The operational technology (OT) landscape is a perpetual target for threat actors, and the stability of industrial control systems (ICS) hinges on robust security. A [...]
The network is the ultimate source of ground truth in the modern enterprise. As organizations accelerate their digital transformation and adopt complex, cloud-native security architectures, [...]
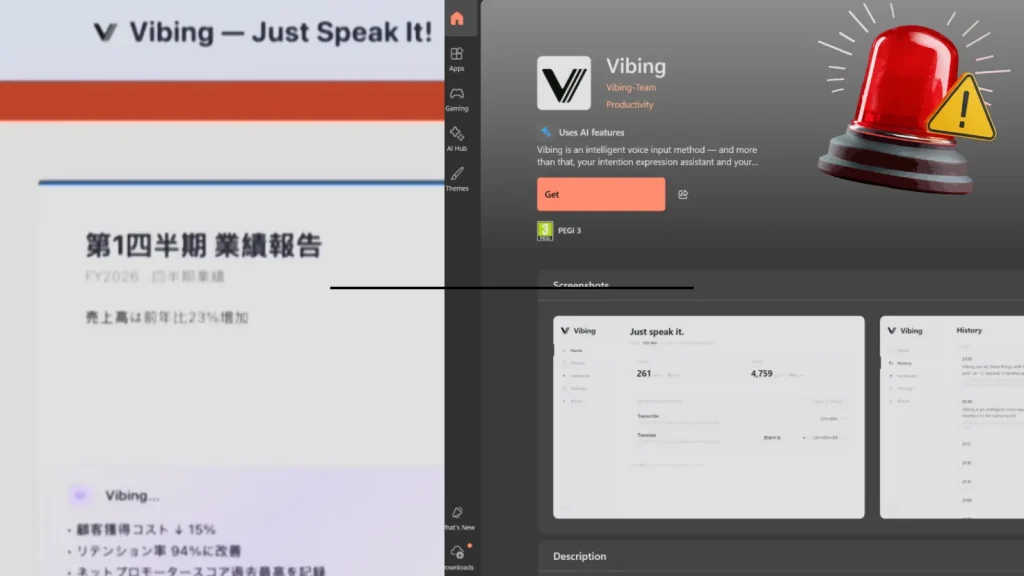
A disturbing report has emerged from the cybersecurity community, highlighting a significant privacy and security risk originating from an application available on the official Microsoft [...]
In the high-stakes world of cybersecurity, the whispers of a new, exceptionally dangerous threat often precede a storm. Enter ‘fast16,’ a recently unearthed malware strain [...]
The landscape of cyber threats is in constant flux, with sophisticated malware continually evolving its tactics to bypass even the most robust security measures. A [...]
The rapid advancement of artificial intelligence, particularly large language models (LLMs), presents both unprecedented opportunities and significant security challenges. As these systems become more sophisticated [...]
Artificial intelligence is rapidly reshaping industries, and its capabilities are expanding into domains once exclusively human. A recent experiment by Anthropic, dubbed “Project Deal,” has [...]
CISA Warns of Critical SimpleHelp Vulnerabilities Actively Exploited in Attacks The digital landscape is a constant battlefield, and organizations rely heavily on remote access tools [...]
A significant architectural flaw, dubbed PhantomRPC, has been uncovered within the Windows Remote Procedure Call (RPC) mechanism. This critical vulnerability allows for local privilege escalation, [...]
A Critical Blow: Litecoin Zero-Day Vulnerability Rocks Mining Pools The cryptocurrency landscape, while built on principles of decentralization and security, is not immune to sophisticated [...]