The digital landscape is a dynamic battlefield, and even the most ubiquitous communication platforms aren’t immune to attack. Microsoft Teams, a cornerstone for collaboration in [...]
Unmasking PoisonSeed: The Phishing Kit Bypassing MFA to Steal Your Credentials Modern cybersecurity defenses often pivot on Multi-Factor Authentication (MFA) as a robust barrier [...]
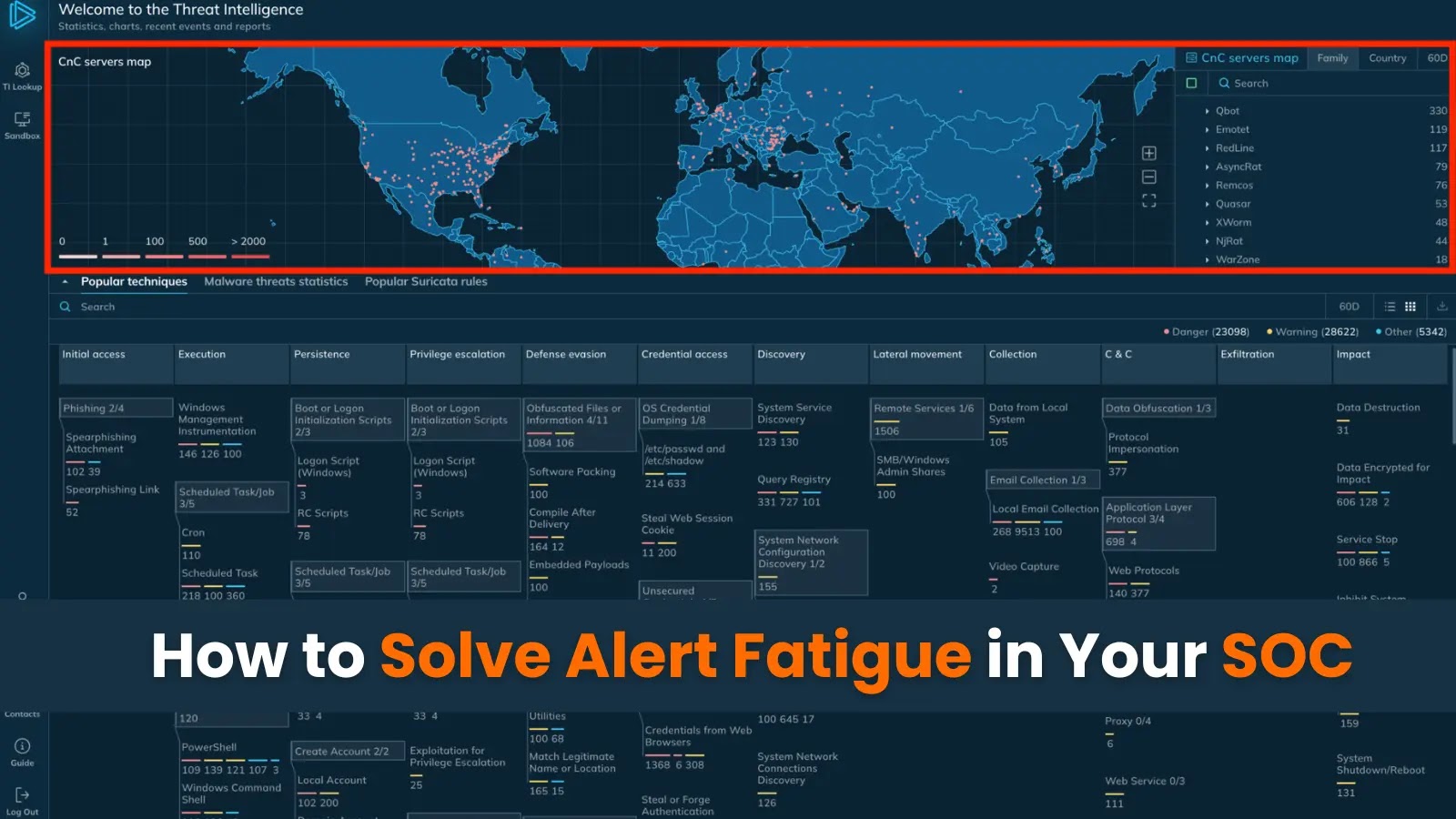
Imagine your Security Operations Center (SOC) as the tactical center of a medieval fortress, where vigilant sentries scan the horizon for approaching threats. But instead [...]
