Apple has taken an unprecedented step, rolling out critical security patches to a wider array of devices still operating on iOS 18. This expansion of [...]
The integrity of the software supply chain is a fundamental pillar of modern cybersecurity. When a widely adopted component is compromised, the ripple effect [...]
A critical alert echoes across the cybersecurity landscape as a severe zero-day vulnerability in Google Chrome has been discovered and, disturbingly, is already being [...]
Unmasking Operation NoVoice: A Deep Dive into Android’s Latest Rootkit Threat The digital landscape for Android users has been shaken by the discovery of [...]
OpenSSH 10.3: Urgent Update Addresses Critical Shell Injection and Security Hardening The digital landscape demands constant vigilance, especially when it comes to foundational services like [...]
A disturbing trend has emerged in the cybersecurity landscape: sophisticated multi-stage malware campaigns leveraging seemingly innocuous document formats. Recently, a stealthy operation targeting industrial [...]
In the relentless cat-and-mouse game of cybersecurity, threat actors constantly adapt their tactics to circumvent our most sophisticated defenses. A recent and particularly alarming development [...]
Cyber Espionage Unveiled: Hackers Clone CERT-UA Site to Deploy Go-Based RAT The digital battlefield is constantly shifting, and sophisticated cyber espionage tactics are a [...]
A perilous new threat has emerged in the cybersecurity landscape, specifically targeting Windows users across South America. A particularly insidious ransomware campaign is now active, [...]
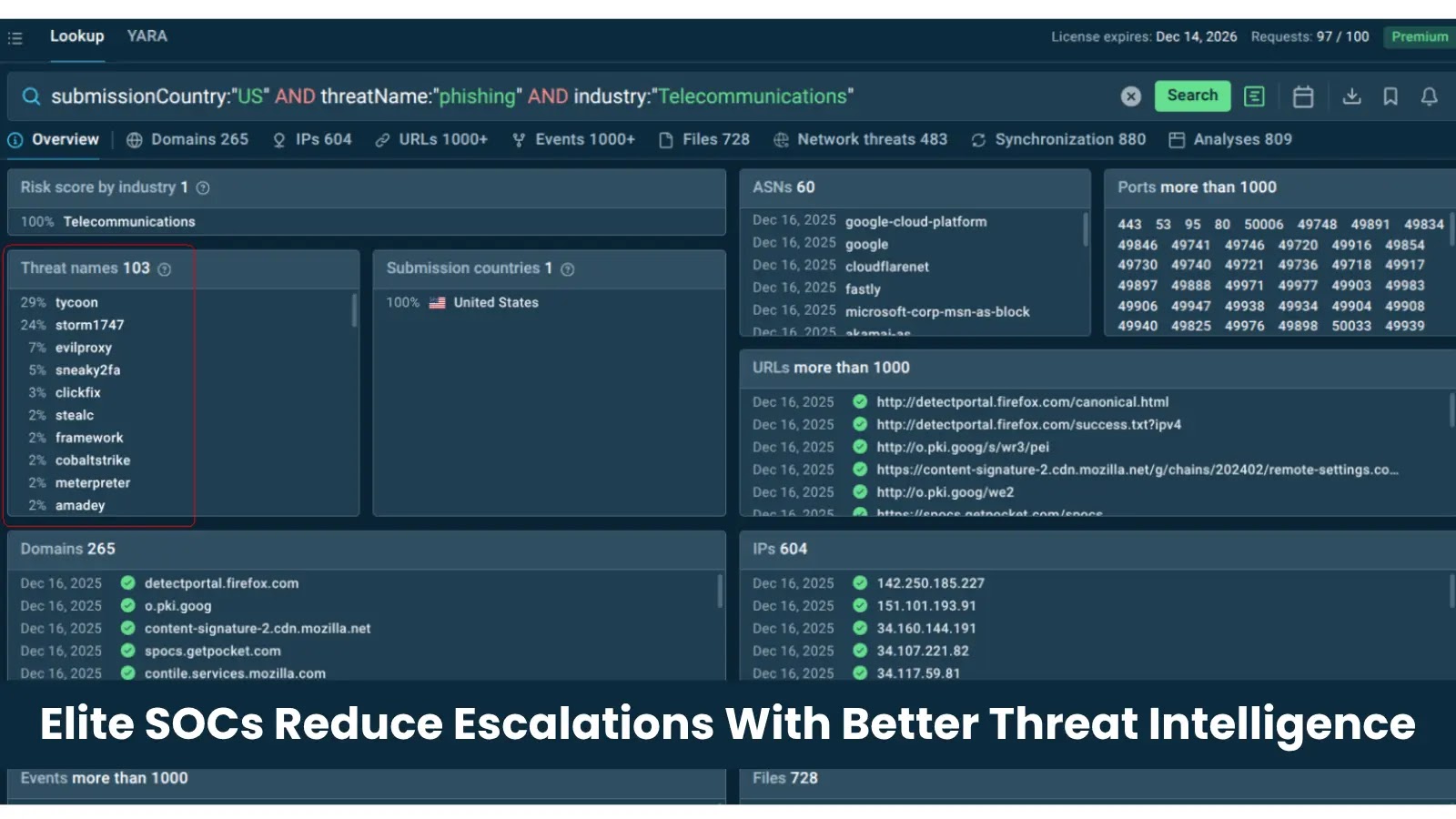
In the high-stakes world of cybersecurity, a Security Operations Center (SOC) is the frontline defense against ever-evolving threats. Yet, even in mature SOC environments, [...]