A significant security alert has been issued for developers leveraging Next.js and React Server Components, as Vercel, the company behind Next.js, has disclosed and patched [...]
The cybersecurity landscape has once again been shaken, this time by a critical vulnerability in Palo Alto Networks’ PAN-OS. The Cybersecurity and Infrastructure Security Agency [...]
The digital landscape is a constant battleground, and for organizations relying on mobile endpoint management, a recent development demands immediate attention. Ivanti has disclosed a [...]
A new, high-severity vulnerability in Cisco’s critical network management solutions, Crosswork Network Controller (CNC) and Network Services Orchestrator (NSO), has been disclosed. Tracked as CVE-2026-20188, [...]
The Allure of AI: How Deceptive Claude Installers Are Delivering Malware The rapid advancement and widespread adoption of artificial intelligence tools, particularly large language models [...]
The Shifting Sands of Phone Scams: How Attackers Outsmart Reputation-Based Blocking The arms race between cybercriminals and cybersecurity defenses is never-ending. While enterprises invest heavily [...]
Urgent Alert: WatchGuard Agent Vulnerabilities Grant SYSTEM Privileges on Windows The digital landscape demands constant vigilance, and recent disclosures from WatchGuard underscore this reality. Critical [...]
Unmasking the Critical Redis Vulnerabilities: A Path to Remote Code Execution Redis, the popular open-source, in-memory data store, is a cornerstone for countless applications requiring [...]
Urgent Alert: Palo Alto Networks Firewall Zero-Day RCE Under Active Exploitation The cybersecurity landscape has been rocked by the disclosure of a critical zero-day vulnerability [...]
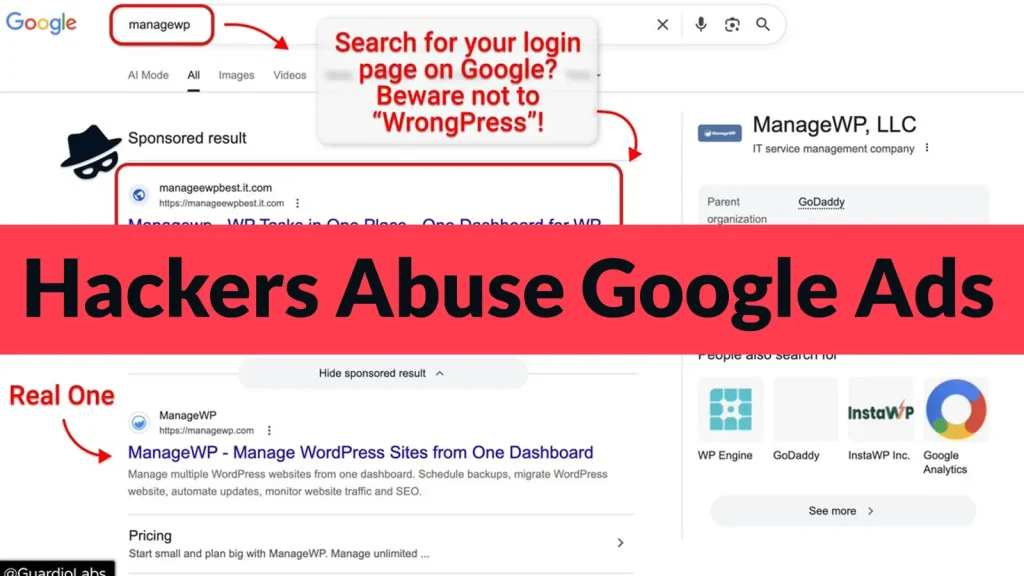
The digital landscape is a battleground, and even seemingly trusted channels can become vectors for attack. A recent campaign, dubbed “WrongPress,” highlights a critical vulnerability [...]