Git 2.51: Ushering in Performance and Next-Gen Security for Developers The continuous evolution of version control systems is paramount for efficient software development and [...]
In the intricate landscape of digital security, proactive threat detection stands as the bulwark against emerging cyber threats. Identity and access management (IAM) systems, [...]
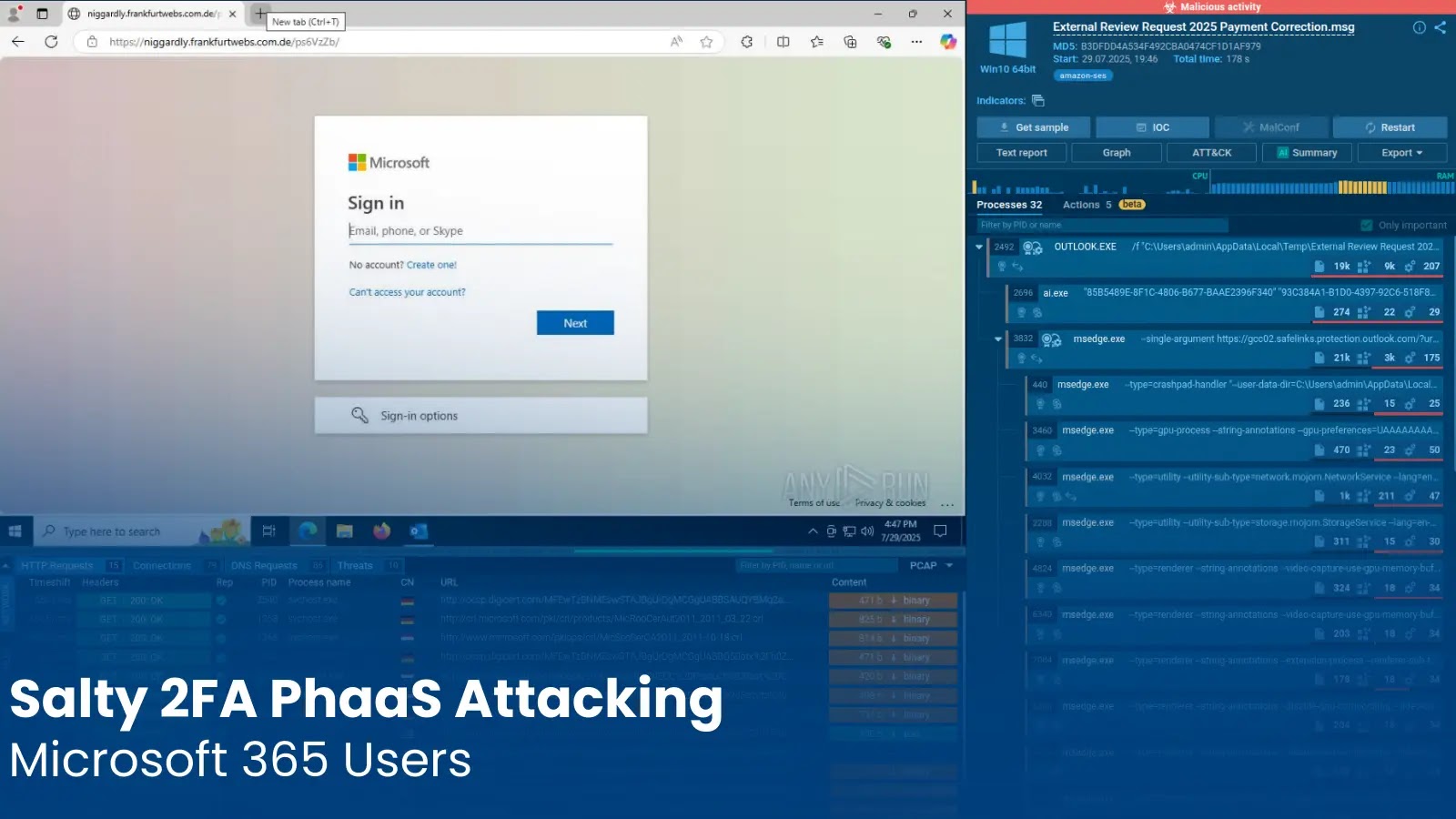
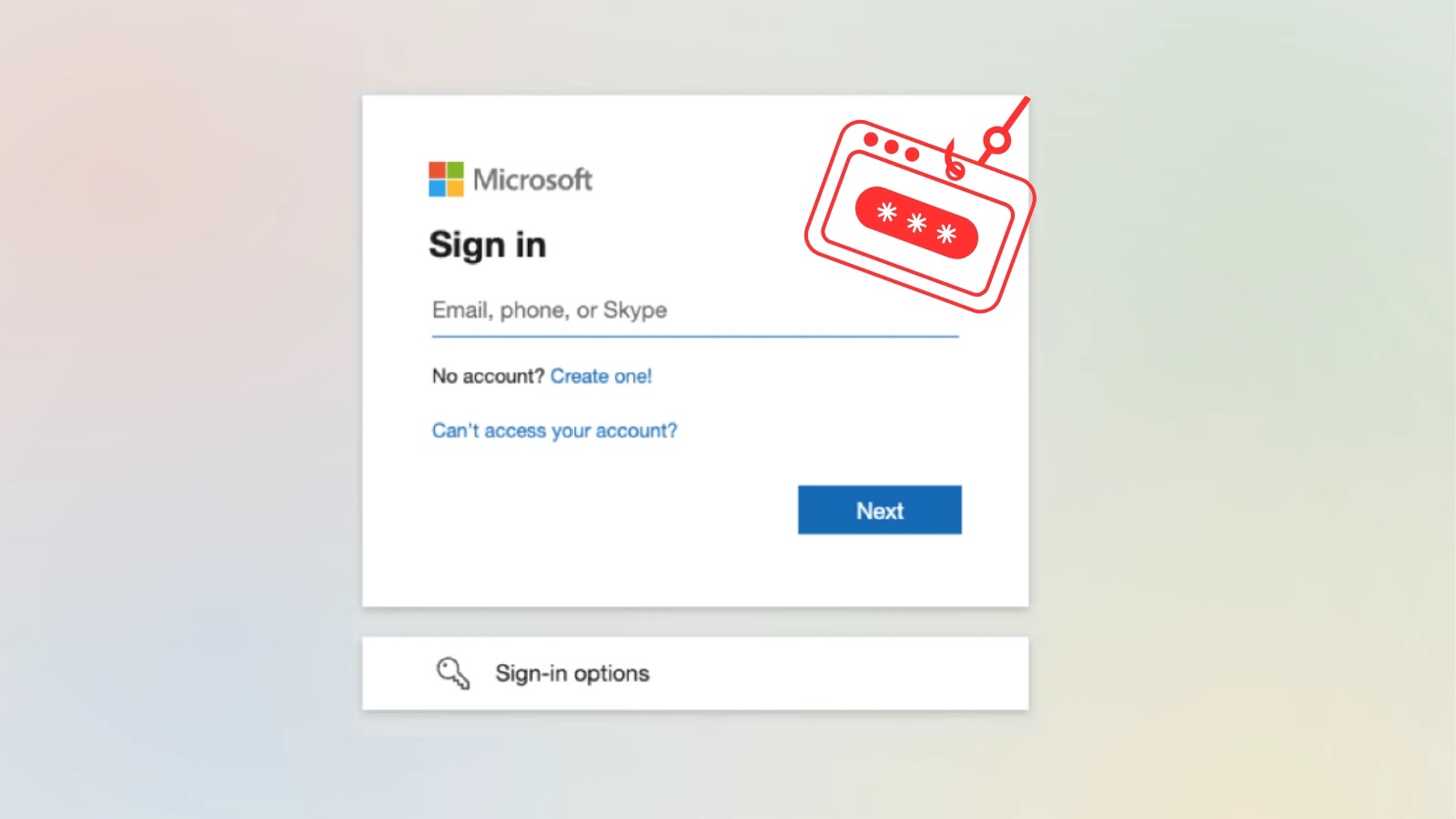
Salty 2FA: Unmasking the Advanced Phishing-as-a-Service Threat to Microsoft 365 The digital landscape is under relentless assault, and a sophisticated new threat has emerged, [...]
