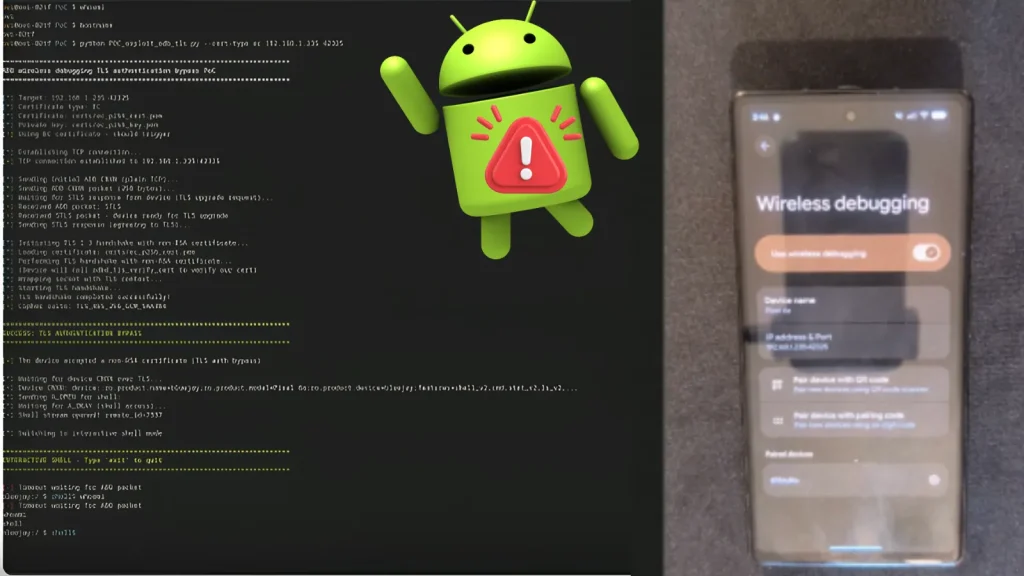
PoC Exploit Released for Android Zero-Click Vulnerability that Enables Remote Shell Access
A disturbing new development has rocked the Android security landscape: a proof-of-concept (PoC) exploit has been released for a critical zero-click vulnerability. This flaw, tracked as CVE-2026-0073, allows nearby attackers to gain full remote shell access to unsuspecting Android devices without any user interaction whatsoever. This represents a catastrophic cryptographic breakdown within the core Android System and demands immediate attention from users and organizations alike.
The Zero-Click Nightmare: CVE-2026-0073 Explained
Google’s May 2026 Android Security Bulletin unveiled CVE-2026-0073, a severe zero-click vulnerability residing within Android’s adbd daemon. This daemon, or Android Debug Bridge daemon, is a background process crucial for communication between an Android device and a development workstation. While typically used for legitimate debugging and development purposes, this flaw perverts its intended function.
The essence of a zero-click vulnerability is its uniquely insidious nature. Unlike phishing attempts or malicious app downloads, a zero-click exploit requires absolutely no action from the victim. The attacker simply needs to be within proximity, exploiting a weakness that automatically grants them unauthorized access. In the case of CVE-2026-0073 (MITRE CVE-2026-0073), this translates to an attacker gaining full remote shell access, effectively taking complete control of the compromised Android device.
How BARGHEST Researchers Uncovered the Flaw
This critical vulnerability was unearthed by security researchers at BARGHEST. Their findings highlight a profound cryptographic weakness, allowing nearby threat actors to bypass security measures and gain deep system access. The release of a PoC exploit for CVE-2026-0073 significantly escalates the risk, transforming what was a theoretical threat into an immediate and tangible danger for Android users.
Remote shell access grants an attacker the ability to execute arbitrary commands on the device. This means they could potentially:
- Steal sensitive personal data (photos, messages, financial information).
- Install malware or spyware.
- Monitor user activities (keystrokes, screen activity).
- Utilize the compromised device as part of a botnet.
- Take complete control over device functions, including the camera and microphone.
Remediation Actions and Mitigating the Threat
Given the severity and zero-click nature of CVE-2026-0073, immediate action is paramount for all Android users and organizations managing Android devices. Addressing this vulnerability requires a multi-layered approach to mobile security.
- Update Your Android Devices IMMEDIATELY: The most crucial step is to install the latest Android Security Bulletin updates. Google typically releases monthly security patches that address such vulnerabilities. Ensure your device is updated to the May 2026 Android Security Bulletin or later. If your device manufacturer has not yet pushed this update, contact them for timelines.
- Maintain Physical Distance in Public Areas: While not a permanent solution, being mindful of your surroundings, especially in public places like cafes, airports, or shared workspaces, can reduce the risk of a “nearby” attacker exploiting your device.
- Review Wi-Fi and Bluetooth Settings: Consider disabling Wi-Fi and Bluetooth when not in use, especially in untrusted environments. While the exploit leverages the
adbddaemon, reducing your device’s discoverability can contribute to overall security. - Implement Mobile Device Management (MDM): For enterprises, an effective MDM solution can help enforce security policies, push updates, and monitor device health across your fleet of Android devices.
- Educate Users: Inform users about the importance of keeping their devices updated and the risks associated with unpatched vulnerabilities.
Tools for Detection and Mitigation
While direct detection of the CVE-2026-0073 exploit in real-time might be challenging without specialized tools, several cybersecurity solutions can aid in overall mobile security and identify compromised devices or suspicious activity.
| Tool Name | Purpose | Link |
|---|---|---|
| Mobile Threat Defense (MTD) Solutions | Detects and prevents mobile-specific attacks, including zero-day exploits and malware. | (Varies by vendor, e.g., Lookout, Zimperium) |
| Endpoint Detection and Response (EDR) for Mobile | Monitors device activity, detects anomalies, and provides incident response capabilities. | (Varies by vendor, often integrated with EDR platforms) |
| Android Security Updates | Official patches released by Google to fix vulnerabilities. | source.android.com/security/bulletin |
| Network Intrusion Detection/Prevention Systems (NIDS/NIPS) | Can detect suspicious network traffic patterns originating from compromised devices. | (Various commercial and open-source options) |
Conclusion: The Urgency of Android Security
The release of a PoC exploit for CVE-2026-0073 underscores the constant, evolving threat landscape mobile devices face. A zero-click vulnerability granting remote shell access is among the most severe. Android users and IT professionals must prioritize timely patching and adopt robust mobile security practices to safeguard against this and future threats. Staying informed, promptly updating, and leveraging security tools are not just recommendations; they are immediate necessities in the face of such a critical vulnerability.





