Layer 2 Port Security Best Practices on a Cisco Switch In today’s interconnected world, network security is paramount. Cisco switches are the backbone of many [...]
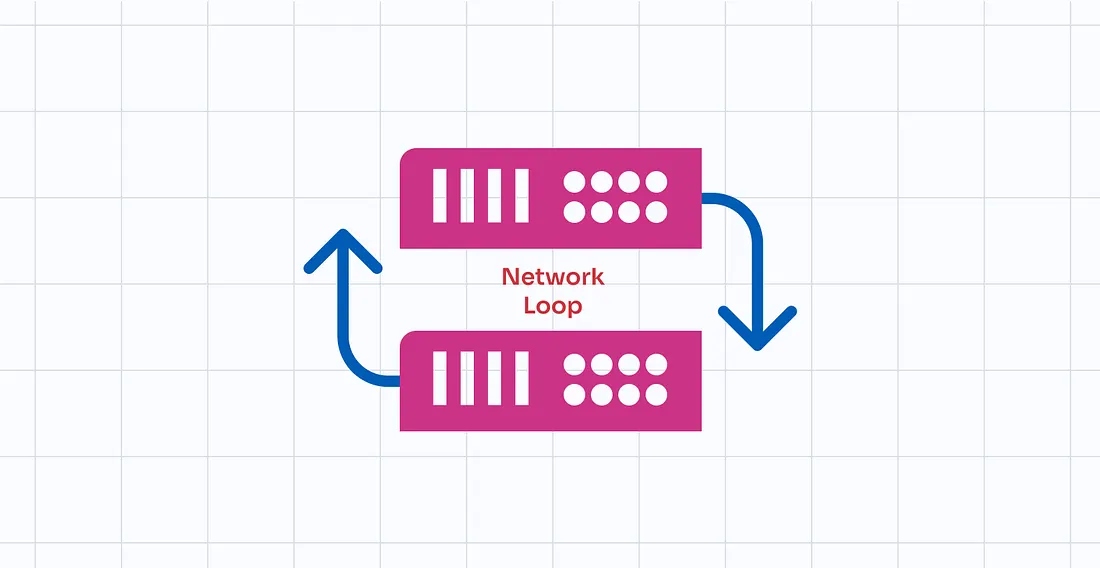
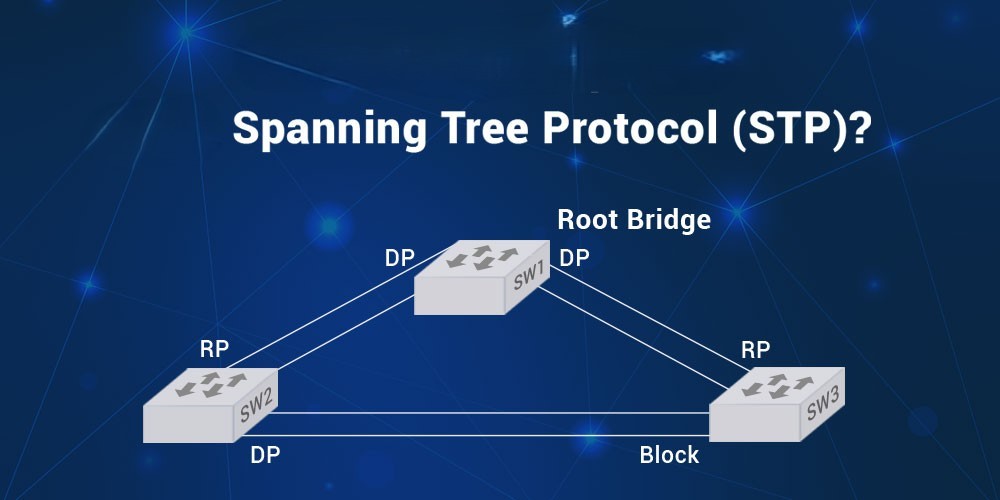
Prevent Network Loops: Spanning Tree Protocol (STP) Solutions At Teamwin Global Technologica, we understand the critical importance of maintaining a stable and efficient network. Network [...]
What is Spanning Tree Protocol (STP): Explained, Cisco & More In the intricate world of network management, ensuring seamless and reliable communication is paramount. The [...]
Configure VLANs on a Cisco Switch: VLAN Configuration Step-by-Step Guide In this step-by-step guide, we will explore how to configure VLANs on a Cisco switch. [...]
VLANs: Simplify & Enhance Improve Network Segmentation for Performance Optimal network performance and security are paramount in today’s complex network environments. VLANs offer a robust [...]
Cisco Switch: Understanding Layer 2 MAC Address Table & How Switches Learn MAC Addresses In the realm of networking, understanding how a Cisco switch operates [...]
What is a Layer 2 vs Layer 3 Switch: Understanding the Differences Between Layer 2 and Layer 3 Network Switches. In the realm of computer [...]
How to Configure Trunk Ports on L2 Switches: Switchport Mode Guide In today’s network environments, understanding and configuring trunk ports on Layer 2 (L2) switches [...]
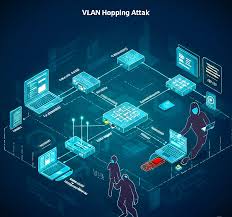
Mitigating VLAN Hopping Attack: Best Practices for VLAN Security and How to Prevent Them In today’s interconnected digital landscape, ensuring robust network security is paramount. [...]
Understanding Network Switch Forwarding and Filtering In the realm of network engineering, understanding how a network switch forwards and filters data is crucial for efficient [...]