In a stark reminder of the relentless pace of cyberattacks, a critical vulnerability dubbed React2Shell is being actively exploited, allowing attackers to compromise web [...]
The Stealthy Threat: Fake Gemini npm Package Targets AI Developers with Token Theft In the rapidly evolving landscape of artificial intelligence, developers are increasingly [...]
The Looming Threat: Kubernetes Misconfigurations as a Gateway to Cloud Accounts Kubernetes, the de facto standard for managing containerized applications, offers unparalleled scalability and [...]
The digital perimeter of critical infrastructure, particularly within global telecommunications, faces a constant barrage of sophisticated threats. Among these, Linux backdoors represent a particularly [...]
Unmasking the Critical CUPS Vulnerability Chain: Root Privileges at Risk The Common Unix Printing System (CUPS), a ubiquitous component in Unix-like operating systems, is [...]
In a development that underscores the evolving landscape of cybersecurity and the increasing prowess of artificial intelligence, a critical remote code execution (RCE) vulnerability within [...]
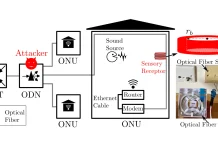
Imagine your critical conversations, the ones you deemed secure within the confines of your office or home, being effortlessly captured by an invisible adversary. Not [...]
A disturbing new cyber threat has emerged, leveraging a sophisticated social engineering scheme dubbed “ClickFix” to deploy a potent Node.js-based Remote Access Trojan (RAT) on [...]
The digital perimeter of our homes and small offices is under siege. Recent intelligence reveals a sophisticated and expansive campaign orchestrated by Forest Blizzard, a [...]
In the quiet corners of the internet, a persistent and financially motivated threat actor has been operating under the radar for over two years, leveraging [...]