Unmasking CVE-2026-3991: Symantec DLP Agent’s Privilege Escalation Threat In the intricate landscape of enterprise security, Data Loss Prevention (DLP) solutions stand as critical bastions against [...]
Urgent Alert: Critical Cisco IMC Vulnerability (CVE-2026-20093) Allows Authentication Bypass A severe security vulnerability has recently come to light, impacting Cisco’s Integrated Management Controller (IMC). [...]
The digital landscape is a battleground, and even the most ubiquitous brands aren’t immune to attack. Starbucks, a global coffee giant, has reportedly fallen victim [...]
Navigating the Digital Wilderness: Choosing the Best VPN for Privacy in 2026 The landscape of online privacy is constantly shifting. With data breaches and [...]
Unveiling Tomorrow’s Digital Forensics: The Top 20 Tools for 2026 The landscape of cybercrime is in constant flux, demanding equally adaptive and sophisticated investigative [...]
Russian Hackers Deploying ‘CTRL’ Remote Access Toolkit in RDP Hijacking Campaigns In a significant development for cybersecurity professionals, a newly identified remote access toolkit [...]
The digital landscape often feels like a constant high-stakes chase, and today, that chase leads directly to your web browser. Google has just issued [...]
Artificial intelligence agents are rapidly integrating into enterprise operations, dramatically enhancing efficiency and enabling innovative solutions. However, this transformative technology also introduces sophisticated new attack [...]
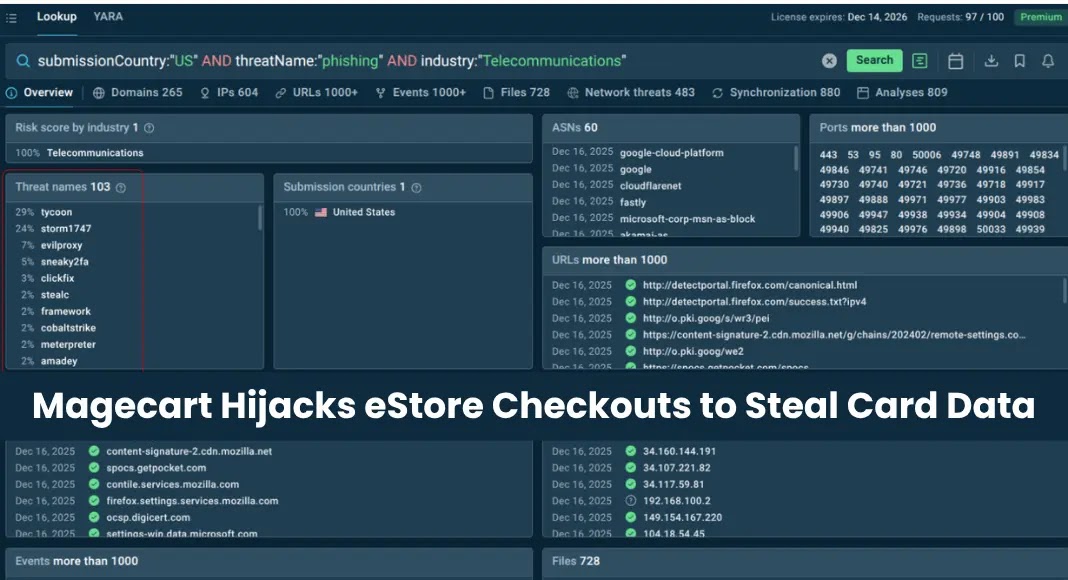
The Silent Threat: Magecart’s Persistent Attack on e-Commerce Checkouts For over two years, a highly sophisticated and persistent Magecart campaign has silently compromised online [...]
Microsoft Teams to Enhance Privacy by Removing EXIF Data from Shared Images In a significant step towards bolstering enterprise privacy and operational security, Microsoft [...]