How to Protect Your Digital Identities: Ways to Secure Your Digital Life In today’s interconnected world, our digital lives are just as real as our [...]
Email Security Best Practices: How to Secure Your Email System Account In today’s digital age, maintaining robust email security is crucial for safeguarding sensitive information [...]
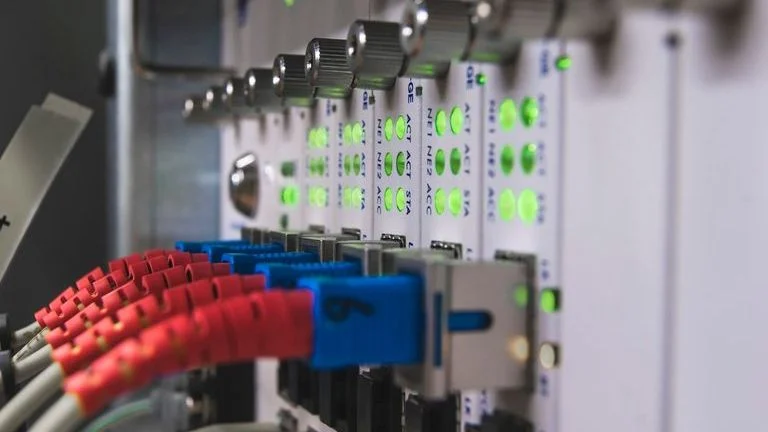
Modbus TCP Vulnerability in Industrial Control System and OT Protocol Exploits The Hidden Risks In the realm of industrial control systems, securing communication protocols is [...]
Insider Threat Detection: How to Detect and Prevention Prevent Insider Threats In today’s digital landscape, protecting sensitive data from both insider threats and external threats [...]
Securing Smart Cities: Internet of Things (IoT) And Infrastructure Challenges in Smart Cities Smart cities represent a significant evolution in urban planning and management, leveraging [...]
Ransomware Attack: Understanding Ransomware Prevention and Response Guide In today’s digital landscape, the threat of a ransomware attack looms large, posing a significant risk to [...]
What is Zero Trust Security Model and How to Implement it and Implement Zero Trust. In an era defined by increasingly sophisticated cyber threats, traditional [...]
How to Choose the right CCTV System: A Camera perfect Guide for your Business Needs In the rapidly evolving landscape of security and surveillance, choosing [...]
Securing Your IoT Device: Internet of Things in Smart Cybersecurity Tips In an increasingly interconnected world, the Internet of Things (IoT) has revolutionized how we [...]
Why AI and Cybersecurity: Best Practices Security for Cyber Incident Response Plans In an era where cyber threats are evolving at an unprecedented pace, the [...]