The Trojan in Your Browser: Malicious Chrome MV3 Extension Steals TronLink Credentials The digital frontier of cryptocurrency continues to attract both innovation and insidious [...]
The Silent Compromise: Microsoft Warns of Malicious Code in MistralAI PyPI Package The rapid advancements in artificial intelligence have brought forth an explosion of [...]
The relentless pace of software development often outstrips the capacity for robust security integration. In an era dominated by advanced persistent threats and zero-day [...]
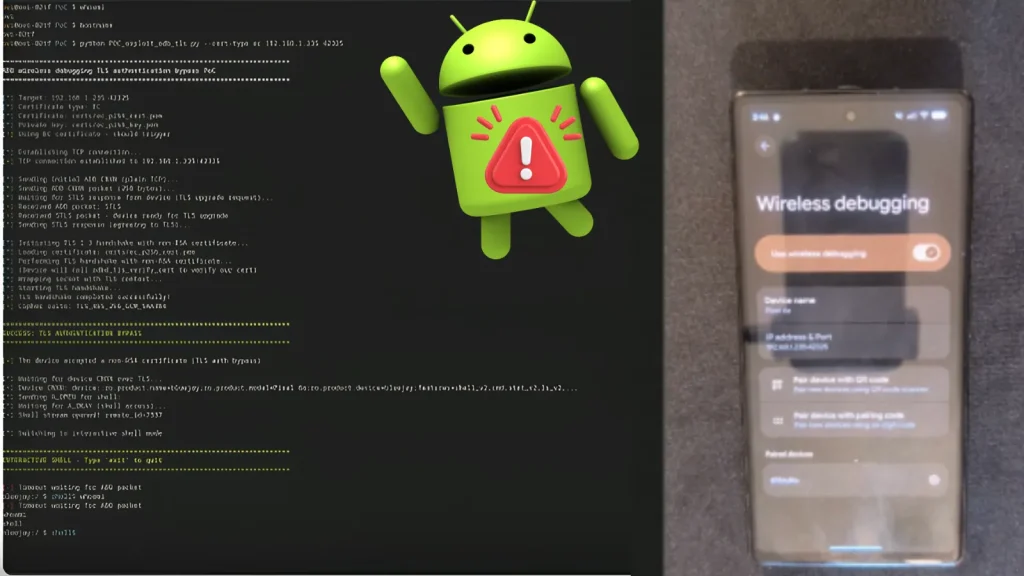
A disturbing new development has rocked the Android security landscape: a proof-of-concept (PoC) exploit has been released for a critical zero-click vulnerability. This flaw, [...]
The digital landscape is a constant battlefield, and a new shadow has emerged over Android users: TrickMo. This banking malware, far from a new [...]
A disturbing new report has surfaced from cybersecurity researchers, revealing a critical cluster of vulnerabilities within PHP’s core string processing and the ‘ext-soap’ components. This [...]
Online retail has become an indispensable part of modern life, offering convenience at our fingertips. Yet, this digital storefront is also a prime target [...]
A disturbing new chapter has unfolded in the ongoing saga of software supply chain attacks, reaching into the heart of application security tools. What began [...]
A troubling new report indicates a sophisticated, China-linked advanced persistent threat (APT) group, identified as UAT-8302, is actively compromising government agencies. This threat actor leverages [...]
The AI-Powered Zero-Day: Google Threatens a New Era of Exploits A recent report from Google’s Threat Intelligence Group has sent ripples through the cybersecurity community: [...]