FBI Sounds Alarm: Kali365 Unleashes Advanced Phishing on Microsoft 365 Users The Federal Bureau of Investigation (FBI) has issued a critical cybersecurity warning regarding a [...]
CISA Sounds the Alarm: Trend Micro Apex One Vulnerability Actively Exploited The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued a critical warning, adding [...]
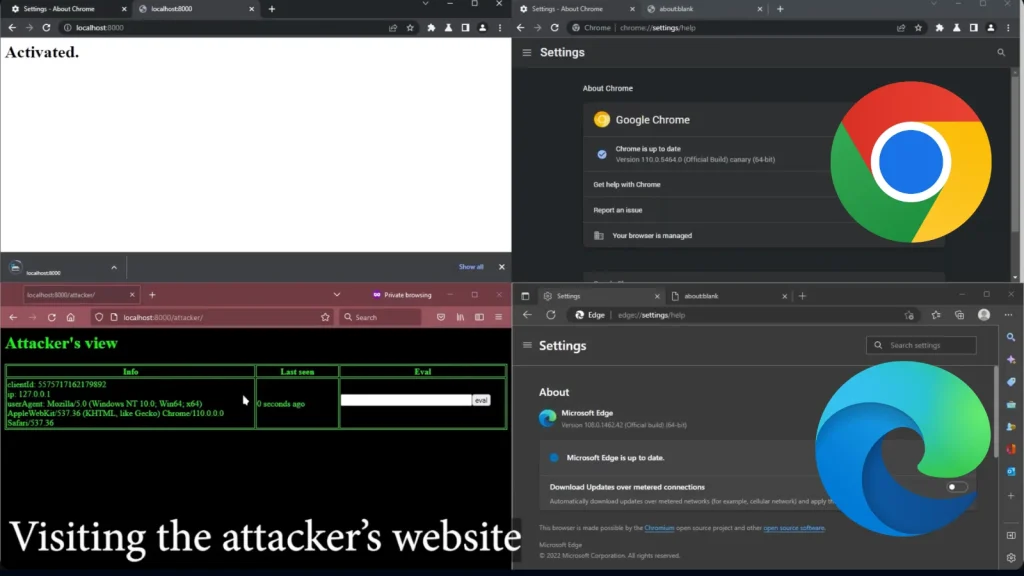
Google Drops Zero-Day Exploit: Unpatched Chromium Bug Threatens Millions In a rare and concerning move, Google has publicly released proof-of-concept (PoC) exploit code for a [...]
In a concerning development for the integrity of the software supply chain, a threat actor with suspected links to North Korea has been observed actively [...]
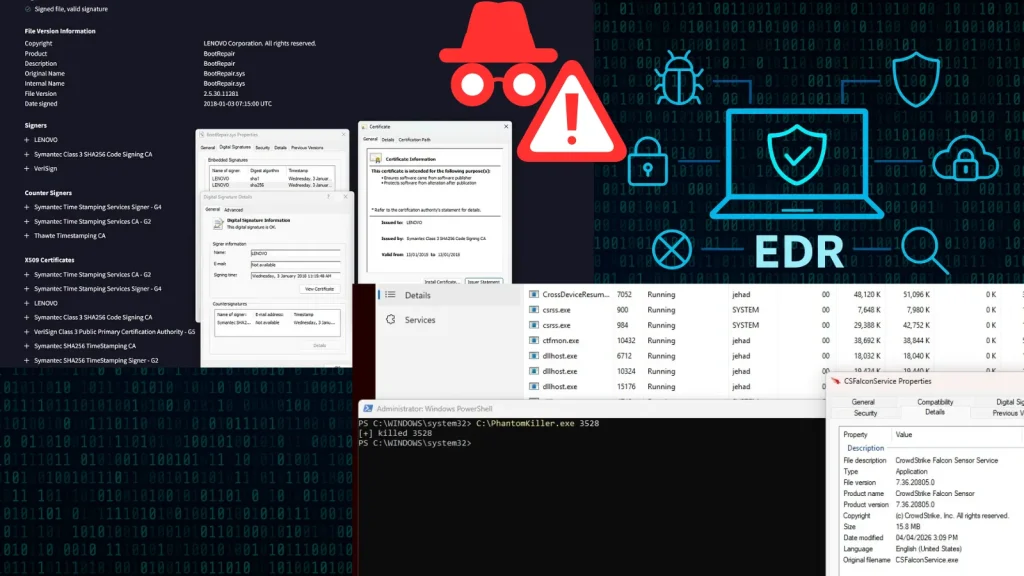
A disturbing discovery has emerged from the cybersecurity landscape: threat actors can now weaponize a legitimately signed Lenovo driver to terminate critical Endpoint Detection [...]
The Shai-Hulud Maneuver: npm Forcibly Resets Bypass-2FA Tokens Amid Supply Chain Attack In the intricate landscape of modern software development, the integrity of package [...]
Unveiling Flipper One: A New Era for Open-Source Cyberdecks The cybersecurity landscape is constantly evolving, pushing the boundaries of what’s possible for researchers, developers, [...]
The open-source software ecosystem, a cornerstone of modern development, is often seen as a beacon of collaboration and innovation. Yet, even in its most trusted [...]
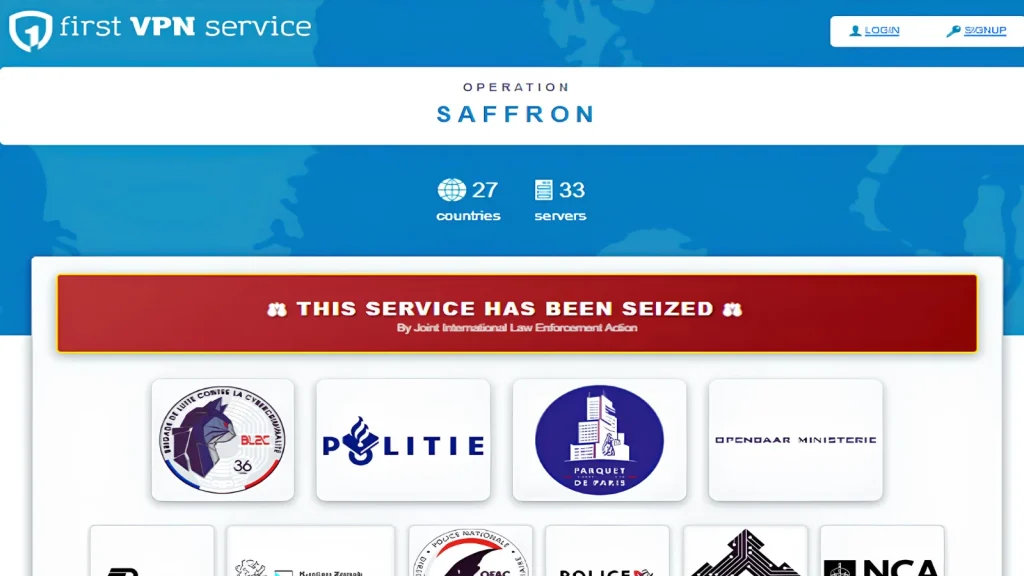
Shuttering First VPN: A Landmark Blow Against Ransomware Infrastructure In a significant victory for international law enforcement, a criminal virtual private network (VPN) known as [...]
An urgent security warning has been issued for Google Chrome users. Google has rolled out a critical update addressing 16 security vulnerabilities, two of [...]