Unmasking RoguePilot: When GitHub Copilot Turns Against You The lines between developer assistance and potential exploit are blurring. Recent findings by the Orca Research [...]
Malicious NuGet Packages: A Silent Threat to ASP.NET Application Security The digital landscape demands vigilance, and recent events highlight a concerning trend: supply chain attacks [...]
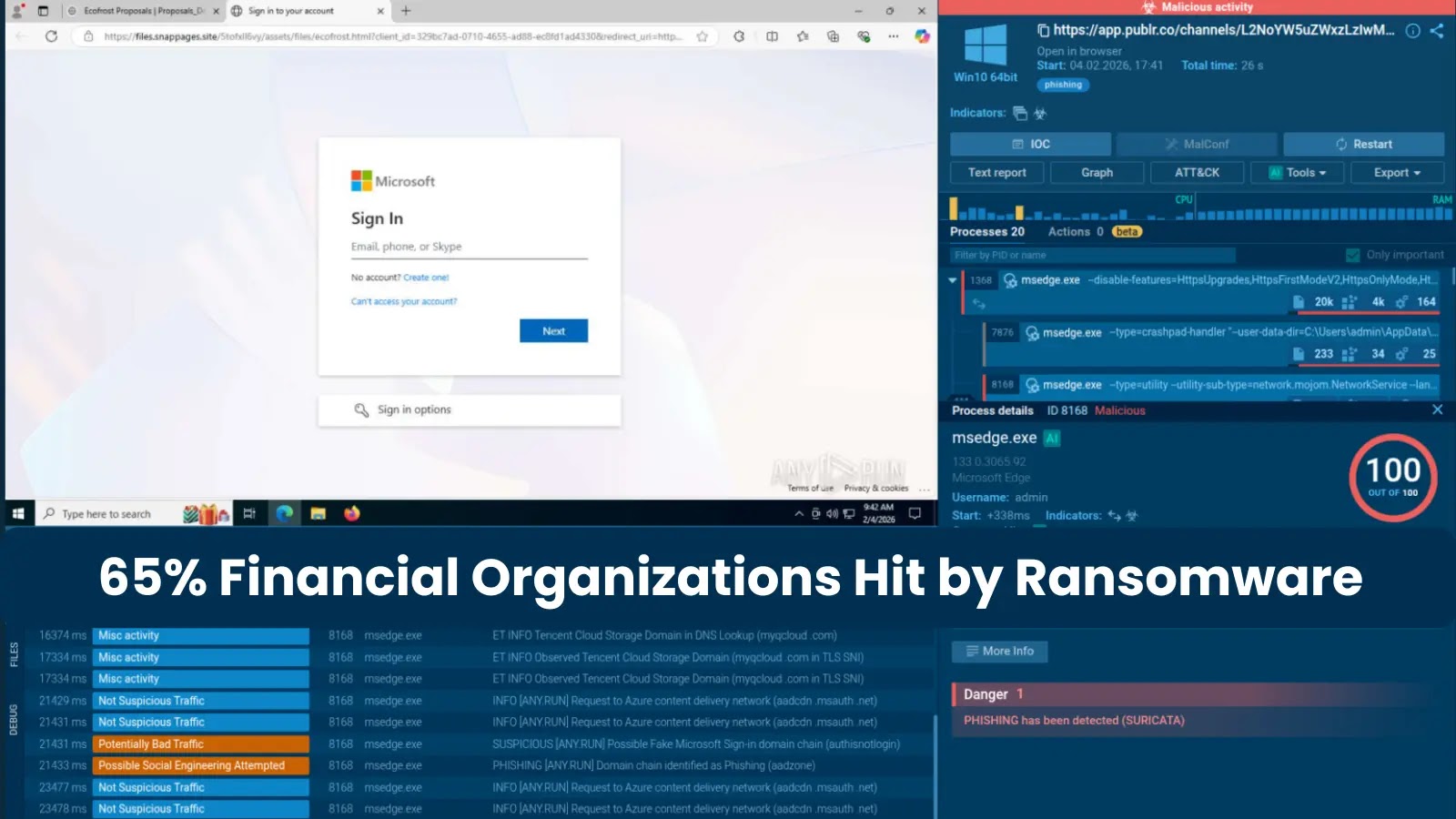
The Ransomware Reckoning: Why Financial Institutions Are Cybercriminals’ Gold Mine The financial sector isn’t just about money; it’s the bedrock of our economic stability, entrusted [...]
In a concerning evolution of cyber threats, the notorious Atomic macOS Stealer (AMOS) has adopted a new, insidious tactic to compromise users. Previously relying on [...]
The digital landscape is a constant battleground, and even the most robust systems can harbor hidden weaknesses. A recent discovery has sent ripples through the [...]
The digital playgrounds of children are increasingly becoming a battleground for privacy. A recent and significant development highlights this concern: Reddit, one of the internet’s [...]
The digital supply chain is under constant threat. Attackers are perpetually refining their methodologies, seeking novel ways to circumvent robust security defenses. A recent, concerning [...]
A Deceptive Huorong Download Site Poisons Users with Valley RAT In a concerning development for cybersecurity, a sophisticated phish has emerged, leveraging a meticulously crafted [...]
Diesel Vortex Russian Cybercrime Group Targets Global Logistics Sector and Steals 1,600+ Credentials
Diesel Vortex: Russian Cybercrime Group Targets Global Logistics, Steals 1,600+ Credentials The global logistics sector, the intricate network that underpins international commerce, has once again [...]
Organizations worldwide rely on VMware Aria Operations to manage their cloud infrastructure efficiently. However, a recent disclosure from Broadcom has cast a critical spotlight [...]