Unpacking GPUBreach: A New Era of GPU-Powered System Compromise The landscape of system security just got significantly more complex with the emergence of GPUBreach, a [...]
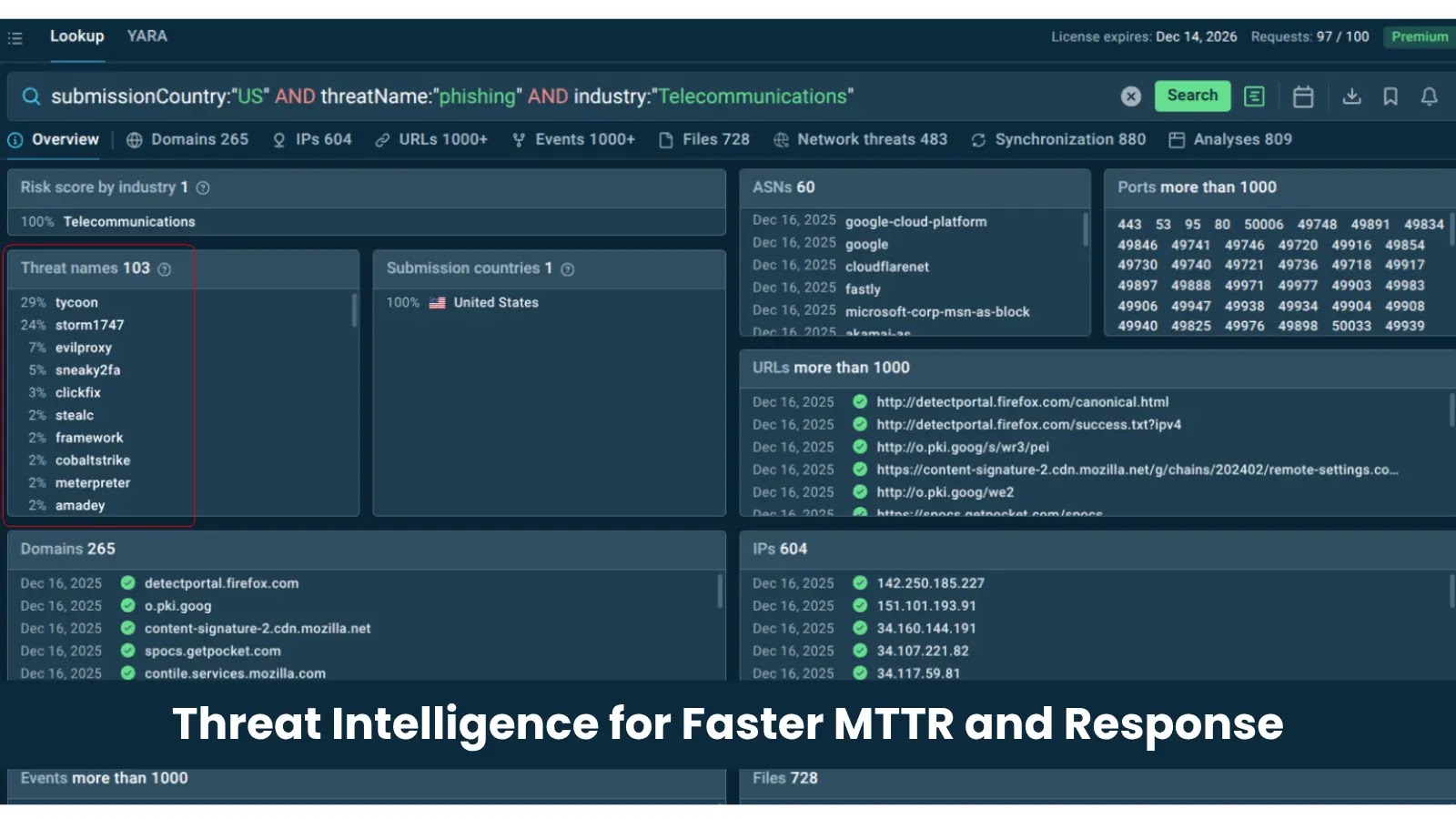
From Alert Overload to Rapid Response: Why Threat Intelligence Is a Top Solution for Fast MTTR Modern Security Operations Centers (SOCs) face a relentless deluge [...]
The digital landscape is a constant battleground, with new threats emerging daily. For Android users and organizations relying on the platform, staying ahead of vulnerabilities [...]
The Deceptive Lure: Threat Actors Weaponize LogMeIn Resolve and ScreenConnect in Multi-Stage Phishing Attacks In a chilling demonstration of evolving cyber tactics, threat actors are [...]
BlueHammer: Exploiting Windows Defender for Privilege Escalation The digital defense landscape faces constant challenges, and the recent public release of “BlueHammer” highlights a critical vulnerability [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Authentication Bypass Vulnerability in SAML SSO Plugin of Drupal Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: CRITICAL [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in Android OS Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: CRITICAL Software Affected Android 14 [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Improper Access Control Vulnerability in FortiClient (EMS) Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: CRITICAL Software Affected [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in ISC BIND Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Software Affected ISC BIND [...]
A disturbing trend has emerged from the Middle East, underscoring the persistent threat of identity-based attacks. Recent intelligence indicates that an Iran-linked threat actor [...]