Endpoint Management And Security : Key To Handling And Securing Future IT Operations Endpoint management and security is not one of the top areas of discussion [...]
Securing Your Digital World: The Latest in Cybersecurity Innovations The importance of robust cybersecurity measures cannot be overstated in the digital age. As technology advances, [...]
Reflectiz Introduces AI-powered Insights on Top of Its Smart Alerting System Reflectiz, a cybersecurity company specializing in continuous web threat management, proudly introduces a new [...]
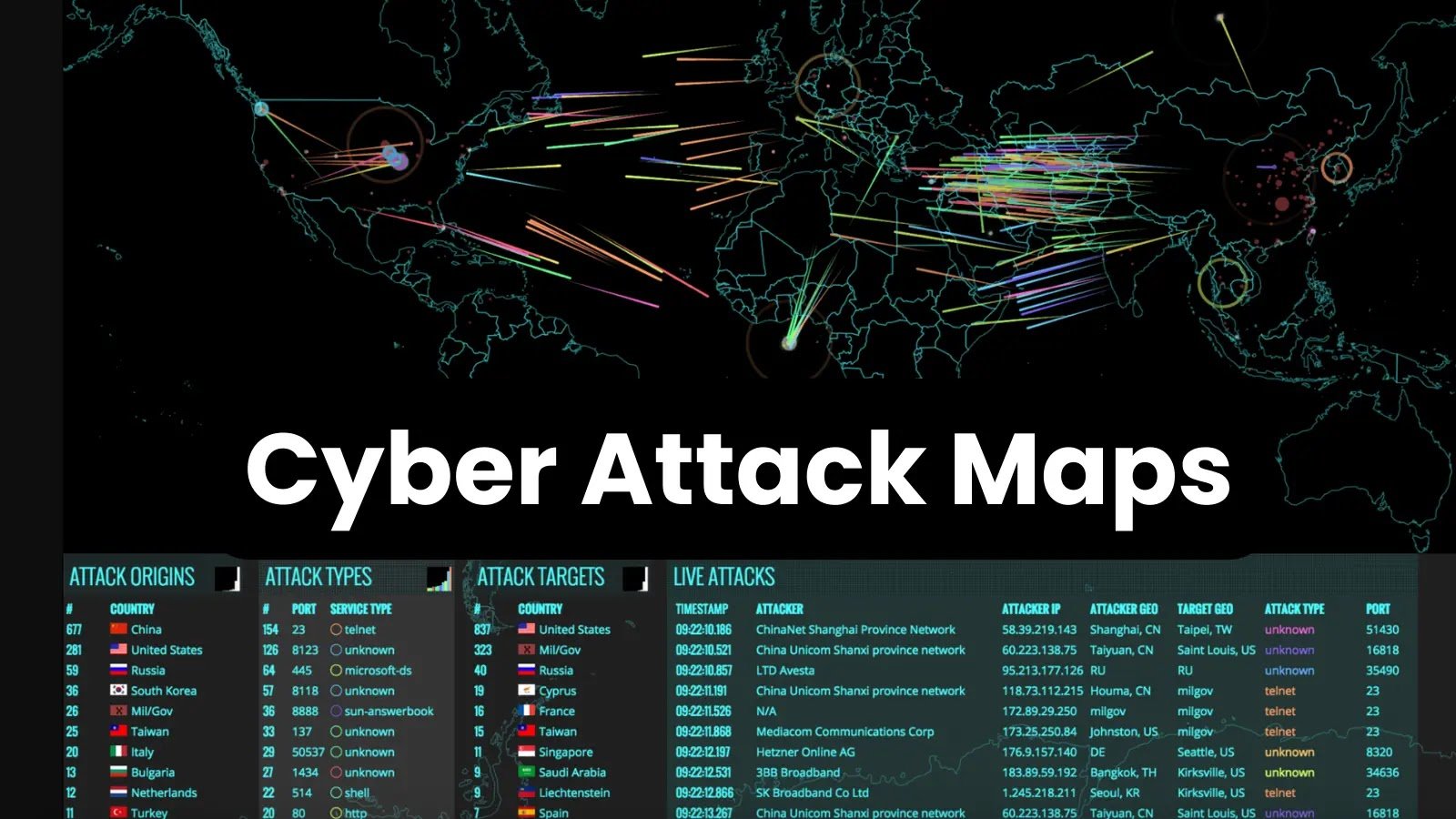
Top 10 Cyber Attack Maps to See Digital Threats In 2024 Cyber attack maps are visual representations or interactive tools that provide real-time or historical [...]
What is SSL and Why it is Important? The protocols SSL (Secure Sockets Layer) and TLS (Transport Layer Security), are used to create secure connections [...]
Unleashing the Potential of IoT Devices with WiFi 6 and Smart Switches The combination of WiFi 6 and smart switches can indeed unlock the full [...]
The Evolution of Firewall Technology: Past, Present and Future Past: Early Firewall Technology (1980s-1990s) Packet Filtering: The earliest form of firewalls involved packet filtering, where [...]
Loader Malware Steal Sensitive System Data & Installs Other Malware In the intricate dance of cybersecurity threats, loader malware emerges as a silent force, discreetly [...]
What are some top tools and technologies used in IT services? There are Several tools and technologies were widely used in the field of IT [...]
To effectively navigate the complex landscape of Active Directory disaster recovery planning, organizations must establish comprehensive strategies that encompass backup and restoration procedures, proactive monitoring [...]