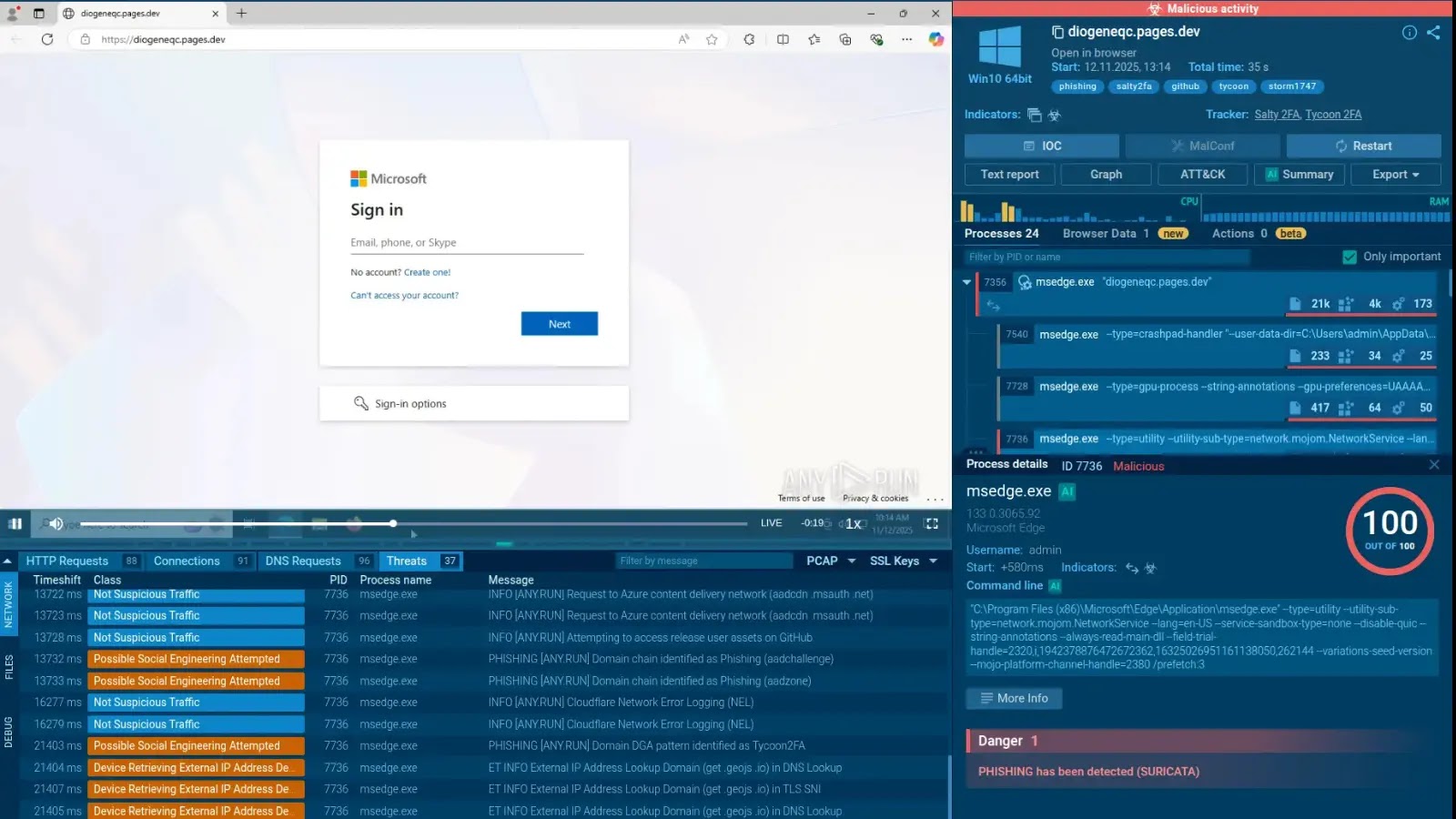
The Evolving Threat: Salty2FA and Tycoon2FA Phishing Kits Converge The landscape of cyber threats is in constant flux, with attackers continuously refining their methodologies. [...]
Cyber Espionage Intensifies: Ukraine-Linked Hackers Target Russian Aerospace and Defense The geopolitical landscape now extends firmly into cyberspace, with nation-state-backed hacking groups actively impacting [...]
The Alarming Rise of Evilginx: Why Your MFA Isn’t as Secure as You Think Multi-factor authentication (MFA) has long been heralded as a critical defense [...]
The Silent Threat: How Your Dash Cam Can Become a Cyber Weapon Dash cams have evolved from niche gadgets to ubiquitous safety devices, offering crucial [...]
Insider threats represent one of the most insidious and challenging security dilemmas any organization faces. Unlike external attacks, they originate from within, often leveraging legitimate [...]
ChatGPT Down: Unpacking the Worldwide Outage and Disappearing Conversations Early Wednesday morning, millions of users globally experienced a significant disruption to their workflows as ChatGPT, [...]
In the constant arms race between security researchers and malicious actors, an unexpected challenger emerges from the depths of your daily browsing: your web browser. [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Surge in Attacks Targeting Palo Alto Networks Devices Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: Critical Overview [...]
The travel and hospitality sector, a prime target for cybercriminals due to its vast repositories of sensitive customer data, is increasingly prioritizing robust cybersecurity measures. [...]
Imagine your Android device, a tool you rely on daily, silently compromised, its defenses bypassed by unseen threats. This isn’t a hypothetical scenario; it’s the [...]