Imagine a sophisticated phishing attack unfolding directly within a trusted application, leveraging its features to deceive you. This isn’t a hypothetical scenario; it’s the reality [...]
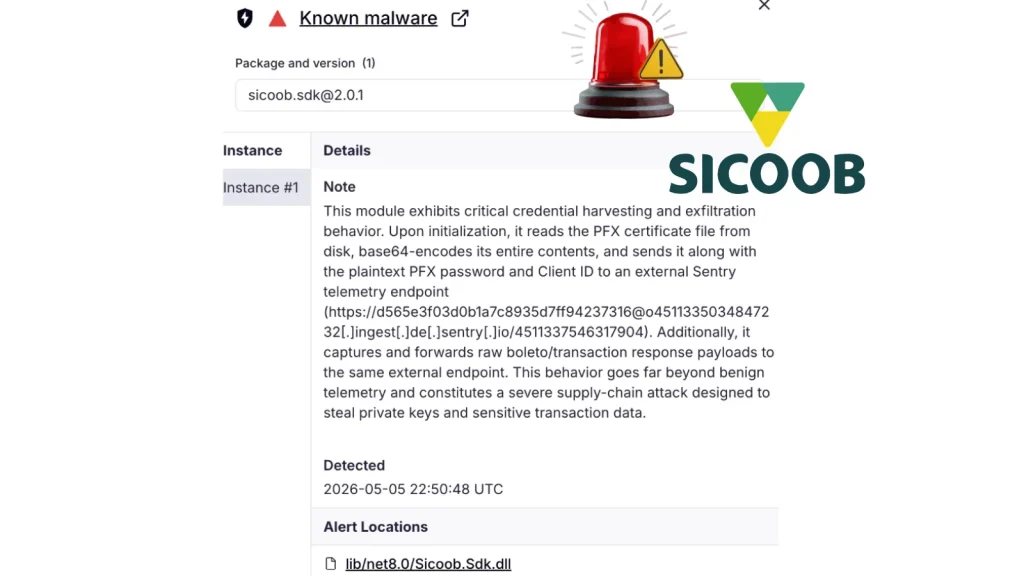
The digital supply chain, a critical nexus of modern software development, has once again been breached with alarming consequences. A recently uncovered malicious NuGet package, [...]
The Trojan Horse of Entertainment: How Fake Video Player Updates Deploy Miner and RAT Malware The allure of free, readily available content often outweighs caution [...]
The open-source software supply chain, a critical pillar of modern development, is once again under siege. A recent discovery on May 28, 2026, has shed [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in Check Point Products Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: CRITICAL Software Affected Security [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in 7-Zip Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Software Affected 7-Zip versions prior [...]
Oracle has just rolled out its inaugural Critical Security Patch Update (CSPU), a significant release designed to fortify the security posture of its extensive [...]
The Trojan within: Malicious `codexui-android` Package Steals OpenAI Codex Tokens The ubiquity of open-source packages in modern software development presents a double-edged sword. While [...]
The Deceptive Lure: Fake Adobe Document Cloud Pages Delivering ScreenConnect Malware In the intricate landscape of cyber threats, attackers constantly evolve their tactics to bypass [...]
In a concerning development for the cybersecurity landscape, a novel malware dubbed MicrosoftSystem64 has emerged, demonstrating sophisticated tactics for data exfiltration. This new threat [...]