What is DDoS?
DDoS stands for “Distributed Denial of Service.” It is a type of cyber-attack in which multiple compromised computers or devices (often referred to as a botnet) are used to flood a target system, network, or service with an overwhelming amount of traffic, requests, or data. The goal of a DDoS attack is to exhaust the target’s resources and make its services unavailable to legitimate users.
How a DDoS Attacks typically works?
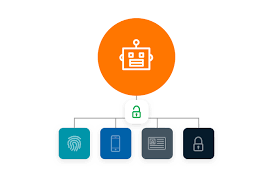
- Botnet Formation: The attackers infect a large number of computers, servers, or IoT devices with malware, turning them into “bots” under their control. These compromised devices are often unaware that they are part of a botnet.
- Command and Control (C&C): The attackers use a centralized command and control infrastructure to communicate with and orchestrate the actions of the botnet. They send instructions to the bots, telling them when and how to launch the attack.
- Attack Initiation: Once the botnet is assembled and instructed, the attack is launched. The bots flood the target with a massive amount of traffic or requests. This could be in the form of a high volume of data packets sent to a server, excessive requests to a web application, or other methods to overwhelm the target’s resources.
- Impact: The target’s resources become overloaded, and it struggles to handle the massive influx of traffic. As a result, legitimate users trying to access the target’s services experience slow response times or complete unavailability.
Types of DDoS Attacks: There are various types of DDoS attacks, including:
- Volumetric Attacks: Overwhelming the target with a high volume of traffic or data.
- TCP/UDP Floods: Sending a large number of TCP or UDP packets to saturate the target’s network capacity.
- HTTP Floods: Overloading a web server with a large number of HTTP requests.
- DNS Amplification: Abusing open DNS servers to generate a massive amount of DNS responses, amplifying the attack traffic.
5. Duration and Complexity: DDoS attacks can vary in duration and complexity. Some attacks may be short-lived bursts, while others can be prolonged and sustained, lasting for hours or even days. Some DDoS attacks may involve multiple attack vectors simultaneously to further increase the impact.
How DDoS attacks on IoT Devices?
DDoS (Distributed Denial of Service) attacks on IoT (Internet of Things) devices have become a significant concern due to the proliferation of IoT devices and their often inadequate security measures. DDoS attacks target IoT devices and use them as part of a botnet to launch large-scale, coordinated attacks against specific targets, overwhelming their resources and causing service disruptions. Here’s how DDoS attacks on IoT devices work and the impact they can have:
- Botnet Formation: Cybercriminals identify vulnerable IoT devices with weak security controls, default credentials, or unpatched vulnerabilities. They infect these devices with malware, turning them into “bots” under their control. The infected devices collectively form a botnet, which is a network of compromised devices ready to carry out the attack.
- Attack Initiation: Once the botnet is assembled, the attacker sends a command to all the compromised IoT devices, instructing them to flood a target server or network with a massive volume of requests or traffic. This overwhelms the target’s resources, causing it to become unreachable or significantly slow down.
- Amplification Techniques: Some DDoS attacks use amplification techniques where small requests are sent to publicly accessible services (e.g., DNS, NTP) that, in turn, generate large responses to the victim’s IP address. This amplifies the attack’s impact, making it more difficult to mitigate.
- Impact: DDoS attacks on IoT devices can have severe consequences, including:
- Service Disruptions: The targeted server or network becomes overwhelmed, leading to service unavailability for legitimate users.
- Financial Loss: Service disruptions can lead to financial losses for businesses that rely on their online presence to generate revenue.
- Reputation Damage: Organizations that suffer from prolonged DDoS attacks may face reputational damage, loss of customer trust, and negative publicity.
- Data Breach Risk: DDoS attacks might serve as a smokescreen for other cyber-attacks, such as data breaches, that occur simultaneously, taking advantage of the chaos caused by the DDoS attack.
5. Challenges in Mitigation: Mitigating DDoS attacks on IoT devices can be challenging due to the following reasons:
- Device Diversity: IoT devices come in various shapes, sizes, and platforms, making it difficult to develop universal security measures.
- Resource Constraints: Many IoT devices have limited processing power, memory, and battery life, making them less capable of running sophisticated security software.
- Proliferation: The sheer number of IoT devices makes it challenging to monitor and control all of them effectively.
- Lack of Awareness: Many IoT device owners may be unaware of the security risks and may not take appropriate steps to secure their devices.
To address the DDoS threat on IoT devices, manufacturers must implement robust security measures in their devices, including secure boot processes, regular firmware updates, strong authentication mechanisms, and encryption for data in transit and at rest. Users should also be educated about the importance of securing their IoT devices and following best practices to protect against DDoS attacks. Additionally, network operators can deploy DDoS mitigation solutions to identify and block malicious traffic before it reaches the target.