Unmasking ClearFake: The Evolving Threat of Blockchain-Powered C2 The cybersecurity landscape has witnessed a disturbing evolution in recent months, with threat actors continuously innovating [...]
A significant vulnerability has emerged in the Linux ecosystem, posing a critical threat to system security. Dubbed “CIFSwitch,” this local privilege escalation (LPE) flaw [...]
Claude Opus 4.8: The AI Engineer Arrives The pace of AI development is staggering, and Anthropic’s latest release, Claude Opus 4.8, marks a significant [...]
Imagine your everyday browser activity, a seemingly innocuous visit to a website, quietly revealing details about your computer’s performance and, by extension, tracking your digital [...]
A sophisticated new phishing technique, dubbed VaultJacking, is sending shockwaves through the cybersecurity community. This alarming method allows attackers to compromise an entire Google Password [...]
The AI Paradox: When Malware Backfires – A GitHub Token Exposed In a revealing incident that underscores both the evolving threat landscape and the [...]
The AI Agent’s Ascent: From Marimo RCE to Database Dumper in Minutes In a stark illustration of escalating cyber threats, a recent incident on [...]
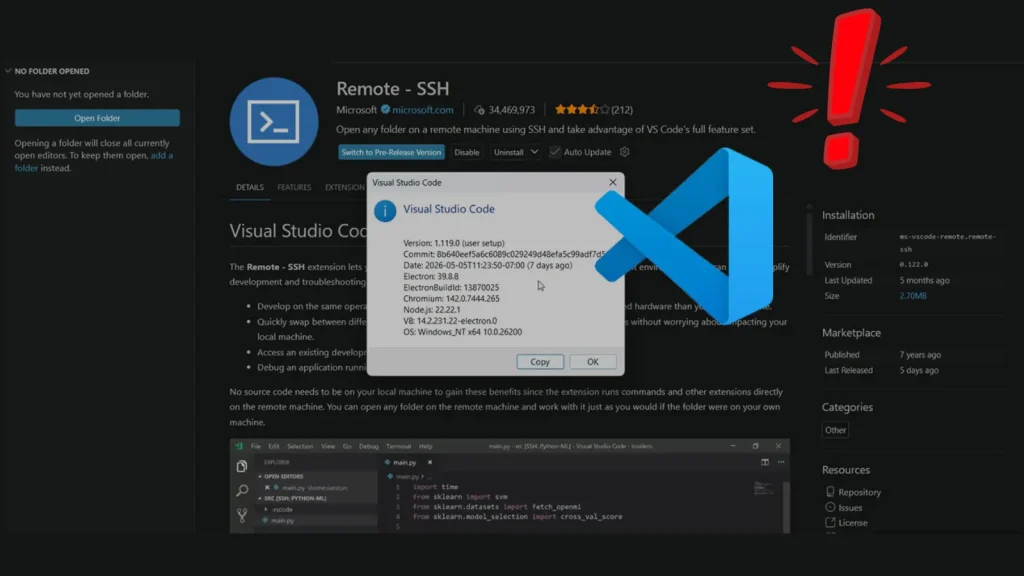
Introduction: The Hidden Bridge to Your Cloud – VS Code Remote-SSH RCE The modern software development landscape is increasingly distributed, with developers often connecting [...]
The digital landscape is a constant battleground, and threat actors are perpetually refining their tactics. A particularly insidious trend is emerging within Microsoft Teams [...]
Unmasking CVE-2026-9560: A Critical Flaw in OpenVPN Connect for macOS The digital landscape demands unwavering vigilance, especially when it comes to tools designed to secure [...]