—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in Google Chrome for Desktop Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Software Affected [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in Drupal Core Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: Critical Software Affected Drupal 11.3.x [...]
The Silent Threat: How MSHTA Becomes a Malware Delivery Vehicle for LummaStealer and Amatera In the evolving landscape of cyber threats, attackers constantly seek [...]
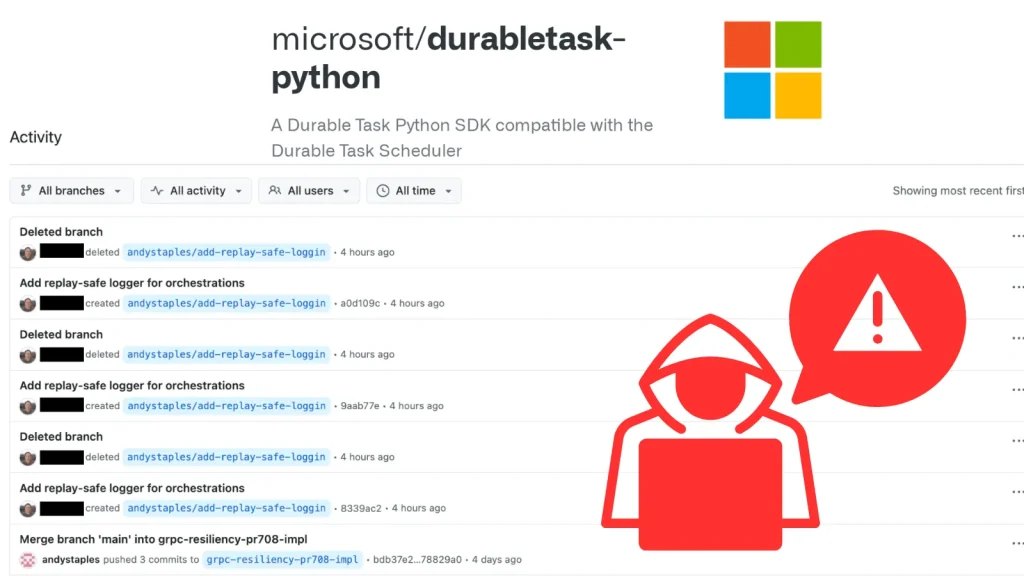
The Shadow Over DurableTask: TeamPCP’s Supply Chain Attack on Microsoft’s Python Client The digital supply chain remains a prime target for sophisticated threat actors, and [...]
The Deceptive Cloak: Fox Tempest Abuses Microsoft Artifact Signing to Certify Malware The digital landscape is a constant battleground, where the lines between legitimate [...]
Unmasking GraphWorm: How Nation-State Actors Weaponize Microsoft OneDrive The cybersecurity landscape shifts constantly, and sophisticated threat actors are at the forefront of these evolutions. [...]
Microsoft Addresses Critical BitLocker 0-Day: A Deep Dive into the “YellowKey” Bypass Data breaches often begin with physical access, a chilling reality reinforced by [...]
Urgent NGINX Vulnerability: Unauthenticated Attackers Can Trigger Remote Code Execution A critical new vulnerability, tracked as CVE-2026-8711, has been discovered in NGINX’s JavaScript (njs) [...]
GitHub Confirms Internal Repository Breach Via Compromised Employee Device The integrity of internal development environments is paramount for any organization, especially for platforms as critical [...]
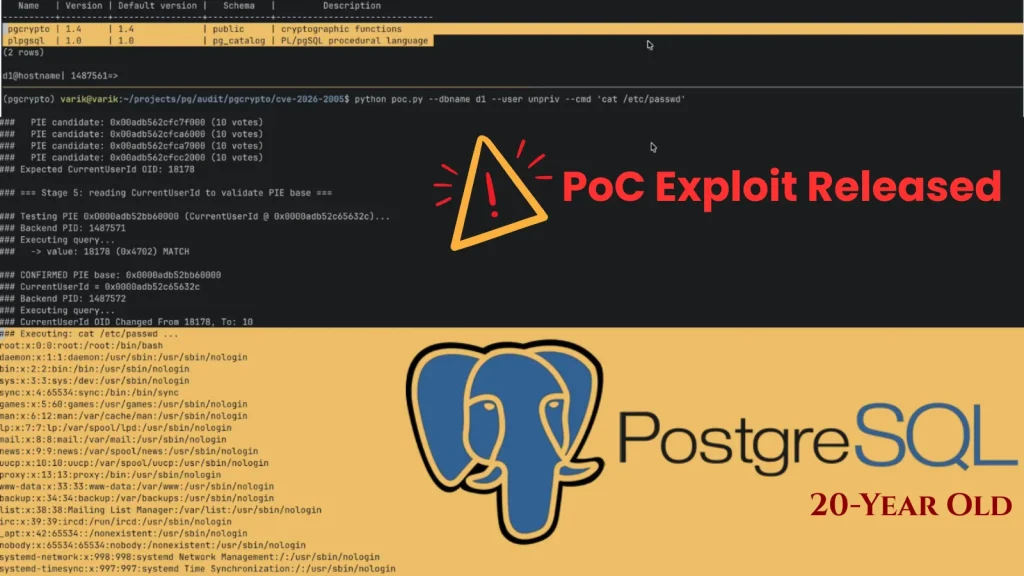
The Ghost in the Machine: 20-Year Old PostgreSQL RCE Vulnerability Awakens with Public Exploit Databases are the lifeblood of modern applications, and PostgreSQL stands as [...]