Unmasking the SSH-Like Deception: A New Supply Chain Threat to Linux Developers The digital fabric of software development relies heavily on shared packages and [...]
Urgent Warning: Critical 7-Zip Vulnerability Allows Arbitrary Code Execution A severe vulnerability has been uncovered in the widely used open-source archiving tool, 7-Zip, posing a [...]
The digital battlefield evolves constantly, with advanced persistent threat (APT) groups continually refining their tactics. A recent discovery shines a spotlight on the Cloud Atlas [...]
The digital black market is evolving at an alarming pace, transforming traditional illicit activities into highly structured, on-demand services. A disturbing trend has emerged where [...]
The silent war against cyber threats wages on, and a recent development indicates a significant shift in adversary tactics. North Korea-linked threat actors, specifically [...]
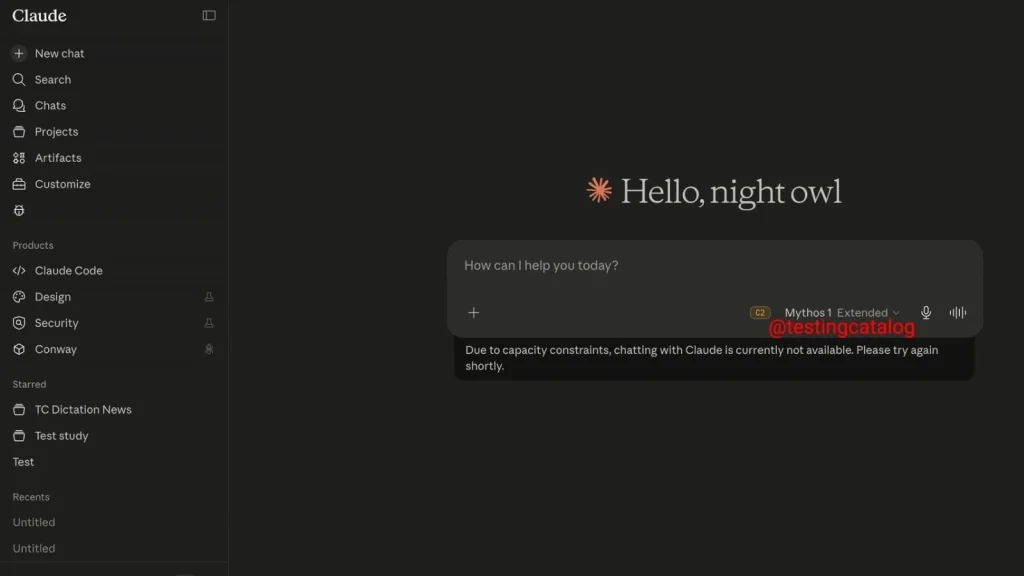
Anthropic, a prominent player in the AI landscape, appears to be making strategic moves with its most powerful and previously restricted AI model, Claude [...]
The convergence of advanced AI, geopolitical motivations, and sophisticated cyberattacks presents an increasingly complex threat landscape. A recent, alarming incident brought to light by TrendAI [...]
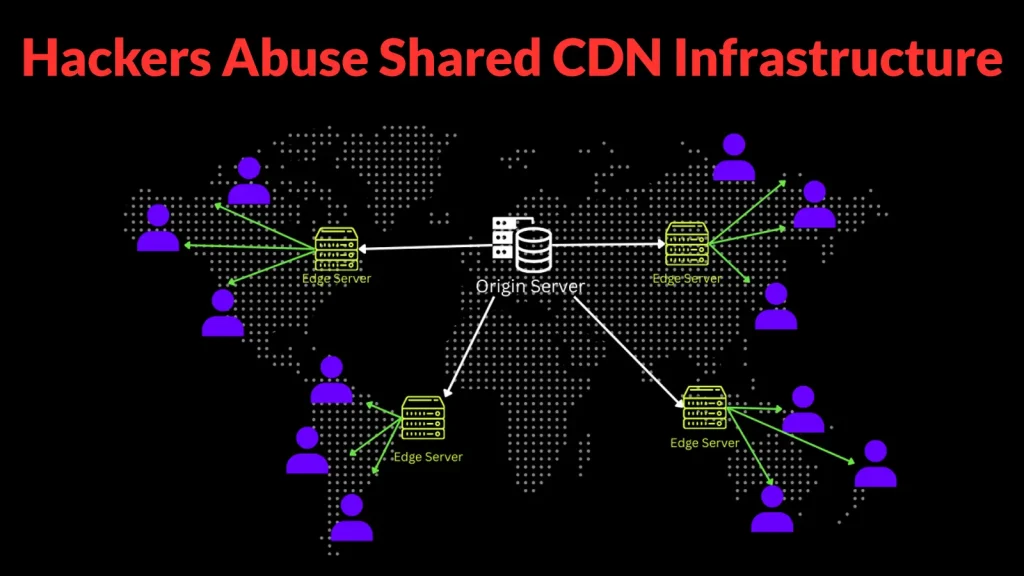
The Underminr Threat: How Shared CDN Abuse Bypasses Your Security Defenses The digital landscape often presents a deceptive veneer of security, particularly when relying on [...]
In a concerning shift in tactics, a prominent Iranian advanced persistent threat (APT) group has deployed an ingenious method to compromise targets: SEO poisoning to [...]
Urgent Alert: KnowledgeDeliver LMS Zero-Day Exploited to Deploy BLUEBEAM Web Shell A critical zero-day vulnerability in the popular KnowledgeDeliver Learning Management System (LMS) has been [...]