Imagine your everyday browser activity, a seemingly innocuous visit to a website, quietly revealing details about your computer’s performance and, by extension, tracking your digital [...]
A sophisticated new phishing technique, dubbed VaultJacking, is sending shockwaves through the cybersecurity community. This alarming method allows attackers to compromise an entire Google Password [...]
The AI Paradox: When Malware Backfires – A GitHub Token Exposed In a revealing incident that underscores both the evolving threat landscape and the [...]
The AI Agent’s Ascent: From Marimo RCE to Database Dumper in Minutes In a stark illustration of escalating cyber threats, a recent incident on [...]
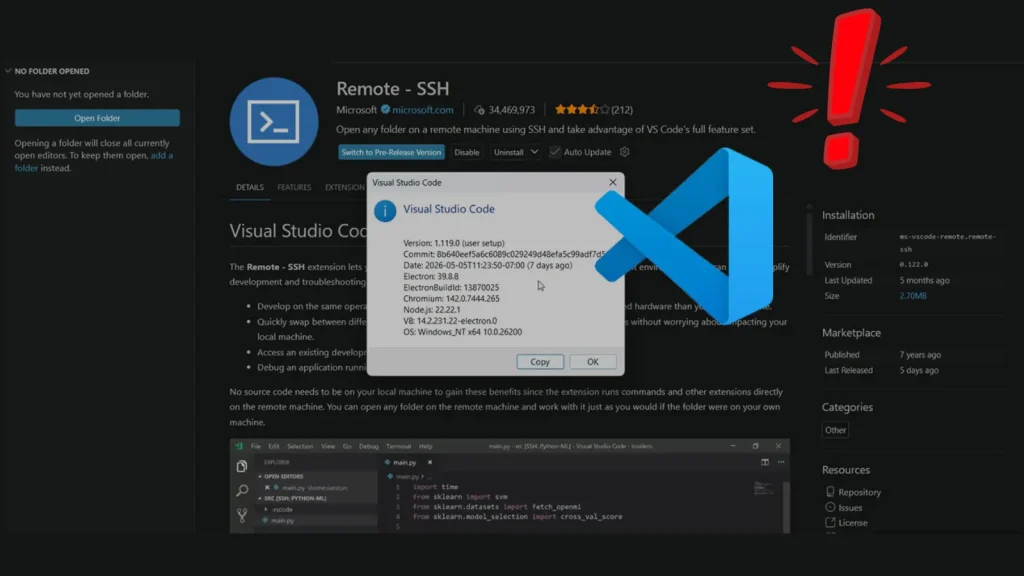
Introduction: The Hidden Bridge to Your Cloud – VS Code Remote-SSH RCE The modern software development landscape is increasingly distributed, with developers often connecting [...]
The digital landscape is a constant battleground, and threat actors are perpetually refining their tactics. A particularly insidious trend is emerging within Microsoft Teams [...]
Unmasking CVE-2026-9560: A Critical Flaw in OpenVPN Connect for macOS The digital landscape demands unwavering vigilance, especially when it comes to tools designed to secure [...]
Unmasking the VIP Keylogger Threat: How Phishing Emails Are Exploiting Business Trust In the intricate landscape of cyber threats, one constant remains: attackers relentlessly refine [...]
In March 2026, a sophisticated wave of malicious spam emails infiltrated inboxes globally, targeting critical sectors like energy, automotive, and government finance. These attackers weren’t [...]
The digital seas can be perilous, not just for ships, but for the data of their passengers. Carnival Corporation, the world’s largest cruise company and [...]