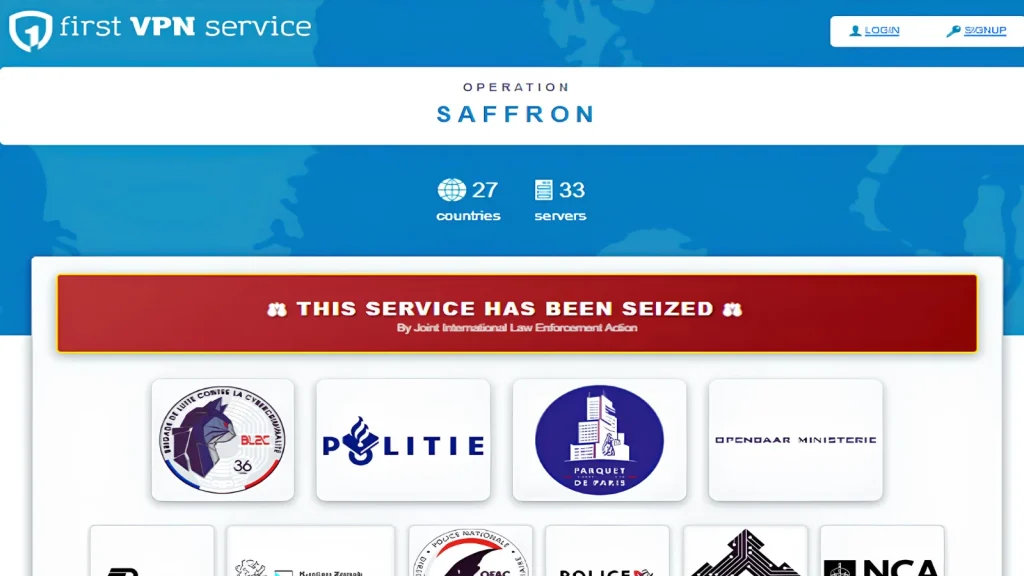
Shuttering First VPN: A Landmark Blow Against Ransomware Infrastructure In a significant victory for international law enforcement, a criminal virtual private network (VPN) known as [...]
An urgent security warning has been issued for Google Chrome users. Google has rolled out a critical update addressing 16 security vulnerabilities, two of [...]
The academic aspirations of millions of Indian students are being exploited by a new, insidious cyber threat. What began as a promise of educational [...]
In the relentless battle against cyber threats, a new alarm has sounded for U.S. organizations. A sophisticated and extensive phishing campaign is actively exploiting [...]
A new and insidious threat is quietly spreading across the digital landscape, masquerading as the very tools designed to enhance productivity. Organizations and individuals [...]
The Silent Threat: Fake Microsoft Teams Downloads Deploy ValleyRAT Malware In the evolving landscape of cyber threats, even the most trusted applications can become [...]
On May 18, 2026, the cybersecurity landscape witnessed a stark reminder of the escalating dangers within the software supply chain. A sophisticated, automated offensive, [...]
Discord Elevates Privacy: End-to-End Encryption Now Default for Voice and Video The landscape of digital communication security just took a significant leap forward. Discord, [...]
The landscape of cyber threats is in constant flux, and few developments are as concerning as the evolution of established botnets to target cloud-native [...]
The Unseen Threat: How a Weaponized VS Code Extension Breached GitHub’s Internal Repositories On May 18, 2026, the cybersecurity landscape was reminded of a critical [...]