The digital threat landscape is in constant flux, with cybercrime groups continually refining their tactics and forming new alliances to maximize their impact. A [...]
The digital landscape relies heavily on uninterrupted access to critical productivity tools. Few platforms embody this reliance more than Microsoft Office.com, the central hub [...]
A disturbing revelation has shaken the cybersecurity landscape, underscoring the critical importance of secure AI implementation in corporate environments. A recent discovery has unveiled [...]
Git 2.51: Ushering in Performance and Next-Gen Security for Developers The continuous evolution of version control systems is paramount for efficient software development and [...]
In the intricate landscape of digital security, proactive threat detection stands as the bulwark against emerging cyber threats. Identity and access management (IAM) systems, [...]
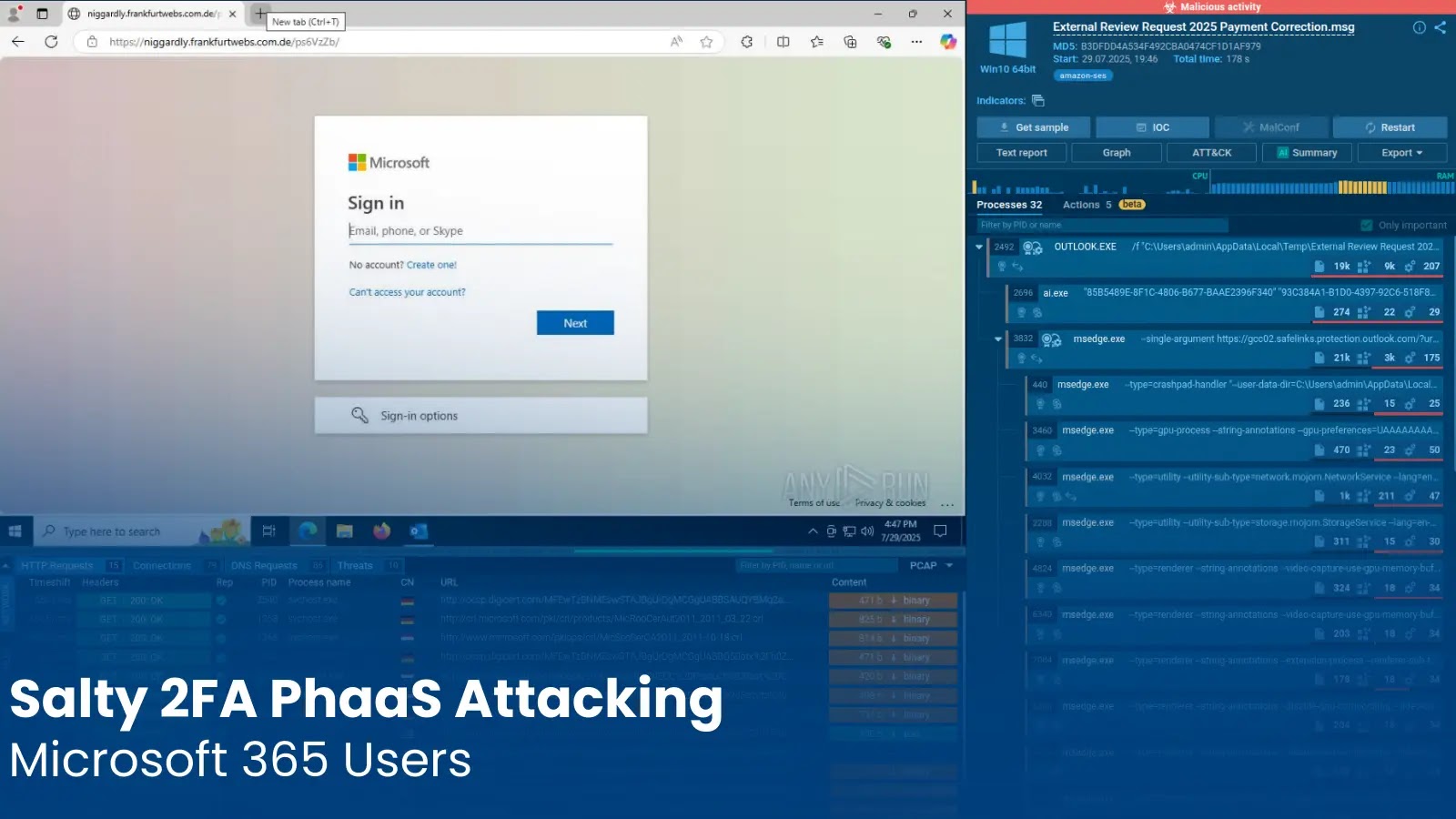
Salty 2FA: Unmasking the Advanced Phishing-as-a-Service Threat to Microsoft 365 The digital landscape is under relentless assault, and a sophisticated new threat has emerged, [...]
