How to Protect Against DDoS Attack Mitigation: Prevent Distributed Denial of Service In today’s digital landscape, Distributed Denial of Service (DDoS) attacks pose a significant [...]
Layer 2 Switching in Campus Network Design In modern network design, understanding the nuances of Layer 2 switching is essential, especially within a campus network [...]
What is BPDU Guard and Why Use it for Filter, Portfast, Root Guard and STP BPDU Guard is a critical feature in network administration, designed [...]
Configure Spanning Tree Protocol (STP): Root Bridge Basics In this article, we delve into the crucial aspects of configuring Spanning Tree Protocol (STP), focusing on [...]
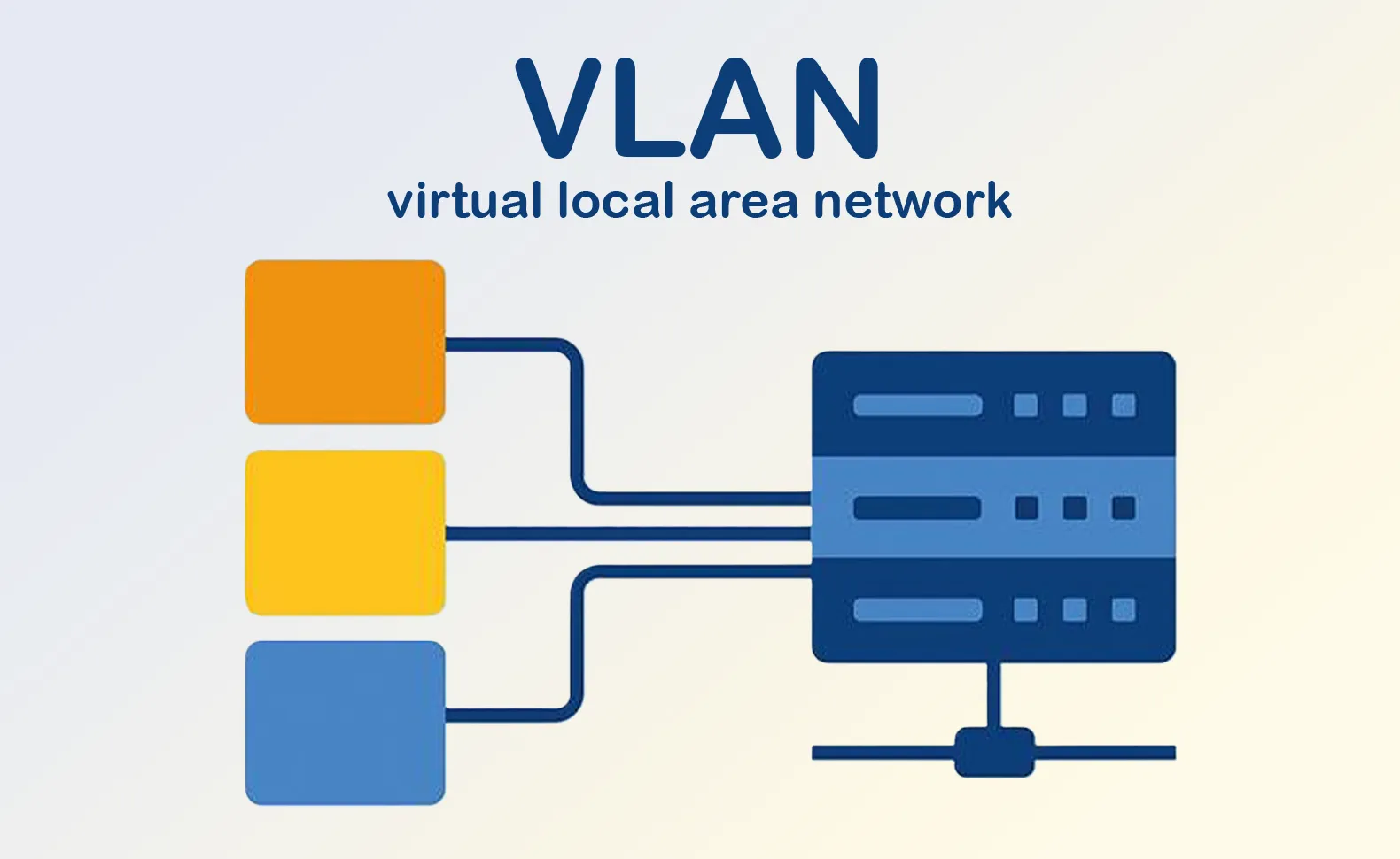
Troubleshoot Native VLAN Mismatch on Your Switch A A native VLAN mismatch can lead to significant issues in the network. on your switch can cause [...]
Layer 2 Network Redundancy Techniques with Switches In modern computer networks, ensuring high availability and reliability is paramount. Layer 2 network redundancy, achieved through the [...]
Layer 2 Switching in Network Virtualized Environments In today’s complex network environments, understanding layer 2 switching is crucial, especially within network virtualization. This guide aims [...]
Automotive Cybersecurity: Securing in Automotive Systems In today’s increasingly connected world, the automotive industry faces unprecedented challenges in safeguarding vehicle systems against evolving cyber threats. [...]
The Role of AI and Machine Learning in Cybersecurity Threat Detection In today’s digital landscape, where evolving cyber threats pose significant risks to businesses of [...]
Cybersecurity for Government Agencies: Threats & Best Practices In today’s digital age, cybersecurity is paramount for government agencies. These entities manage vast amounts of sensitive [...]