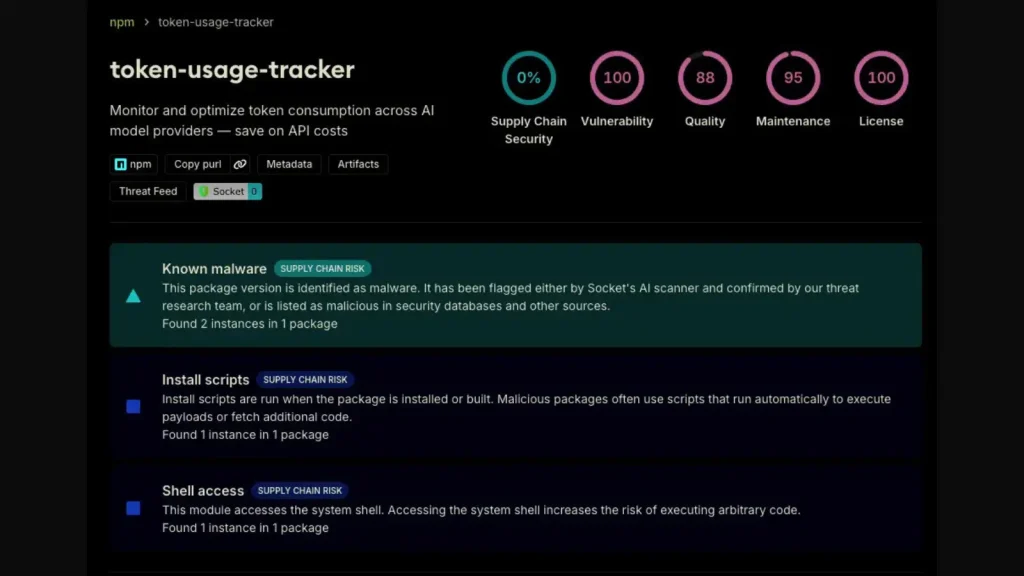
A disturbing new campaign, dubbed “TrapDoor,” has cast a long shadow across the software supply chain, compromising 34 distinct packages and over 384 related [...]
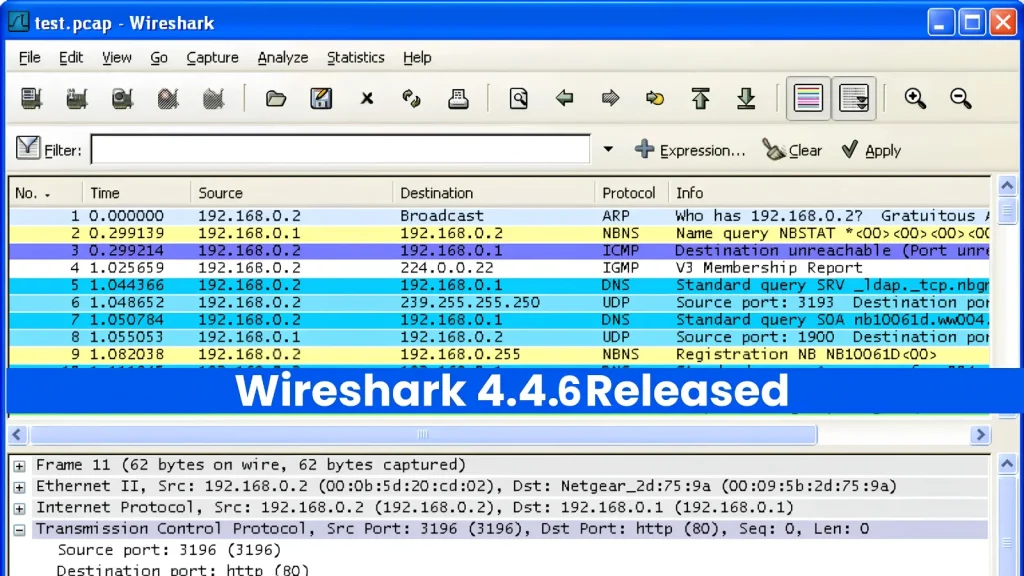
For cybersecurity professionals, network analysts, and developers, Wireshark is an indispensable tool. It’s the magnifying glass for network traffic, allowing deep dives into protocols [...]
The pace of software development, particularly with the integration of AI-powered coding assistants, has surged. While these tools dramatically enhance productivity, they also introduce new [...]
Network administrators and cybersecurity professionals managing Ubiquiti UniFi environments, attention: a critical security alert demands immediate action. Ubiquiti Networks has released urgent security updates to [...]
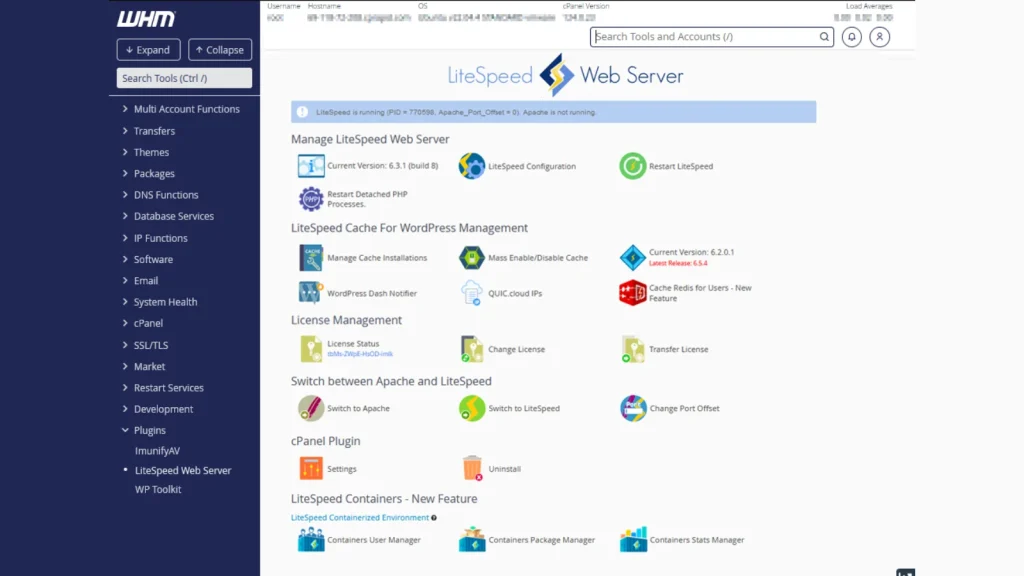
A Critical Alert: LiteSpeed cPanel Plugin 0-Day Actively Exploited for Root Access The cybersecurity landscape remains a dynamic and often precarious environment. Latest intelligence from [...]
In the dynamic landscape of cloud security, ensuring that revoked credentials truly lose their access is paramount. A recent disclosure has sent ripples through the [...]
CISA Sounds the Alarm: Langflow Origin Validation Flaw Under Active Exploitation The cybersecurity landscape just became a little more challenging for organizations leveraging AI-driven workflows. [...]
The Silent Drain: Android Malware Hijacking Premium Subscriptions The digital landscape is a battleground, and a recent campaign underscores the insidious nature of modern cyber [...]
The digital landscape is a constant battleground, and even seemingly innocuous files can harbor sinister intentions. A recent and deeply concerning development in this ongoing [...]
Unmasking KimWolf: The Takedown of a Massive IoT DDoS Botnet Operator In a significant win for international law enforcement, a 23-year-old Canadian national has been [...]