Network Forensics: Examining the Role of Layer 2 and Layer 3 Switches The realm of network forensics is essential for identifying security threats in a [...]
Social Engineering Attacks: Understanding Prevention Tips & What is it? In today’s digital landscape, cybersecurity threats are constantly evolving, and among the most insidious are [...]
Remote Work Force Cybersecurity: Challenges and Solutions The digital landscape has undergone a seismic shift, largely propelled by the increasing prevalence of remote and hybrid [...]
Using Configure Access Control List (ACLs) on Switches for Traffic Filtering – (ACL) Cisco In the realm of network security, Access Control Lists (ACLs) stand [...]
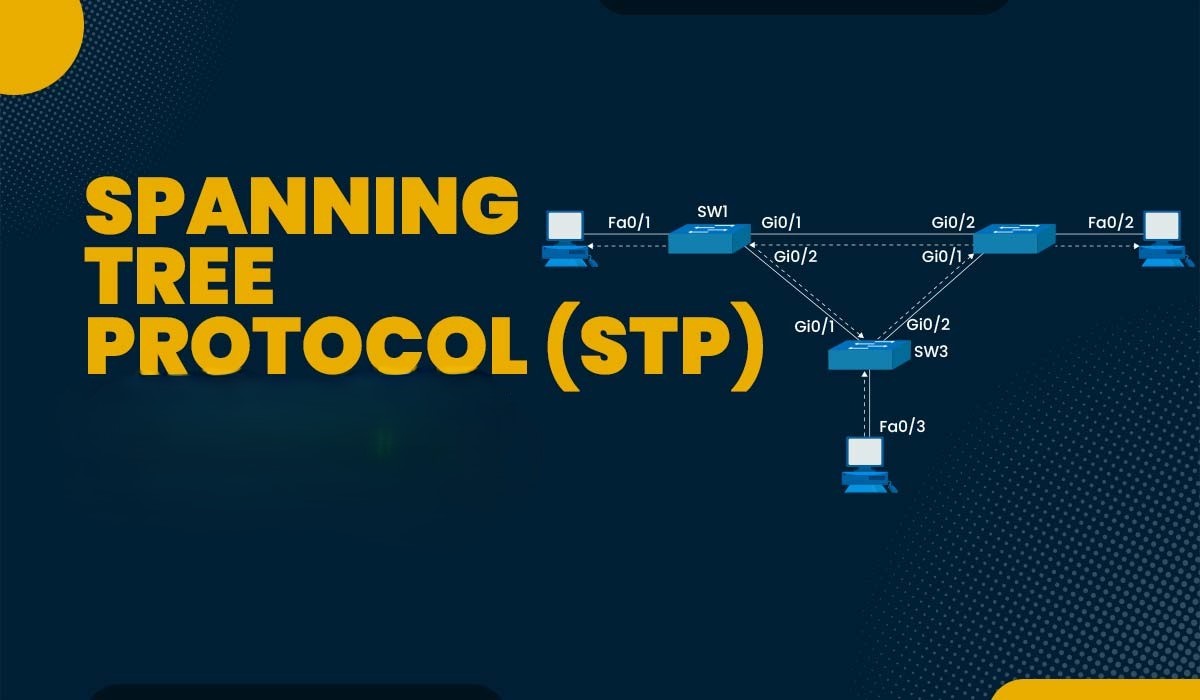
Cybersecurity Implications of STP Security Misconfigurations and Vulnerability Protocol In today’s complex network environments, the Spanning Tree Protocol (STP) plays a crucial role in maintaining [...]
Securing Trunk Links in VLAN Environments: Cisco Network Trunking and VLANs Port Best Practices In today’s complex network environments, securing trunk links is crucial for [...]
Retail Cybersecurity Fortinet FortiGate fg-50g vs Point-of Sale Firewall: Network Security & Threat Protection In today’s digital landscape, network security is paramount. The Fortinet FortiGate [...]
FortiGate Firewall Global Tech Case Studies: Secure Network Performance for Branch Offices In today’s rapidly evolving cybersecurity landscape, securing branch offices presents unique and significant [...]
Modbus TCP Vulnerability in Industrial Control System and OT Protocol Exploits The Hidden Risks In the realm of industrial control systems, securing communication protocols is [...]
Insider Threat Detection: How to Detect and Prevention Prevent Insider Threats In today’s digital landscape, protecting sensitive data from both insider threats and external threats [...]