How Fortigate Reduces Next-Generation Firewall ROI: Fortinet FortiGate vs. Palo Alto Downtime and Boosts Productivity. In the realm of cybersecurity, safeguarding your enterprise is paramount [...]
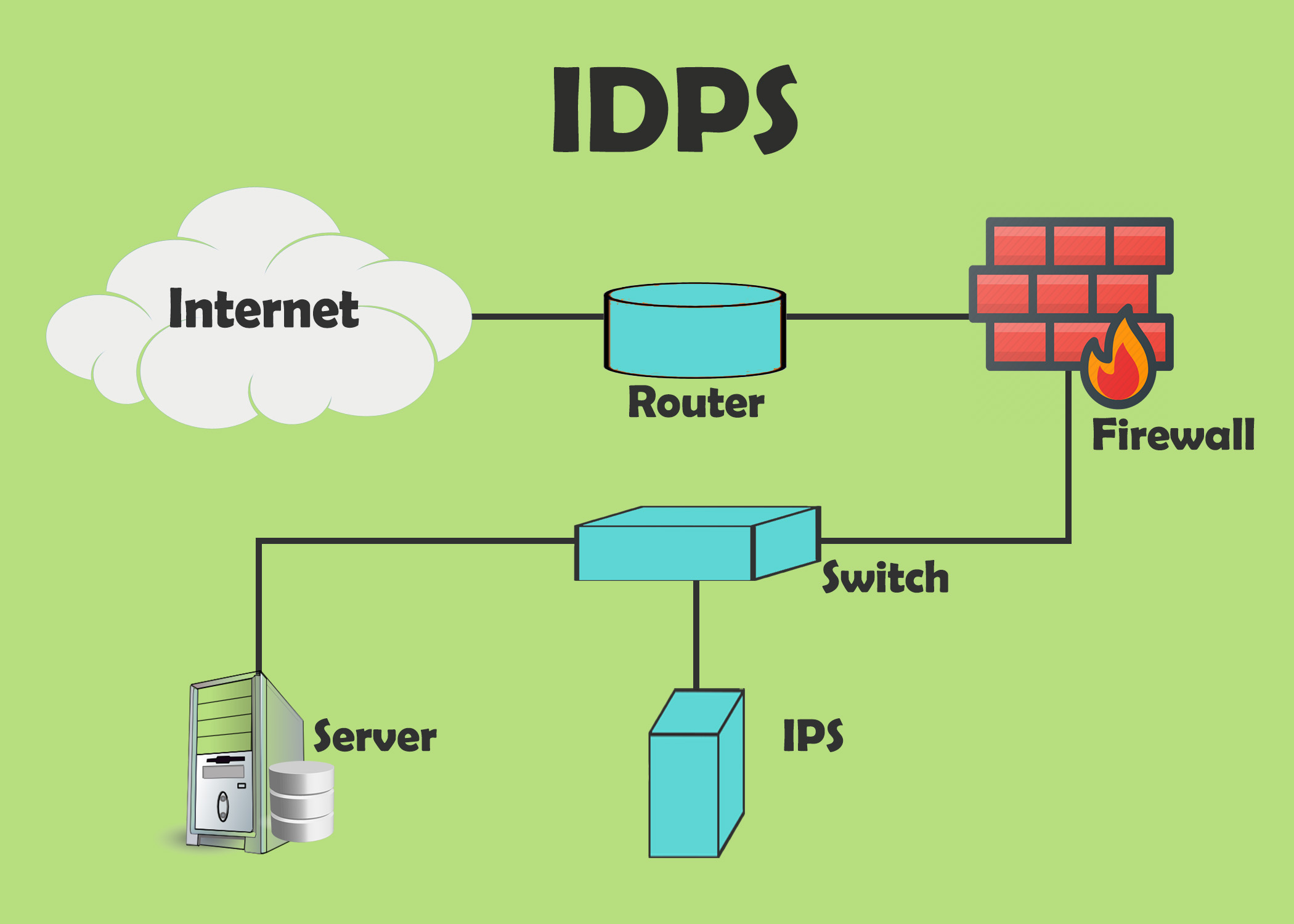
IDS and IPS: Understanding Intrusion Detection and Intrusion Prevention Systems In today’s digital landscape, securing networks against evolving cyber threats is crucial. Intrusion Detection Systems [...]
Evolution of Firewall: From Network Security to Cloud Firewalls In today’s digital landscape, the evolution of firewall technology is crucial for maintaining robust network security [...]
