In the dynamic landscape of enterprise security, the emergence of a critical vulnerability, especially one under active exploitation, demands immediate attention. Organizations leveraging Trend [...]
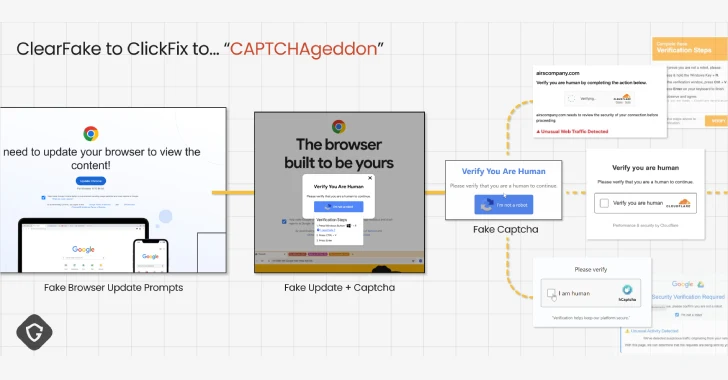
ClickFix Malware Campaign Exploits CAPTCHAs to Spread Cross-Platform Infections The digital threat landscape constantly evolves, with new attack methodologies pushing the boundaries of social engineering [...]
Cisco Hacked: Understanding the Vishing Attack That Compromised User Data A recent cyberattack on Cisco has highlighted the persistent threat of sophisticated social engineering [...]
Unmasking MCPoison: A Critical RCE Vulnerability in Cursor IDE In the rapidly evolving landscape of AI-powered development tools, security vulnerabilities can have far-reaching consequences [...]
Navigating the New SEC Compliance Mandate: Your Network Security Checklist for Audit Readiness The landscape of cybersecurity compliance has shifted dramatically. With new SEC [...]
Secure Socket Layer (SSL) certificates, more accurately known as Transport Layer Security (TLS) certificates, are the silent guardians of digital trust. They underpin the security [...]
Unlocking the Future of Software Security: Microsoft’s $5 Million Zero Day Quest The digital landscape is a constant battleground, with new threats emerging daily. [...]
U.S. Treasury Sounds Alarm: Crypto ATMs Exploited by Criminal Enterprises The burgeoning landscape of digital finance offers unparalleled convenience and accessibility. However, this rapid [...]
Unmasking ClickTok: The 10,000+ Malicious TikTok Shop Domains Exploiting Users The digital landscape of e-commerce is constantly evolving, bringing convenience and accessibility to millions. [...]
The AI Frontier: Navigating the Rising Tide of Cyber Attacks on LLM Infrastructure The landscape of cyber threats is in constant flux, and one [...]