Urgent Alert: New Microsoft Defender Zero-Days Under Active Exploitation The cybersecurity landscape has been rocked by the disclosure of two critical zero-day vulnerabilities in Microsoft [...]
In the relentlessly evolving landscape of cybersecurity, a critical vulnerability has emerged, casting a significant shadow over organizations relying on Cisco Secure Workload. A newly [...]
Urgent Alert: Highly Critical Drupal Core Vulnerability Threatens Global Websites A significant security alert is on the horizon for countless websites globally, as Drupal [...]
Unmasking BadIIS: How This Malware Hijacks Your IIS Servers and Redirects Users Imagine your meticulously crafted website, built on a robust Internet Information Services [...]
A disturbing discovery has sent ripples through the cybersecurity community: a critical zero-day Remote Code Execution (RCE) vulnerability, ominously dubbed “nginx-poolslip,” has been identified in [...]
In the relentless landscape of cyber threats, ransomware continues its evolution, constantly finding new vectors to compromise systems and extort organizations. A recent and particularly [...]
The integrity of the digital ecosystem relies on trust and ethical conduct. However, a recent case highlights how sophisticated actors exploit vulnerabilities—not in software, but [...]
Within many Security Operations Centers (SOCs), a subtle yet significant inefficiency often lurks, quietly draining resources and delaying critical responses. This isn’t a flashy zero-day [...]
Mobile banking applications have become indispensable, offering unparalleled convenience. Yet, this convenience comes with a heightened risk, as sophisticated malware constantly evolves to exploit vulnerabilities. [...]
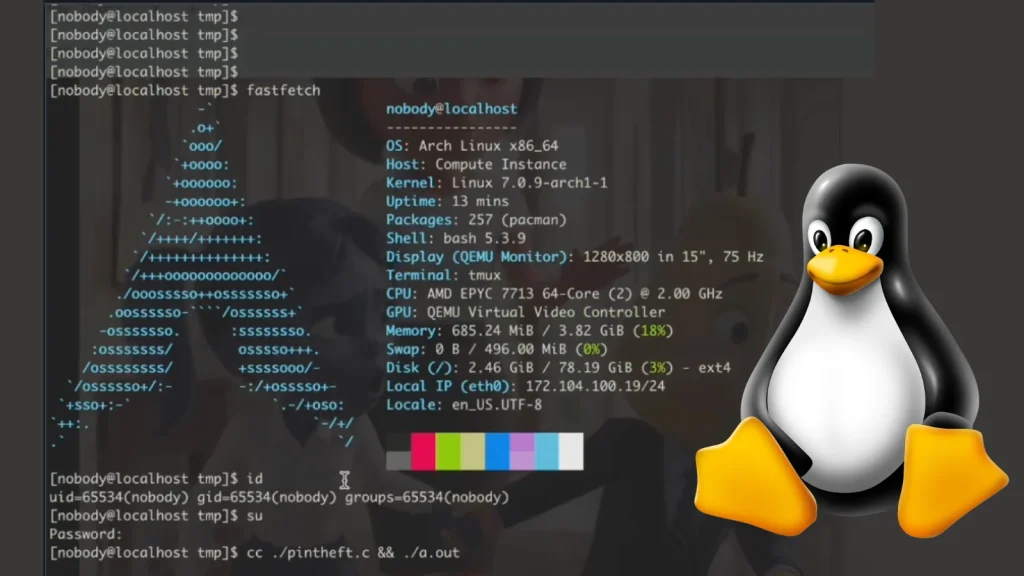
PinTheft Linux Vulnerability: When Local Access Becomes Root Access In the evolving landscape of cybersecurity, local privilege escalation (LPE) vulnerabilities remain a critical concern [...]