Role of Layer 2 Switches in Zero Trust Architecture: Layer 2 Segmentation, Zero Trust Security Use Cases & Verification In today’s dynamic threat landscape, a [...]
Fortigate Fortinet: Unify Security Operations & Unified Threat Management In today’s rapidly evolving digital landscape, safeguarding your infrastructure is paramount to ensuring the success of [...]
SSL/SSH Inspection Explained: Deep Packet Inspection Analysis on FortiGate SSH Inspection and SSL Inspection. In the ever-evolving landscape of cybersecurity threats, safeguarding your enterprise’s data [...]
Fortinet FortiSandbox: The Ultimate Duo Against Zero-Day Threat Protection and Fortigate Analysis In an era where cyber threats evolve at an alarming pace, safeguarding your [...]
Fortinet FortiGate Firewall: Implementing Advanced Threat Protection (ATP) Against Threats a Step-by-Step Guide. In today’s rapidly evolving digital landscape, safeguarding enterprise networks from advanced threats [...]
How Fortigate Reduces Next-Generation Firewall ROI: Fortinet FortiGate vs. Palo Alto Downtime and Boosts Productivity. In the realm of cybersecurity, safeguarding your enterprise is paramount [...]
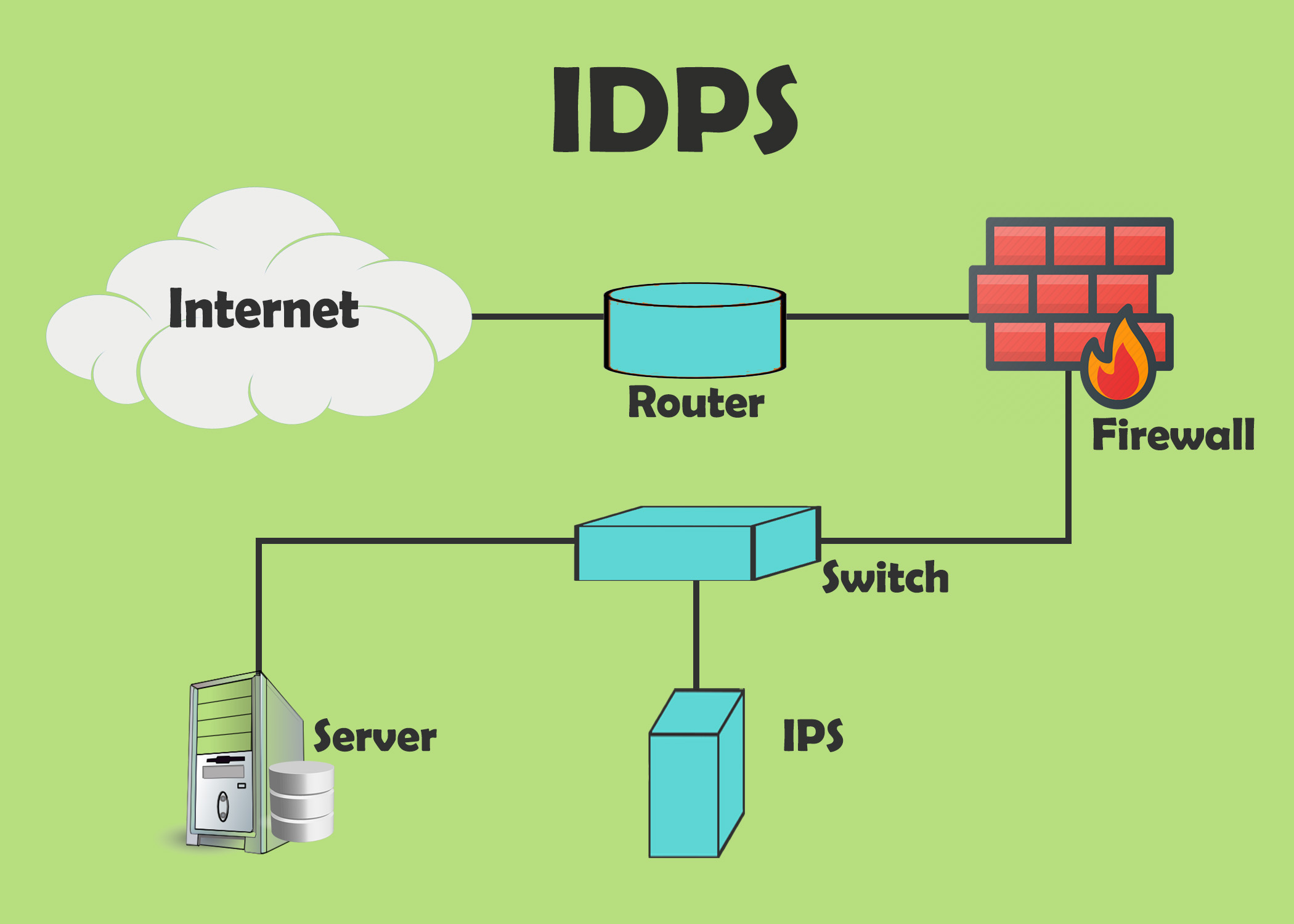
IDS and IPS: Understanding Intrusion Detection and Intrusion Prevention Systems In today’s digital landscape, securing networks against evolving cyber threats is crucial. Intrusion Detection Systems [...]
Evolution of Firewall: From Network Security to Cloud Firewalls In today’s digital landscape, the evolution of firewall technology is crucial for maintaining robust network security [...]
Fortinet: Automation SOC Detection with FortiAnalyzer and FortiSOAR Playbooks Automate Security Team. In today’s rapidly evolving digital landscape, ensuring the security of your enterprise is [...]
In today’s digitally-driven landscape, ensuring robust security measures within your network infrastructure is not just a priority—it’s a necessity for effective cyber security. As businesses [...]