The academic aspirations of millions of Indian students are being exploited by a new, insidious cyber threat. What began as a promise of educational [...]
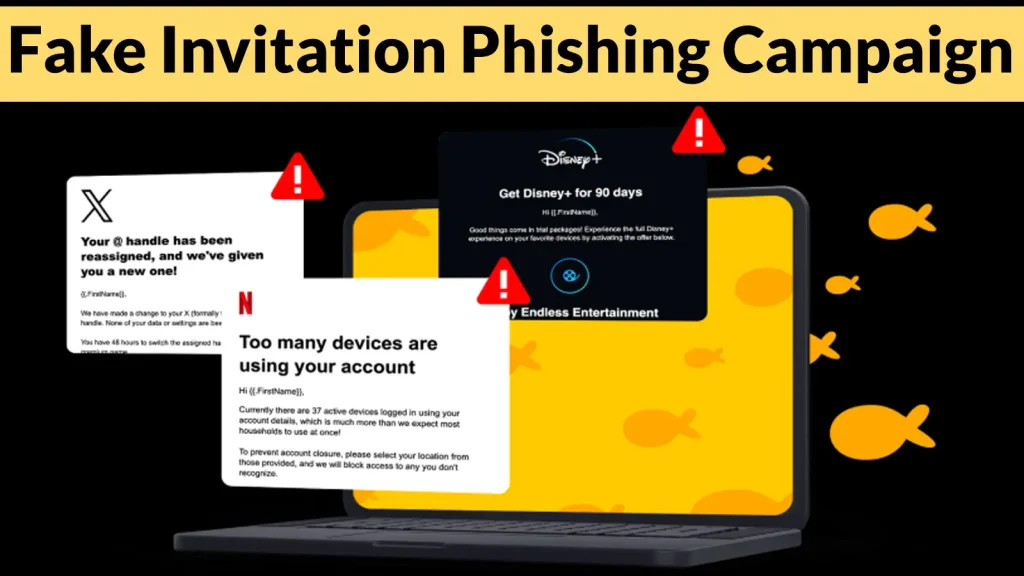
In the relentless battle against cyber threats, a new alarm has sounded for U.S. organizations. A sophisticated and extensive phishing campaign is actively exploiting [...]
A new and insidious threat is quietly spreading across the digital landscape, masquerading as the very tools designed to enhance productivity. Organizations and individuals [...]
The Silent Threat: Fake Microsoft Teams Downloads Deploy ValleyRAT Malware In the evolving landscape of cyber threats, even the most trusted applications can become [...]
On May 18, 2026, the cybersecurity landscape witnessed a stark reminder of the escalating dangers within the software supply chain. A sophisticated, automated offensive, [...]
Discord Elevates Privacy: End-to-End Encryption Now Default for Voice and Video The landscape of digital communication security just took a significant leap forward. Discord, [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 ‘Mini Shai-Hulud’ Supply Chain Attack Campaign Targeting Open-Source Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: Critical Overview [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Denial of Service Vulnerability in Wireshark Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: MEDIUM Software Affected Wireshark [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 SQL Injection Vulnerability in Drupal Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: CRITICAL Software Affected Drupal core [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in Microsoft Products Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Software Affected Windows 10: [...]