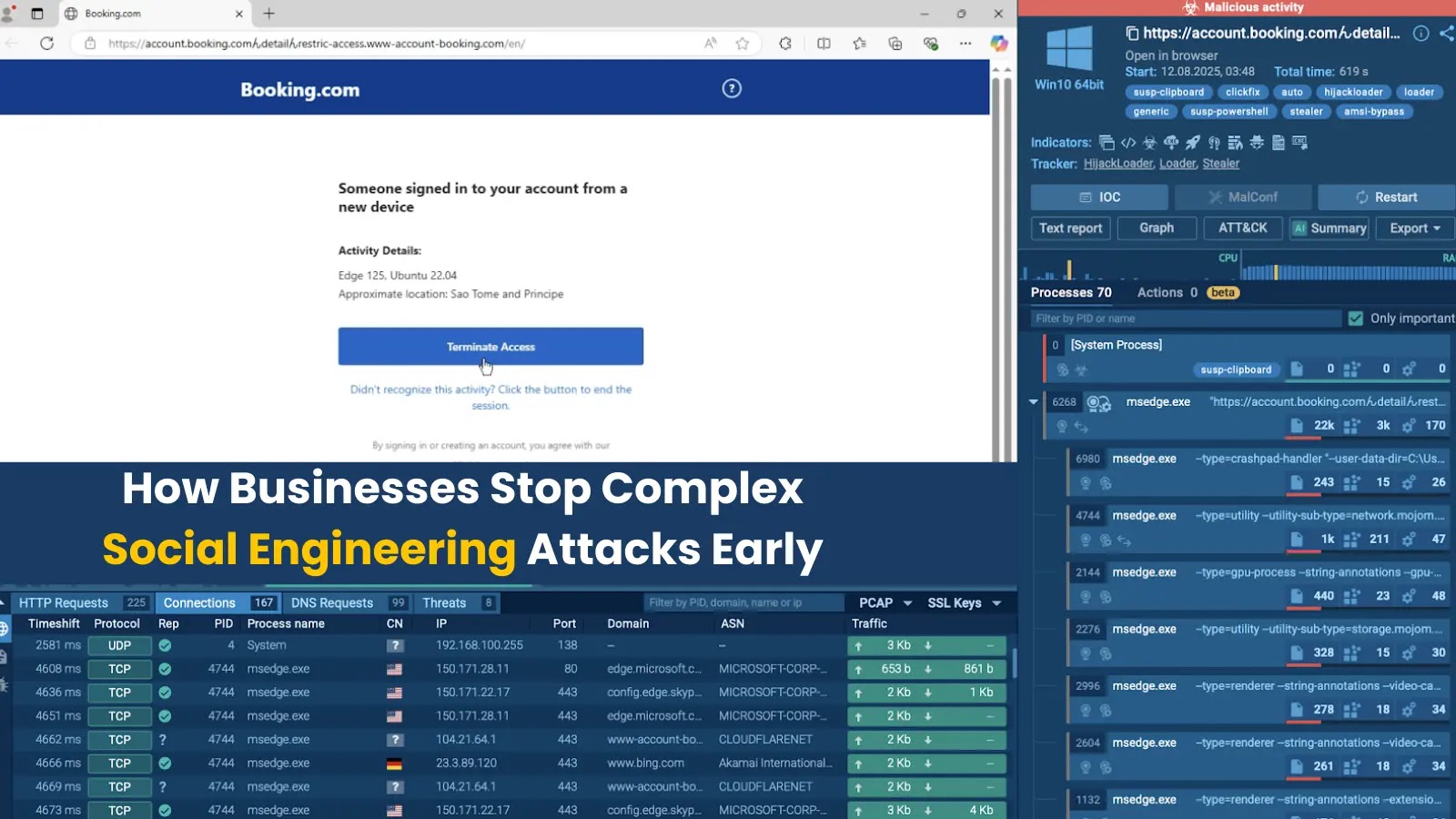
The landscape of cyber threats has transformed dramatically. Gone are the days when phishing attempts were easily spotted by glaring grammatical errors or suspicious [...]
The Deceptive Lure: How ADFS and Office.com Are Weaponized to Steal Microsoft 365 Logins The digital frontier is constantly shifting, and with it, the [...]
