ShinyHunters Strikes: A Deep Dive into the LMS Cyberattack The digital backbone of education recently suffered a significant blow when the notorious cybercriminal collective, ShinyHunters, [...]
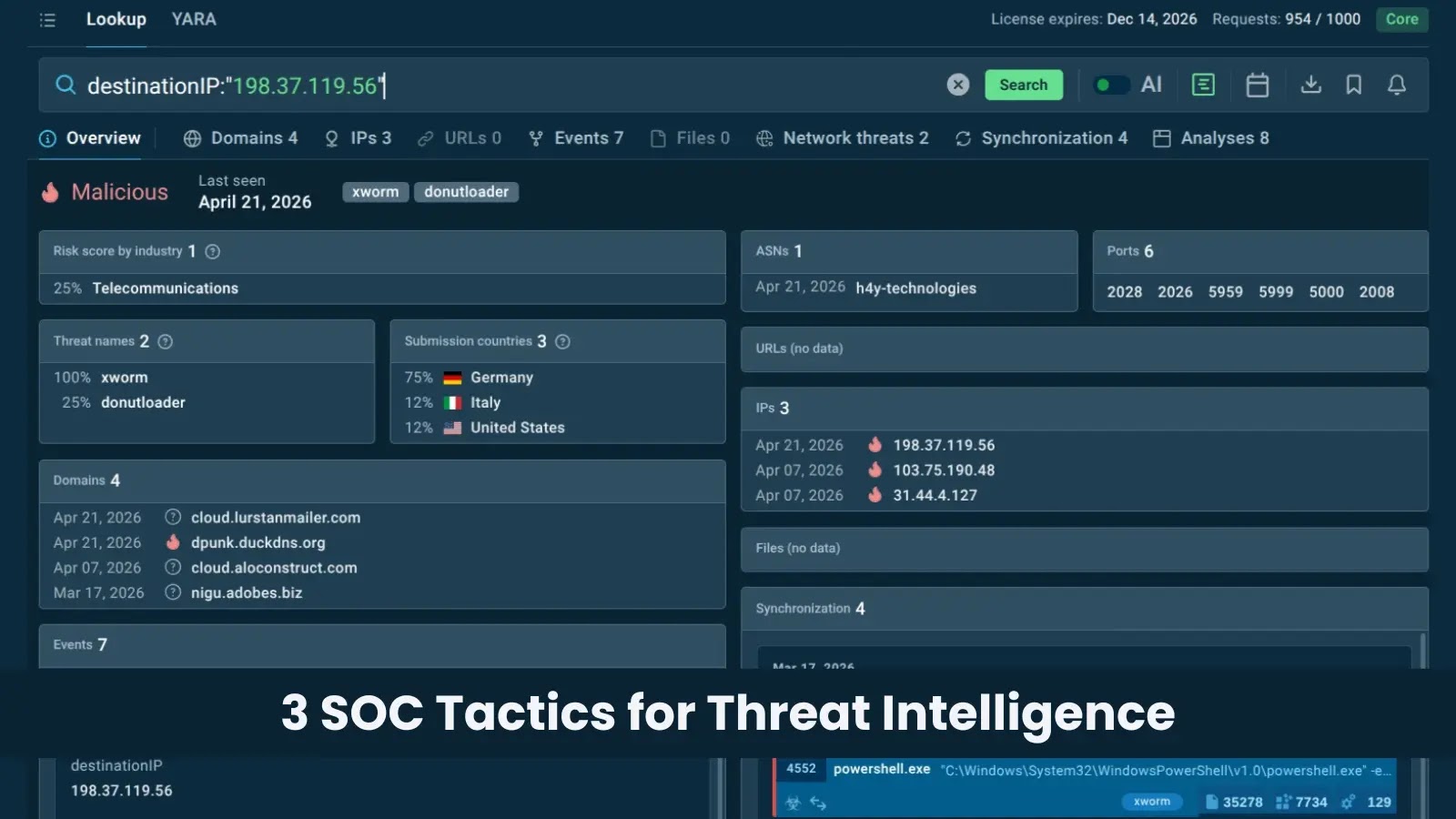
The cybersecurity landscape is a relentless battlefield, with threat actors continually refining their tactics. For organizations striving to defend their digital assets, access to timely, [...]
Unveiling Elite SOC Strategies: Operationalizing Threat Intelligence for Proactive Defense A data breach can dominate headlines for a day, but the damage it inflicts reverberates [...]
In a powerful demonstration of international cooperation against cybercrime, law enforcement agencies across the Middle East and North Africa (MENA) region recently dismantled a sprawling [...]
Unmasking the Threat: Compromised GitHub Action Exfiltrates Workflow Credentials The security landscape for software development teams has just confronted a concerning incident. A widely utilized [...]
A significant security alert has been issued for PostgreSQL, the world’s most advanced open-source relational database. The PostgreSQL Global Development Group has recently rolled out [...]
Navigating the Storm: Critical Apache Flink Vulnerability Exposes RCE Threats In the complex landscape of distributed data processing, swift and secure operations are paramount. However, [...]
The quiet hum of industrial operations relies heavily on robust and secure networking infrastructure. Unfortunately, a recent and alarming trend reveals this foundational security is [...]
In the evolving landscape of cyber threats, the stealthy exfiltration of cryptocurrency remains a persistent and lucrative target for malicious actors. Recent discoveries reveal [...]
North Korea-linked threat actor Kimsuky is actively leveraging sophisticated spear-phishing campaigns, utilizing LNK and JSE lures, to target high-value individuals across various critical sectors. [...]