Microsoft Links Ongoing SharePoint Exploits to Three Chinese Hacker Groups The digital battleground continues to evolve, and recent intelligence from Microsoft underscores the scale [...]
The allure of a half-priced luxury vacation is undeniable. Imagine five-star hotels, round-trip flights, and even exclusive yacht charters at a fraction of their advertised [...]
In the relentless battle against cyber threats, actionable threat intelligence is the ultimate force multiplier for any Security Operations Center (SOC). It’s the difference between [...]
The Silence Before the Storm: Iran’s Cyber Espionage Against Global Airlines Unmasked The global aviation industry, a cornerstone of international commerce and personal travel, operates [...]
CISA Warns of Interlock Ransomware With Double Extortion Tactics Attacking Windows and Linux Systems
The cybersecurity landscape is under constant siege, and a new, urgent warning from leading federal agencies underscores the escalating threat. The Cybersecurity and Infrastructure [...]
Urgent Apache Jena Vulnerabilities: A Critical Threat to Data Integrity The integrity of data infrastructure is paramount for any organization. When critical components are [...]
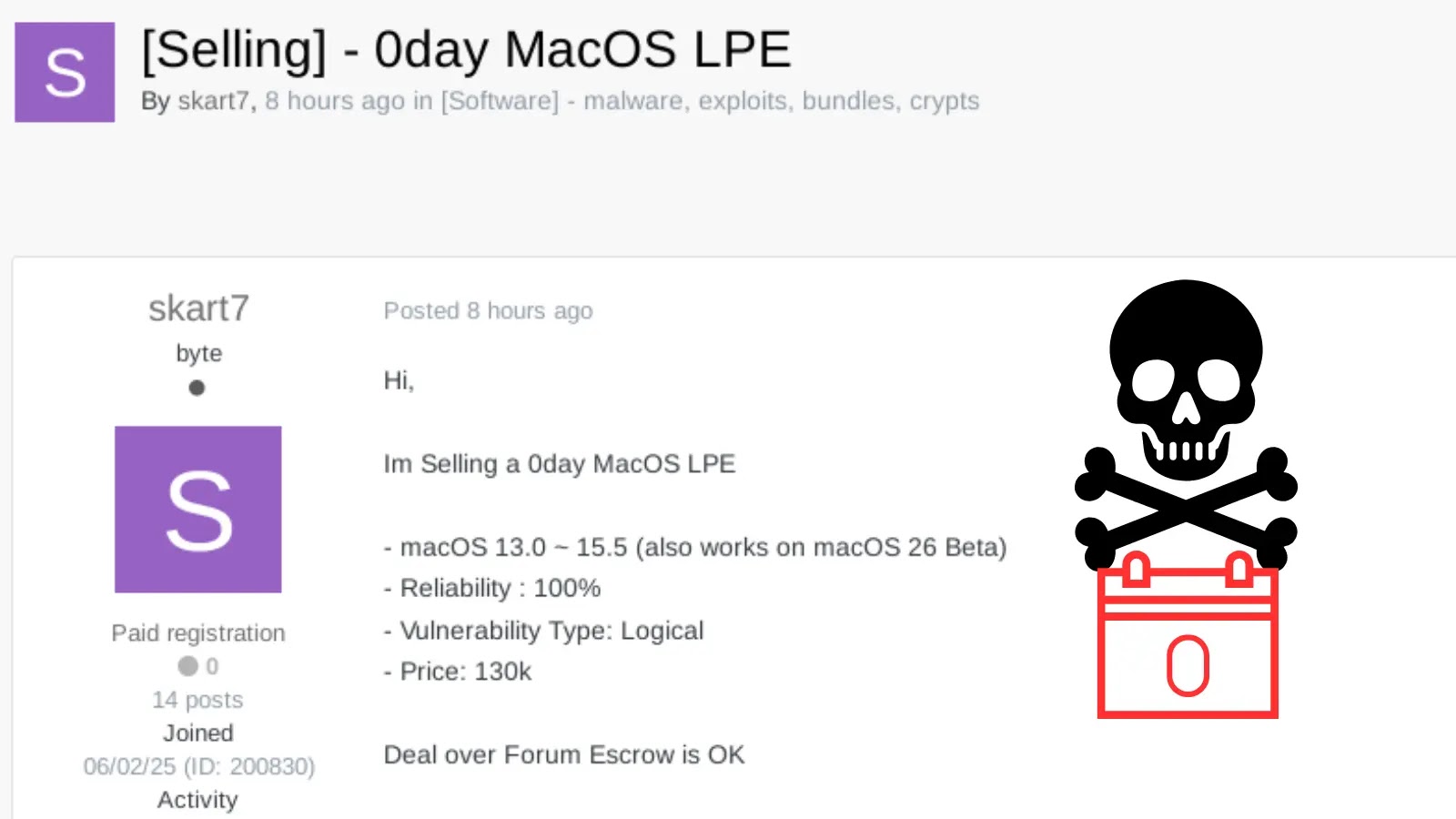
A disturbing development has surfaced in the underground cybercrime landscape: a threat actor, operating under the moniker “skart7,” is reportedly offering a zero-day Local [...]
The One-Space Vulnerability: How a Typo Grants Full System Access in ETQ Reliance Imagine a scenario where a single, seemingly innocuous character could unlock [...]
Urgent Action Required: New Scanner Detects SharePoint Servers Vulnerable to Critical 0-Day Exploit The cybersecurity landscape has been rocked by the discovery of an [...]
The landscape of cybersecurity defense is undergoing a significant strategic evolution, particularly in the United Kingdom. Recent announcements from the UK government confirm a [...]