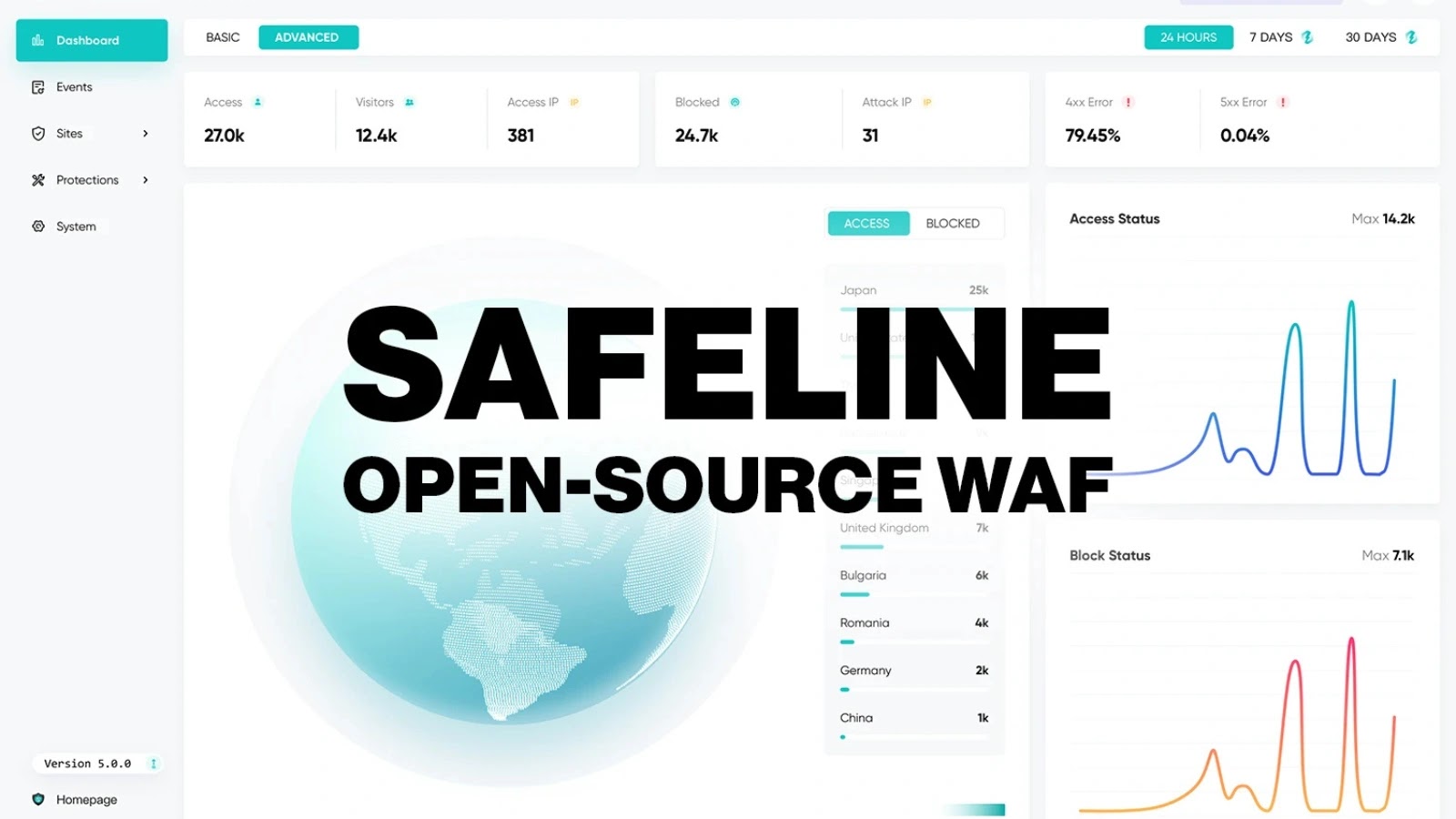
SafeLine: A Free Zero Trust Web Application Firewall for 2026 In a landscape where cyber threats escalate daily, the security of web applications is [...]
Yesterday, Apple released urgent security updates for its iOS and iPadOS operating systems, addressing a critical zero-day vulnerability that is actively being exploited in [...]
Japan, a nation often lauded for its technological prowess and commitment to innovation, is currently grappling with a stark and unsettling reality: a significant [...]
Fortinet SSL VPN Under Siege: An Unprecedented Brute-Force Barrage The digital perimeter of many organizations relies heavily on secure remote access. Fortinet SSL VPNs, [...]
Critical Zoom Vulnerability: A Deep Dive into CVE-2025-49457 The security landscape is constantly shifting, and even the most ubiquitous software can harbor critical vulnerabilities. [...]