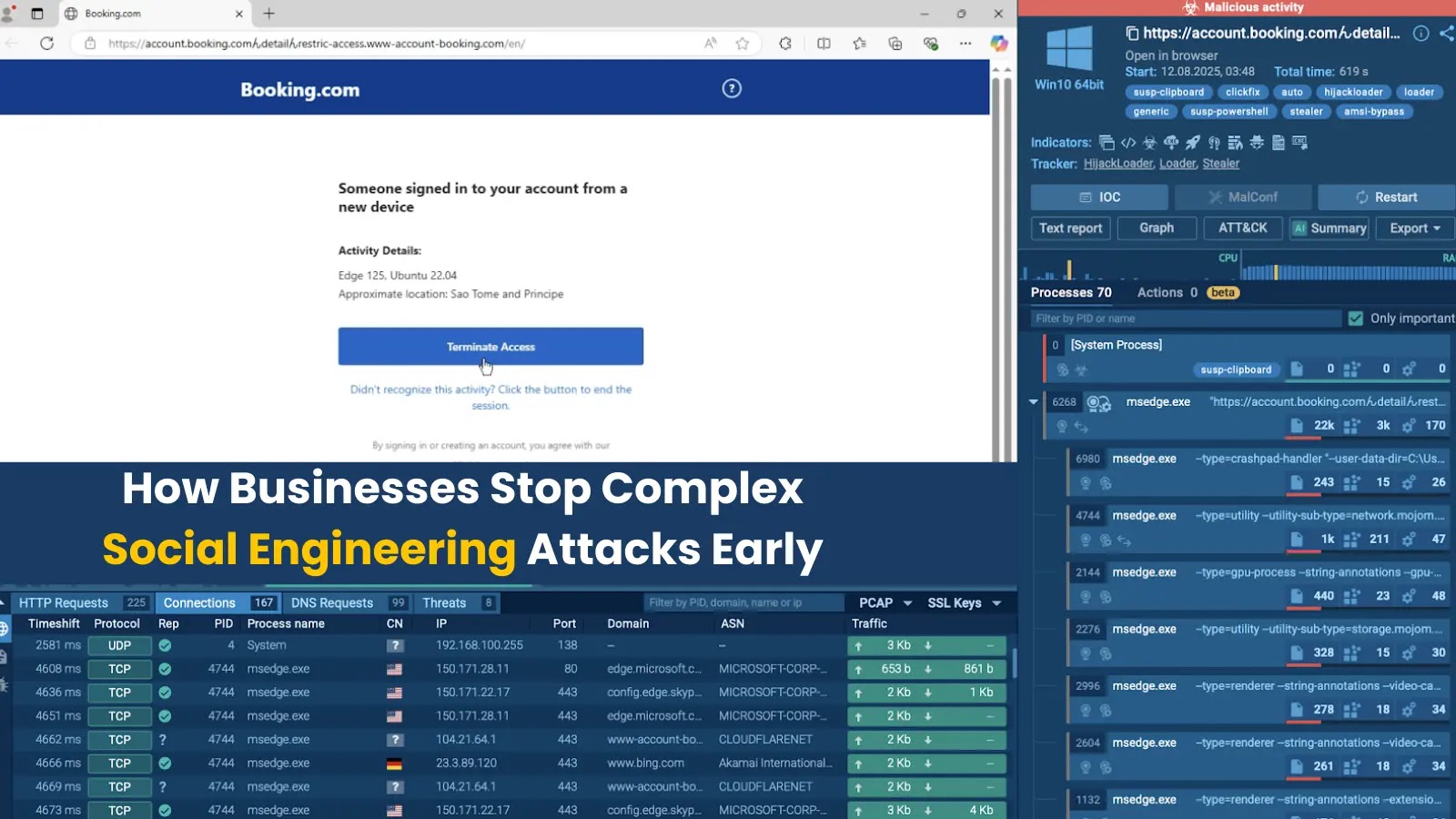
The landscape of cyber threats has transformed dramatically. Gone are the days when phishing attempts were easily spotted by glaring grammatical errors or suspicious [...]