The VexTrio Menace: Malicious VPN Apps Hijacking Google Play and App Store In an alarming development for mobile security, the notorious VexTrio traffic distribution [...]
The AI-Powered Phishing Epidemic: Brazilian Scams Leverage DeepSite AI and BlackBox AI for Credential Theft The landscape of cybercrime is shifting, and threat actors [...]
In a significant victory against the relentless tide of cybercrime, the U.S. government has announced the successful dismantling of the BlackSuit ransomware operation. This [...]
Unpacking Danger: PyPI’s Stand Against ZIP Parser Confusion Attacks on Python Package Installers The integrity of the software supply chain is paramount. In the [...]
Leaked Credentials Soar 160%: The Silent Threat Fueling Breaches Imagine a lock on your most valuable assets, a lock you believed to be secure. [...]
The Silent Threat: RubyGems Malware Weaponizes 60+ Packages to Steal Credentials The digital landscape is a constant battleground, and threat actors continually evolve their [...]
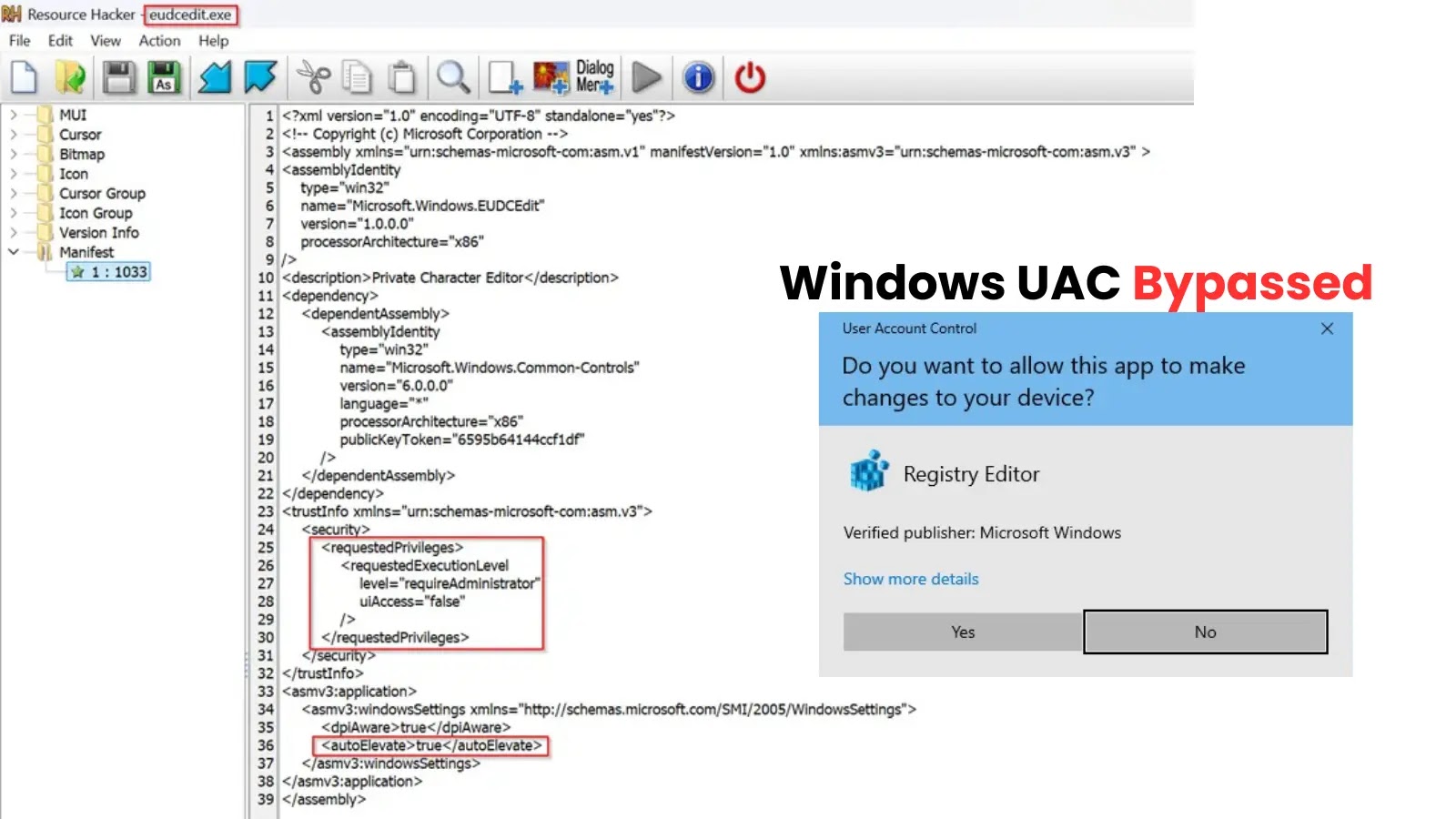
Unmasking the UAC Bypass: Private Character Editor Exploited for Privilege Escalation System administrators and cybersecurity professionals globally are no stranger to the persistent challenge [...]