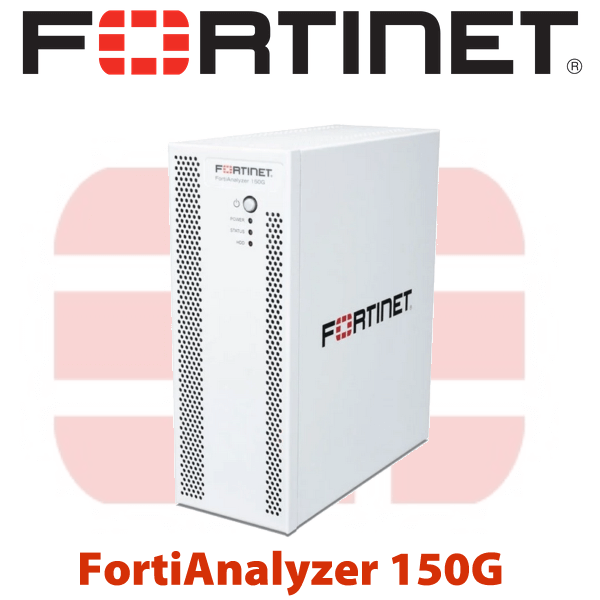
Fortinet: Automation SOC Detection with FortiAnalyzer and FortiSOAR Playbooks Automate Security Team. In today’s rapidly evolving digital landscape, ensuring the security of your enterprise is [...]
In today’s digitally-driven landscape, ensuring robust security measures within your network infrastructure is not just a priority—it’s a necessity for effective cyber security. As businesses [...]
Detailed Comparison of Fortinet Products device: FortiAnalyzer 150G and 200F Upgrade Network Security Document In the ever-evolving landscape of network security, Fortinet stands as a [...]
Network Segmentation in Cybersecurity: What You Need to Know In today’s interconnected world, where data breaches and cyber threats are ever-evolving, implementing effective network segmentation [...]
AI and Machine Learning in Cybersecurity: The Role of AI In today’s interconnected digital landscape, cybersecurity stands as a critical pillar in safeguarding our technological [...]
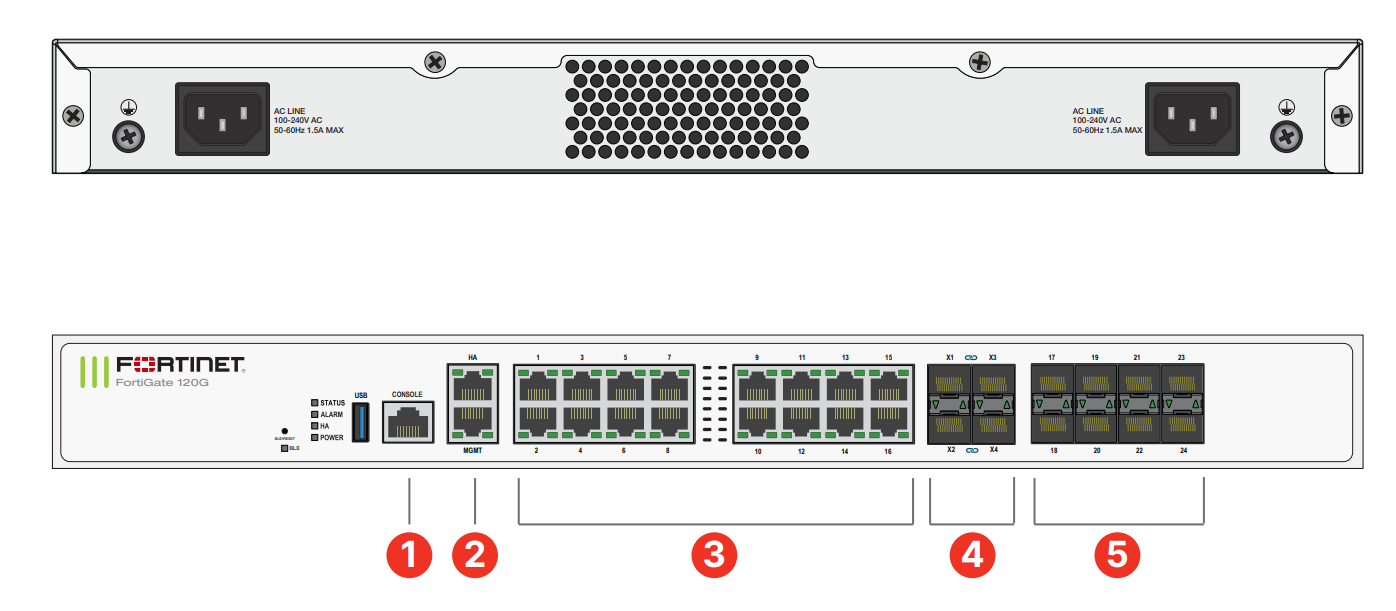
This article provides a comprehensive comparison between Fortinet FortiGate firewall models, specifically focusing on the FortiGate 100F and the 120G. We will delve into their [...]
Troubleshooting IPsec VPN Site-To-Site Connections in FortiGate Firewall Ensuring the robust operation of secure network connections is paramount for any enterprise. This article delves into [...]