Lazarus Hackers Attacking macOS Users With ‘Mach-O Man’ Malware Kit
A disturbing new development has emerged from North Korea’s state-sponsored threat actor, the Lazarus Group. Known for their audacious cyber campaigns, they have now set their sights firmly on macOS users, deploying a sophisticated, multi-stage malware kit dubbed “Mach-O Man.” This campaign is not indiscriminate; it meticulously targets high-value individuals, specifically fintech executives, cryptocurrency developers, and other critical enterprise personnel.
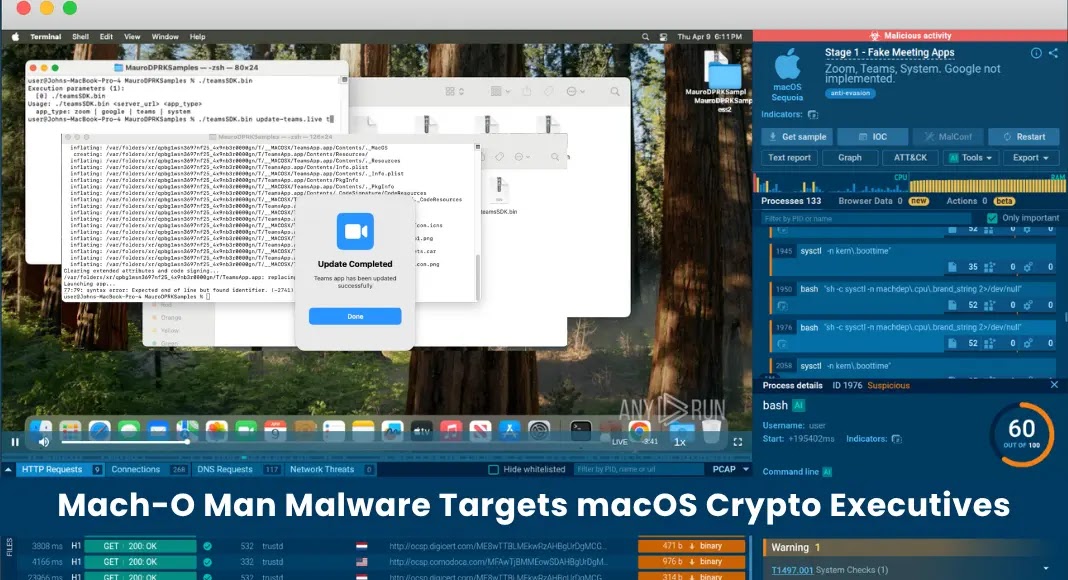
The discovery, meticulously analyzed by Mauro Eldritch in collaboration with ANY.RUN’s interactive sandbox platform, reveals a significant escalation in the Lazarus Group’s capabilities and their determined effort to penetrate what is often perceived as a more secure operating system. Understanding the intricacies of Mach-O Man is paramount for defenders of macOS environments.
Understanding Mach-O Man: A Four-Stage Attack Chain
Mach-O Man represents a highly modular and complex threat, designed to bypass traditional security measures and establish persistent control. Its effectiveness lies in its four-stage attack chain, each phase carefully crafted to advance the adversary’s objectives. The initial vector for this sophisticated intrusion typically involves highly tailored social engineering lures, specifically fake meeting invitations designed to entice unsuspecting targets.
Once activated, the malware, notably compiled in Go, leverages a series of interconnected components to achieve its nefarious goals. This modularity allows the Lazarus Group to adapt quickly and maintain stealth, making detection and eradication significantly more challenging. The use of Go, a increasingly popular choice for malware developers, further highlights the group’s commitment to modern and versatile toolsets.
Lazarus Group’s Evolving Threat Landscape
The Lazarus Group, also known as APT38, Hidden Cobra, and Guardians of Peace, has a well-documented history of engaging in financially motivated cyberattacks, often in support of the North Korean regime’s objectives. Their past campaigns have ranged from bank heists to cryptocurrency theft, demonstrating a persistent and adaptive threat. The shift towards a dedicated macOS malware kit like Mach-O Man underscores their strategic intent to broaden their attack surface and exploit new avenues for financial gain and espionage.
This particular campaign against macOS users, targeting individuals within the fintech and crypto sectors, aligns perfectly with the Lazarus Group’s historical focus on high-value financial targets. The potential for significant financial gain from these compromised executives and developers presents a compelling motivation for such a sophisticated and resource-intensive operation.
Remediation Actions and Proactive Defenses
Given the advanced nature of the Mach-O Man malware and the sophistication of the Lazarus Group, a multi-layered approach to cybersecurity is essential for macOS users, particularly those identified as high-value targets. Proactive measures and immediate remediation actions are critical to mitigate the risk posed by this threat.
- Implement Robust Email Filtering and User Education: Strengthen email security gateways to filter out malicious attachments and links. Crucially, conduct regular security awareness training, emphasizing the dangers of social engineering, especially fake meeting invitations and unexpected attachments from unfamiliar senders.
- Maintain Current Operating Systems and Software: Regularly apply security updates and patches for macOS and all installed applications. This helps to close known vulnerabilities that attackers, including the Lazarus Group, might exploit.
- Deploy Advanced Endpoint Detection and Response (EDR): Utilize EDR solutions capable of behavioral analysis and anomaly detection on macOS. Traditional signature-based antivirus alone may not be sufficient against sophisticated, modular malware like Mach-O Man.
- Enforce Principle of Least Privilege: Limit user permissions to only what is necessary for their roles. This can restrict the damage an attacker can inflict even if they successfully compromise an account.
- Network Segmentation and Monitoring: Implement network segmentation to isolate critical assets and monitor network traffic for suspicious activity, including unusual outbound connections or lateral movement indicative of compromise.
- Regular Backups and Disaster Recovery: Maintain frequent, secure backups of all critical data. Ensure a tested disaster recovery plan is in place to minimize downtime and data loss in the event of a successful attack.
Tools for Detection and Mitigation
Effective defense against threats like Mach-O Man requires a combination of robust security practices and advanced tooling. Here are some relevant tools that can aid in detection, scanning, and mitigation:
| Tool Name | Purpose | Link |
|---|---|---|
| Virustotal | Comprehensive malware analysis through multiple antivirus engines. | https://www.virustotal.com/ |
| ANY.RUN | Interactive online sandbox for dynamic malware analysis. | https://any.run/ |
| Osquery | Operating system instrumentation framework for low-level monitoring. | https://osquery.io/ |
| YARA Rules | Pattern matching tool for identifying and classifying malware. | https://virustotal.github.io/yara/ |
Conclusion: Heightened Vigilance for macOS Users
The emergence of Mach-O Man serves as a stark reminder that no operating system is impervious to determined and well-resourced adversaries. The Lazarus Group’s targeted campaign against macOS users, especially those in financially sensitive sectors, demands immediate attention and a proactive security posture. Organizations and individuals must understand the sophisticated nature of this threat, bolster their defenses, and prioritize continuous security education to counteract the evolving tactics of state-sponsored threat actors.





