Larva-26002 Targets MS-SQL Servers with New ICE Cloud Scanner: What You Need to Know Microsoft SQL (MS-SQL) servers are a cornerstone of countless organizational [...]
The landscape of cyber warfare just intensified dramatically. A new and particularly aggressive destructive payload, dubbed CanisterWorm, has been deployed by the threat actor TeamPCP, [...]
When the Protectors Need Protecting: HackerOne Employees Affected by Navia Data Breach The very organizations dedicated to hardening our digital defenses are not immune [...]
Navigating the Dell Wyse Management Vulnerabilities: A Path to Complete System Compromise The digital landscape is a constant battleground, and even seemingly minor chinks [...]
A disturbing development has sent ripples through the cybersecurity community: the widely trusted open-source vulnerability scanner, Aqua Security’s Trivy, has been compromised in a [...]
Navigating the AI Frontier: Microsoft’s Enhanced Security for Generative Models in Azure AI Foundry The explosive growth of generative artificial intelligence presents unprecedented opportunities, [...]
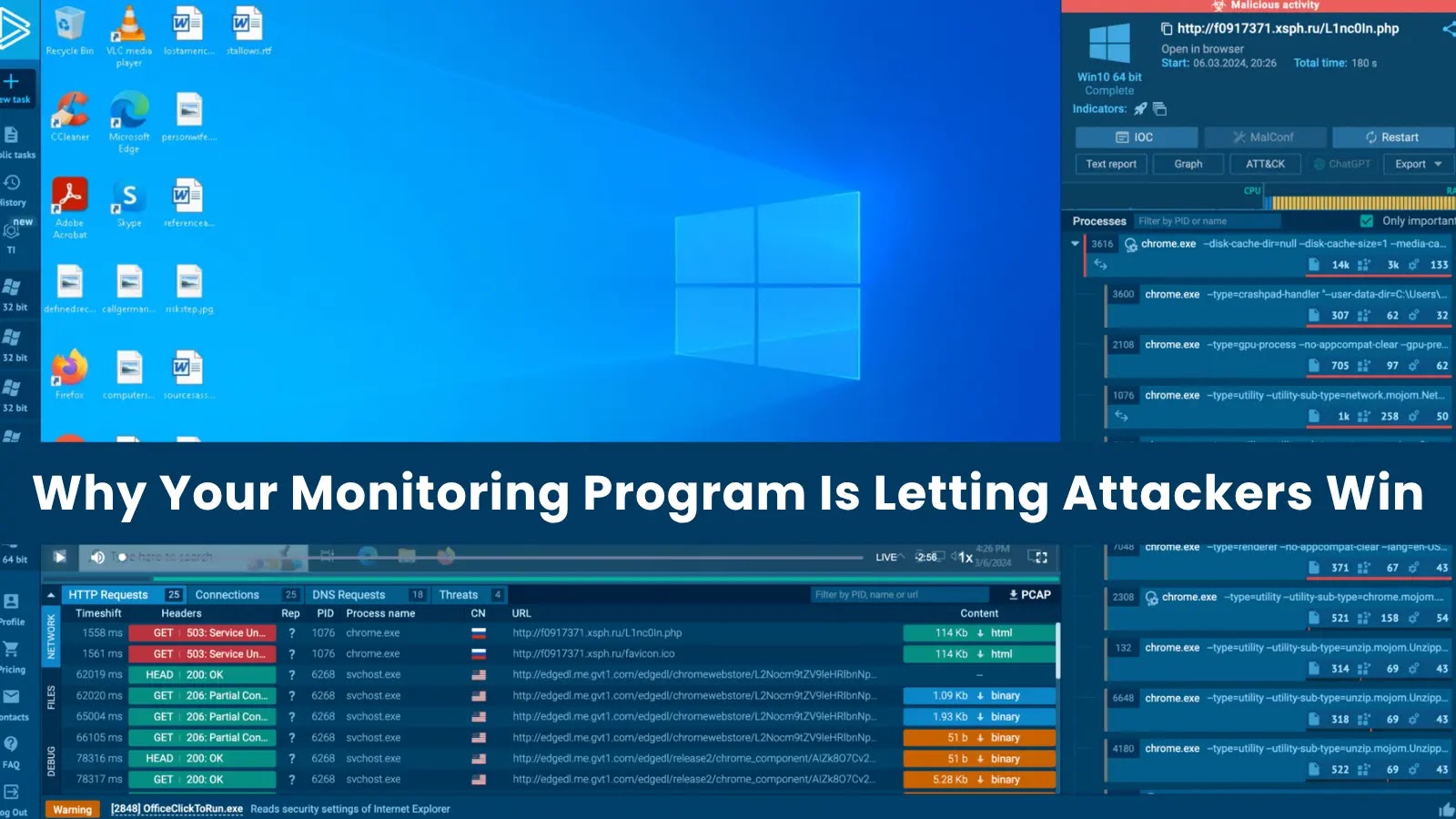
In the high-stakes world of cybersecurity, a sophisticated monitoring program is often considered the bedrock of defense. Organizations invest heavily in advanced logging infrastructures, myriad [...]
The digital underworld, a labyrinth of illicit markets and clandestine communications, has long posed a formidable challenge to cybersecurity professionals. Its sheer scale and the [...]
Distributed Denial of Service (DDoS) attacks are a persistent and growing threat, capable of crippling online services, disrupting businesses, and causing significant financial and reputational [...]
The dark web just became a more dangerous place for organizations. On March 22, 2026, a new Tor-based leak site, “ALP-001,” emerged, openly advertising itself [...]