Popular PyPI Package With 1 Million Monthly Downloads Hacked to Inject Malicious Scripts
Software Supply Chain Under Attack: Popular PyPI Package `elementary-data` Compromised
The integrity of the software supply chain has once again been breached, impacting a critical component in the Python ecosystem. A significant cybersecurity incident has come to light, revealing that the widely-used Python package elementary-data, boasting over a million monthly downloads, was compromised. This sophisticated attack involved the injection of malicious scripts, potentially exposing thousands of developers to credential theft and other severe security risks. This incident underscores the urgent need for robust security practices within open-source communities and among developers.
Understanding the Attack Vector: Malicious Version and Docker Poisoning
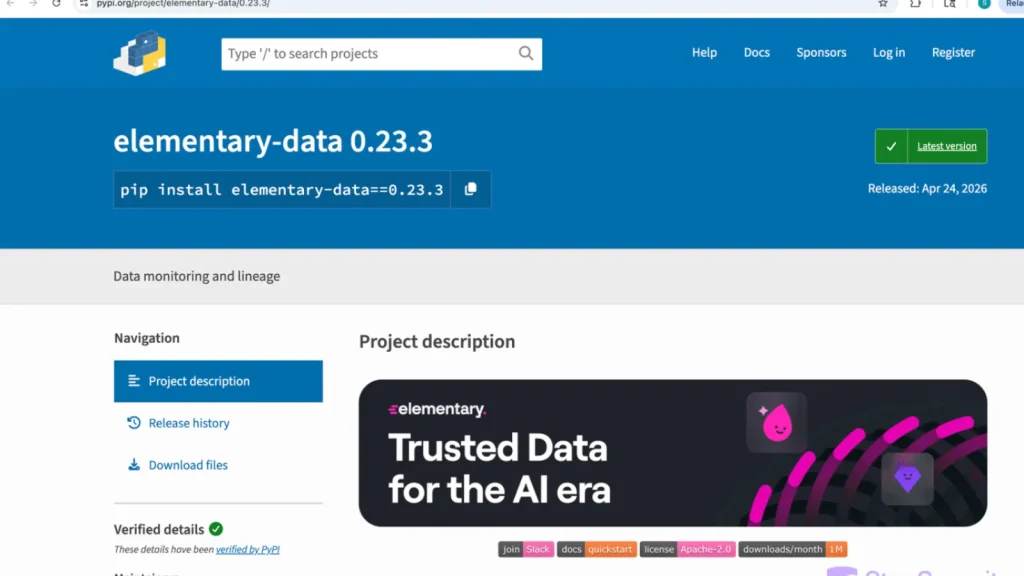
Threat actors executed a multi-pronged attack to maximize their impact. The primary vector involved the malicious version 0.23.3 of the elementary-data package being pushed to the Python Package Index (PyPI). PyPI serves as the official third-party software repository for Python, making any compromise highly impactful due to widespread developer reliance. Developers or automated systems pulling this specific version would inadvertently incorporate the malicious code into their projects.
Beyond the PyPI compromise, the attackers also poisoned matching Docker images on the GitHub Container Registry (GHCR). This secondary vector is particularly insidious as many development and deployment pipelines utilize Docker images for consistency and reproducibility. By injecting malware into these images, attackers ensured that even environments relying on containerized deployments would be at risk, broadening the scope of potential victims and making detection more challenging.
The Threat: Credential Theft and Supply Chain Risk
The primary objective of this attack was likely massive credential theft. Malicious scripts embedded within the compromised package and Docker images could be designed to:
- Exfiltrate API keys, database credentials, and cloud service account tokens.
- Install backdoors for persistent access to developer machines or production environments.
- Insert ransomware or other destructive payloads.
- Manipulate data or interfere with software functionalities.
Such compromises in a popular package like elementary-data have a cascading effect, posing a significant risk to the entire software supply chain. Applications dependent on this package could inherit the malicious code, creating a widespread vulnerability across numerous projects and organizations.
Remediation Actions and Best Practices
Immediate action is crucial for any organization or developer using the elementary-data package. The following steps are strongly recommended:
- Isolate and Audit: Immediately isolate any systems that have downloaded or run
elementary-dataversion 0.23.3 or the corresponding poisoned Docker image. Conduct a thorough audit of all affected environments for unusual activity, suspicious network connections, or unauthorized file modifications. - Update Dependencies: If using
elementary-data, ensure you are running a trusted, clean version. Review the official project page for guidance on verified secure versions. Avoid version 0.23.3 at all costs. - Rotate Credentials: Assume all credentials that might have been exposed through systems using the compromised package are compromised. Immediately rotate all API keys, database passwords, cloud access keys, and other sensitive credentials.
- Implement Software Supply Chain Security:
- Pin Dependencies: Always pin your dependencies to specific, trusted versions (e.g., in
requirements.txtorpackage.json) to prevent automatic upgrades to potentially malicious versions. - Use Content Hashes: Verify the integrity of downloaded packages by checking their cryptographic hashes against known good values.
- Employ Dependency Scanners: Integrate automated tools to scan your project’s dependencies for known vulnerabilities and malicious code.
- Monitor PyPI and other Registries: Stay informed about security advisories related to packages you use.
- Secure Your Build Environment: Ensure your build servers and CI/CD pipelines are hardened and regularly scanned for vulnerabilities.
- Pin Dependencies: Always pin your dependencies to specific, trusted versions (e.g., in
- Educate Developers: Foster a security-aware culture. Educate developers on the risks of supply chain attacks and the importance of verifying package authenticity.
Tools for Detection and Mitigation
Leveraging specialized tools can significantly enhance your ability to detect and mitigate software supply chain risks.
| Tool Name | Purpose | Link |
|---|---|---|
| Dependabot | Automated dependency updates and vulnerability alerts. | https://github.com/dependabot |
| Snyk | Developer security platform for identifying vulnerabilities in code, dependencies, and containers. | https://snyk.io/ |
| OWASP Dependency-Check | Identifies project dependencies and checks if there are any known, publicly disclosed vulnerabilities. | https://owasp.org/www-project-dependency-check/ |
| Trivy | Comprehensive security scanner for vulnerabilities in containers, file systems, and configuration files. | https://aquasec.com/products/trivy/ |
| PyUp.io Safety | Checks your Python dependencies for known security vulnerabilities. | https://pyup.io/safety/ |
Conclusion
The compromise of the elementary-data PyPI package serves as a stark reminder of the persistent and evolving threat landscape in software supply chain security. As development increasingly relies on third-party components, the attack surface expands, making vigilance and proactive security measures paramount. Organizations and developers must prioritize robust dependency management, continuous security scanning, and immediate response protocols to protect against these sophisticated attacks. Staying informed and implementing security best practices are no longer optional but essential for safeguarding digital infrastructure.





