Bridging the Gap – CISOs and CIOs Driving Tech-Driven Security In today’s hyper-connected business landscape, the convergence of technology and security has never been more [...]
VMware Aria Operations Vulnerability Exposes Systems to Privilege Escalation Attacks VMware has issued a critical security advisory (VMSA-2025-0006) addressing a high-severity local privilege escalation vulnerability [...]
New Ubuntu Security Bypasses Allow Attackers to Exploit Kernel Vulnerabilities Three critical bypasses in Ubuntu Linux’s unprivileged user namespace restrictions allow local attackers to escalate [...]
Microsoft 365 Announces E5 Security for Business Premium Customers as Add-on Microsoft has announced the immediate availability of Microsoft 365 E5 Security as a cost-effective add-on for [...]
TSforge – A New Tool Exploits Every Version of Windows Activation Security researchers from MASSGRAVE have unveiled TSforge, a groundbreaking tool exploiting vulnerabilities in Microsoft’s [...]
New Threat Hunting Technique to Uncover Malicious Infrastructure Using SSL History As internet security evolves, SSL (Secure Sockets Layer) certificates, cornerstones of encrypted communication, are [...]
What is Cryptographic Failures? Cryptographic failures occur when the mechanisms and protocols designed to secure data and communications through encryption break down, become compromised, or [...]
Fortinet Acquired Perception Point to Boost Email Security Fortinet, a global leader in cybersecurity solutions, today announced the completion of its acquisition of Perception Point, [...]
What is Host-based Intrusion Detection System? Organizations face a myriad of challenges in protecting their digital assets. One critical component of a robust security strategy [...]
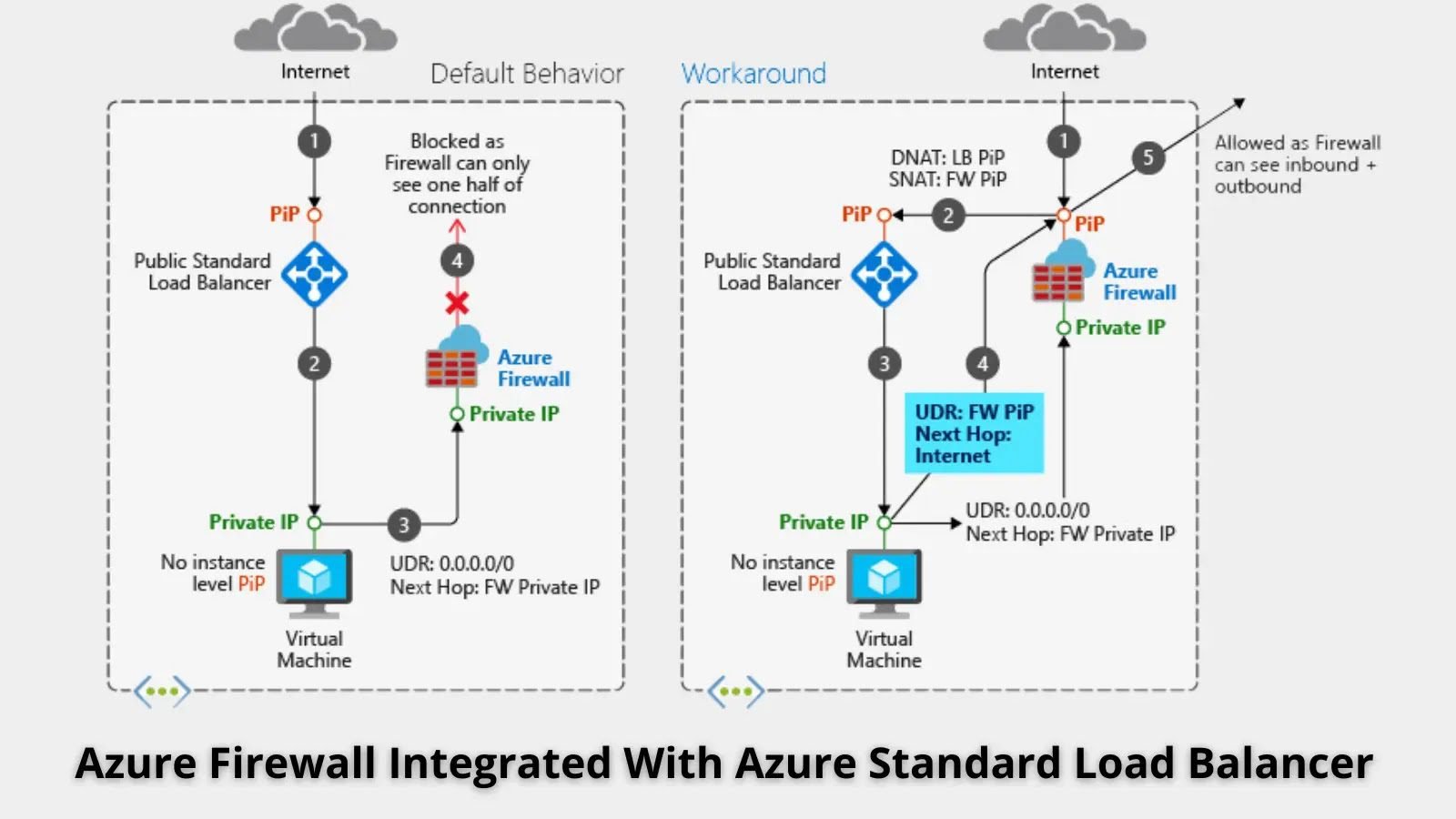
Microsoft Integrates Azure Firewall with Azure Standard Load Balancer to Boost Security Microsoft Azure has unveiled new integration capabilities between Azure Firewall and Azure Standard [...]