The Silent Menace: Threat Actors Weaponizing Malicious Go Packages Supply chain attacks represent a critical and escalating threat in the cybersecurity landscape. Unlike traditional [...]
The digital frontier of cryptocurrency, while promising immense innovation, also presents a fertile ground for sophisticated cyberattacks. Imagine logging into your trusted crypto wallet, only [...]
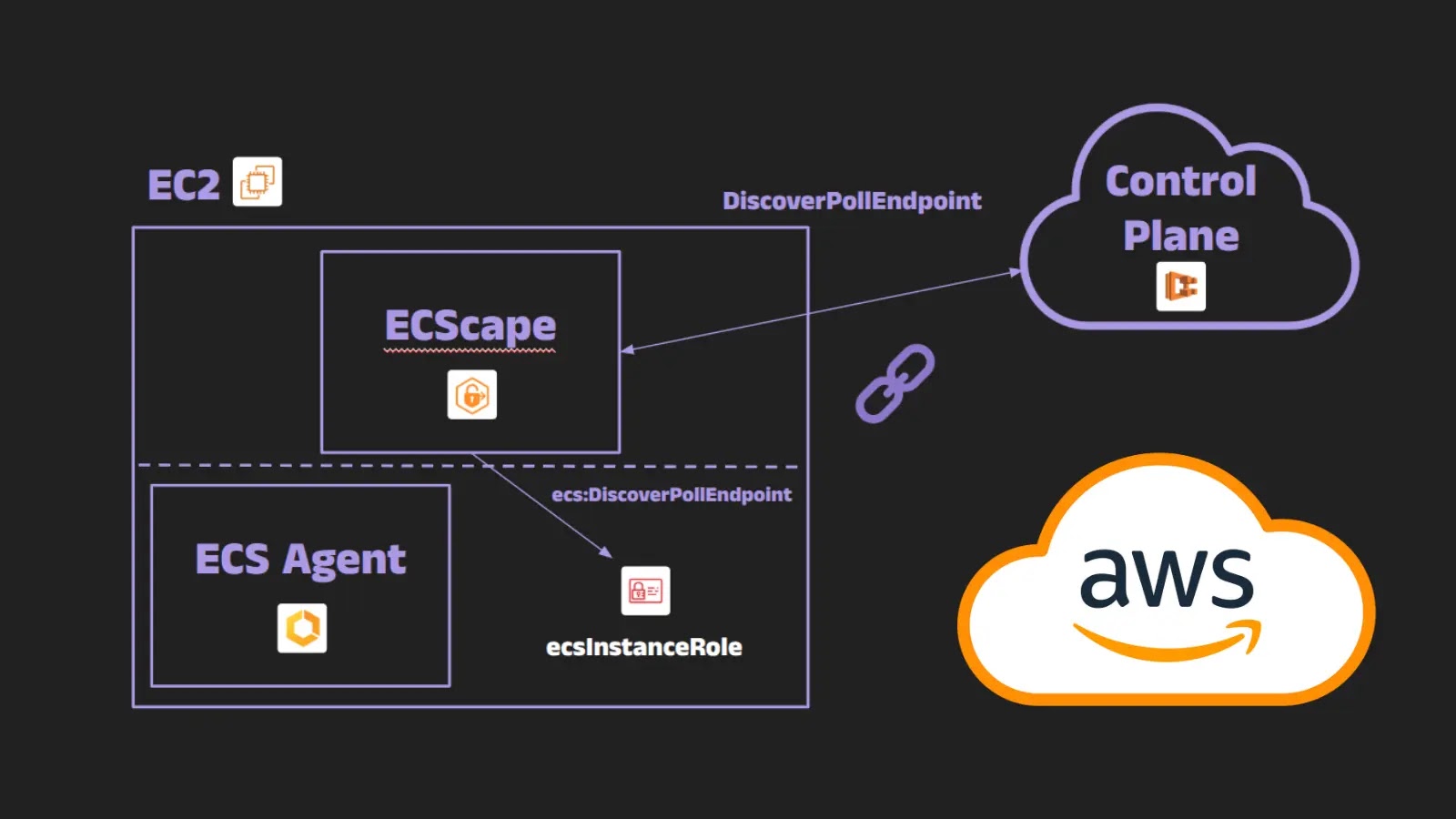
Cloud environments offer unprecedented scalability and flexibility, but they also introduce complex security challenges. A recent discovery, dubbed “ECScape,” highlights a significant vulnerability within [...]