The digital landscape is a gauntlet of persistent threats, and maintaining up-to-date systems is paramount for robust cybersecurity. Yet, what happens when the very mechanism [...]
Urgent Warning: Netlogon 0-Click RCE Actively Exploited in the Wild The cybersecurity landscape has once again been rattled. A critical remote code execution (RCE) vulnerability [...]
The landscape of cybersecurity is constantly evolving, with threats becoming more sophisticated and attack surfaces expanding. For penetration testers and security teams, keeping pace with [...]
Unmasking ‘The Gentlemen’: A New Strain of Ransomware Leveraging SYSTEM Scheduled Tasks The cybersecurity landscape faces a growing threat from a sophisticated ransomware variant dubbed [...]
A critical authentication bypass vulnerability affecting Palo Alto Networks devices, identified as CVE-2026-0257, is now actively being exploited in the wild. This urgent development necessitates [...]
The AI Shadow War: How GREYVIBE Hackers Weaponize ChatGPT and Gemini The landscape of cyber warfare is undergoing a profound transformation, with sophisticated threat actors [...]
For too long, the concept of post-quantum cryptography (PQC) existed in a theoretical realm, a fascinating topic for conferences and research papers. CISOs and security [...]
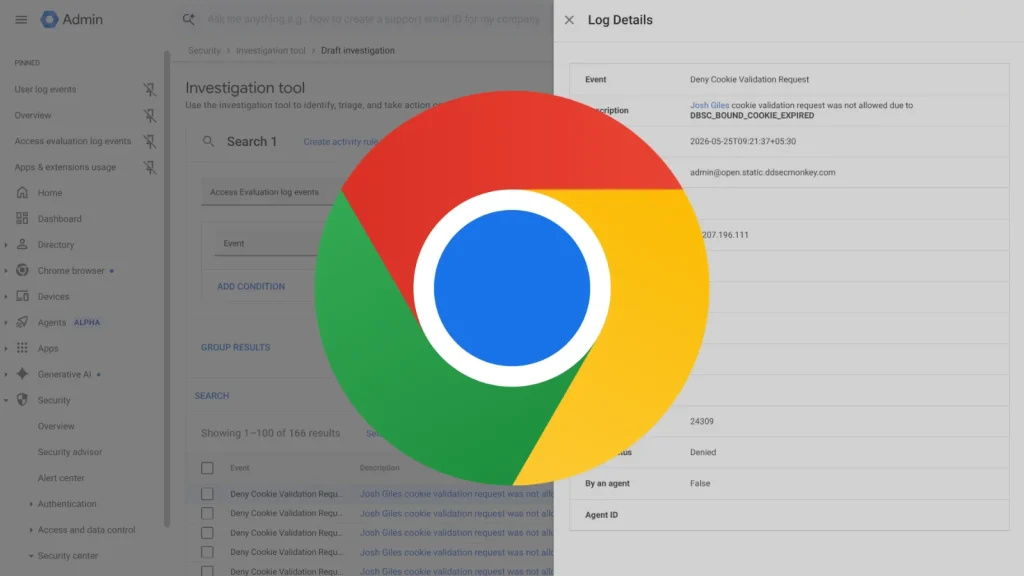
The digital landscape is a constant battleground, and for organizations and individuals alike, account takeover (ATO) remains one of the most insidious threats. Attackers relentlessly [...]
A disturbing trend has emerged in the cybersecurity landscape: attackers are increasingly weaponizing the very tools developers rely on daily. We’re witnessing a wave of [...]
A sophisticated new threat actor, JINX-0164, is actively leveraging LinkedIn to execute highly targeted social engineering attacks against cryptocurrency organizations. This group employs a dangerous [...]