Urgent Alert: Palo Alto PAN-OS 0-Day Under Active Exploitation – Root Privileges at Risk A critical, unauthenticated remote code execution (RCE) vulnerability within Palo [...]
Threat actors relentlessly probe for chinks in our digital armor. For organizations relying on GitLab’s robust platform, a recently disclosed batch of vulnerabilities provides [...]
When Trusted Tools Turn Treacherous: HWMonitor Abused to Deliver STX RAT The digital landscape is a constant battleground, and threat actors are perpetually refining [...]
The AI Paradox: When Security Testing Gets Too Realistic The cybersecurity landscape continuously shifts, often bringing both innovation and unprecedented challenges. One such development, [...]
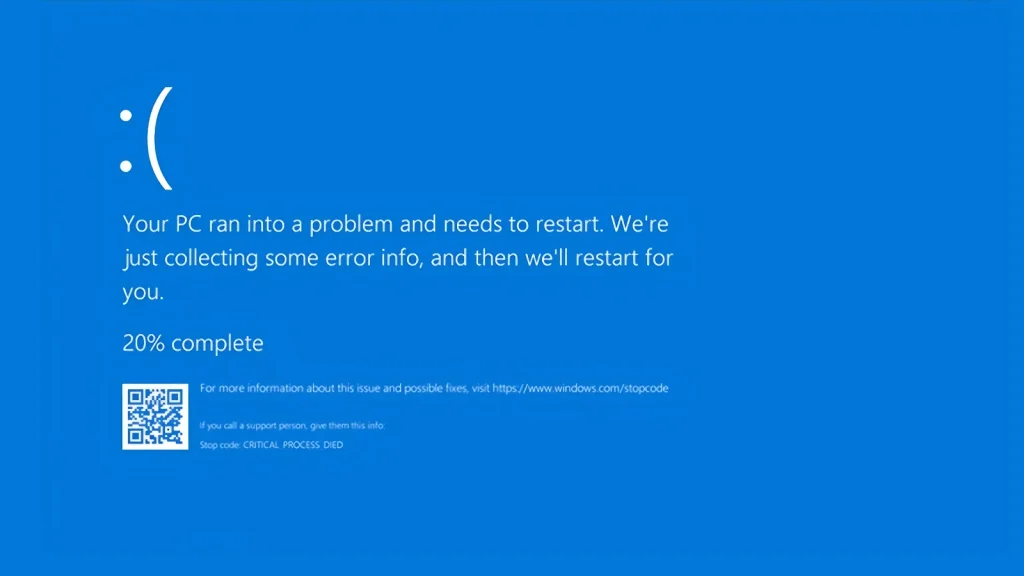
The digital landscape is fraught with potential disruptions, and even routine software updates can harbor significant risks. Recently, a critical situation has unfolded concerning [...]
A severe security flaw has been identified in Exim, one of the most widely deployed mail transfer agents (MTAs) globally. This critical vulnerability, dubbed Dead.Letter, [...]
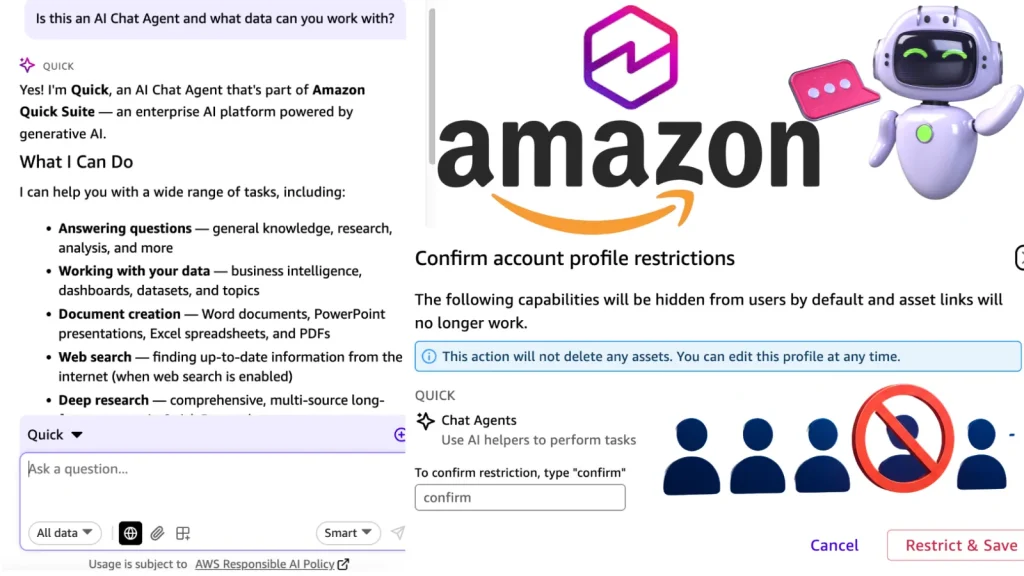
Imagine your organization’s most sensitive data, meticulously guarded within enterprise AI tools. You’ve implemented robust access controls, confident that only authorized personnel can interact with [...]
Critical Canon MailSuite Vulnerability Threatens Enterprise Email Security Enterprise email infrastructure stands as a paramount target for cybercriminals, a critical communication channel often housing [...]
Navigating the npm Supply Chain Crisis: 170 Packages Compromised, Secrets at Risk A sophisticated supply chain attack has sent ripples through the software development [...]
The digital underground is a volatile place, and its latest trend should send shivers down the spine of every organization relying on open-source software. A [...]