Mythos AI Unearths macOS Vulnerabilities: A New Frontier in Security Research The landscape of cybersecurity is perpetually shifting, with adversaries and defenders alike leveraging [...]
Unveiling TencShell: A Potent New Malware Framework Endangering Digital Assets The cybersecurity landscape has been rattled by the emergence of TencShell, a newly discovered [...]
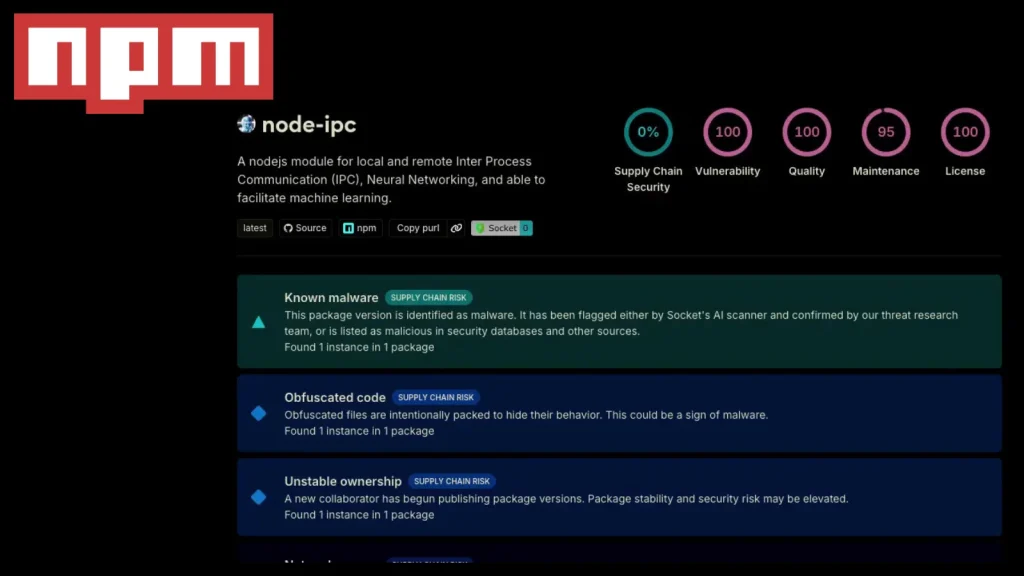
Unpacking the Latest Compromise: Node-ipc Package Hit Again in Supply Chain Attack The digital supply chain continues to be a fertile ground for sophisticated [...]
In a deeply concerning shift, the notorious Russian state-sponsored hacking group, Sandworm, has been observed pivoting its sophisticated cyber operations from traditional Information Technology [...]
Chinese APT Strikes: FamousSparrow Breaches Energy Sector Via Unpatched Exchange In a stark reminder of persistent threats to critical infrastructure, a sophisticated Chinese state-sponsored [...]
OpenAI Confirms Security Incident: A Deep Dive into the TanStack npm Supply Chain Attack The digital supply chain, a critical backbone of modern software [...]
A silent alarm rings across the cybersecurity landscape as a critical zero-day vulnerability in Cisco Catalyst SD-WAN Controller is under active exploitation. This isn’t a [...]
A disturbing new campaign is actively exploiting a recently identified vulnerability in Langflow, CVE-2026-33017, to compromise cloud environments. Attackers are leveraging this flaw to steal [...]
Urgent Action Required: Packagist Warns of GitHub Actions Token Leak in Composer The PHP development community is on high alert following a critical warning from [...]
The burgeoning world of Artificial Intelligence (AI) often arrives with promises of innovation and efficiency. Yet, beneath the surface of convenience, critical questions regarding user [...]