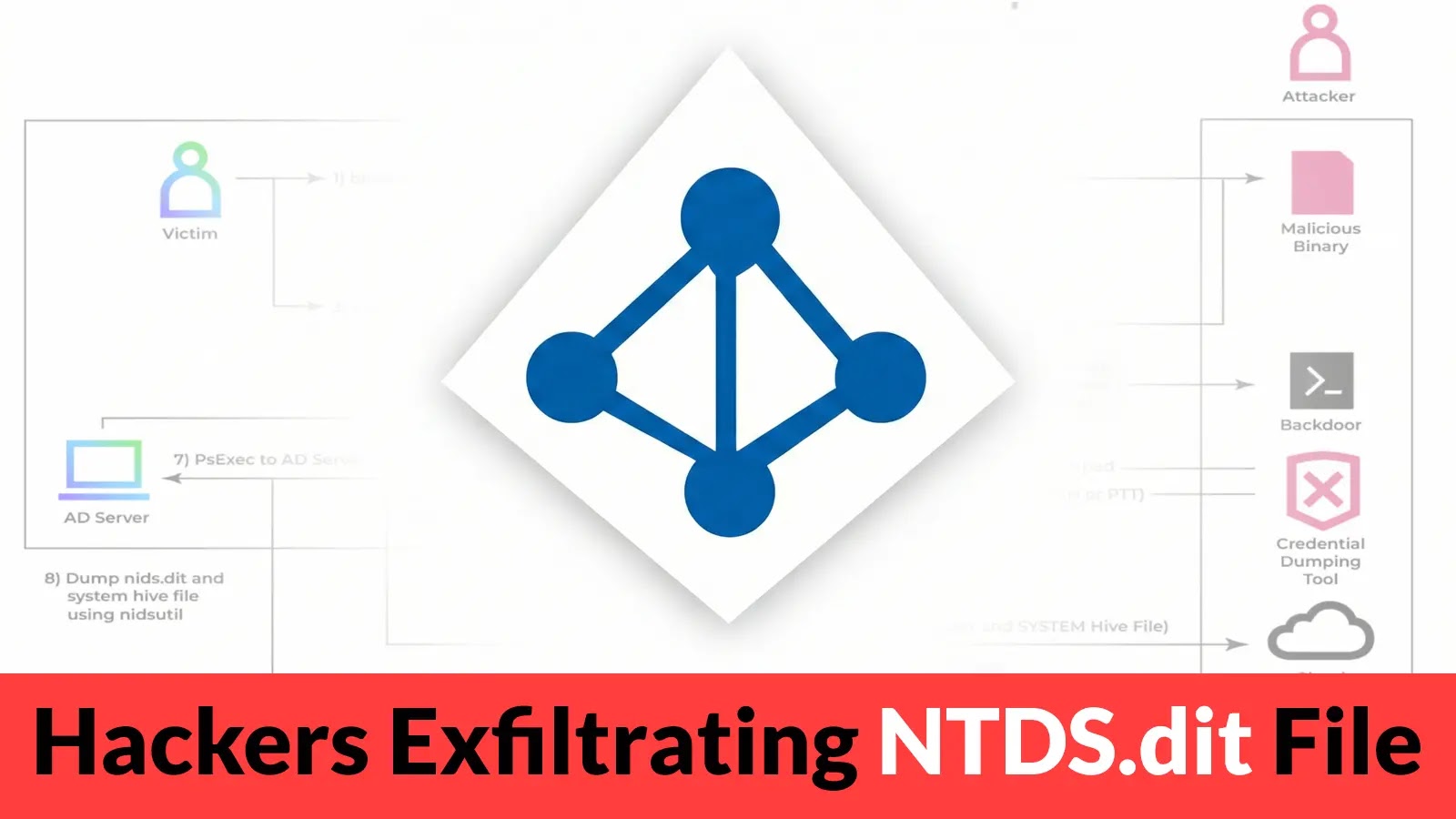
Few assets within an organization’s digital infrastructure are as critical as Active Directory. It’s the cornerstone of identity and access management, the gatekeeper to your [...]
A critical alert has been issued for developers leveraging the Django web framework. Recent disclosures reveal a series of severe vulnerabilities that could expose [...]
A disturbing discovery has recently sent ripples through the Kubernetes ecosystem: a critical security vulnerability in ingress-nginx, a widely adopted Kubernetes ingress controller. This flaw, [...]
Urgent Alert: Large-Scale Reconnaissance Targets Citrix NetScaler Login Panels The digital perimeter of many organizations relies heavily on robust gateways, and Citrix NetScaler (formerly Citrix [...]
Urgent Warning: SolarWinds Web Help Desk RCE Vulnerability Under Active Exploitation A critical remote code execution (RCE) vulnerability in SolarWinds Web Help Desk is [...]
A critical security update for Google Chrome is sounding the alarm across the digital landscape, demanding immediate attention from users and IT professionals alike. [...]
Microsoft is making a significant move to bolster the security of Windows authentication. The tech giant has announced an accelerated phased roadmap to reduce, restrict, [...]
In the evolving landscape of cyber threats, a new sophisticated phishing campaign has emerged, specifically targeting macOS users. This campaign leverages meticulously crafted fake [...]
Unpacking the Latest PDFly Variant: A Deep Dive into Custom PyInstaller Obfuscation The cybersecurity landscape is a relentless battleground, and threat actors are continuously [...]
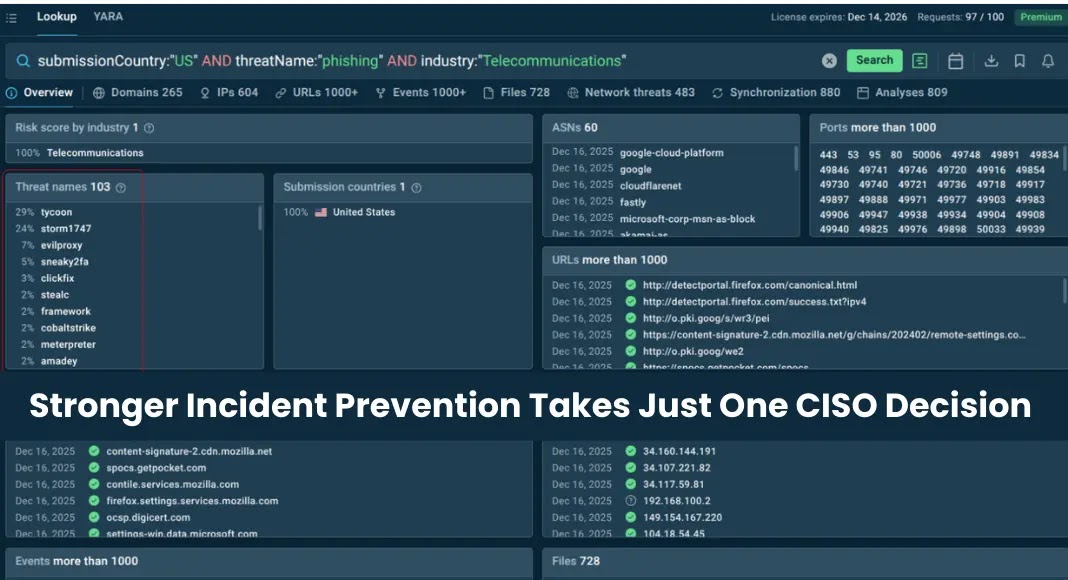
In the complex theater of cybersecurity, a persistent and often misleading narrative suggests that when the digital battleground gets noisy, the immediate solution is [...]