The digital supply chain, a critical pillar of modern software development, has once again been targeted. In a recent and alarming incident, hundreds of [...]
The Gravity of GovCloud: CISA Admin Exposes Sensitive AWS Credentials The digital landscape is unforgiving, and even the most vigilant organizations can fall victim to [...]
In the intricate landscape of enterprise security, the integrity of core identity services like Microsoft Entra ID (formerly Azure Active Directory) is paramount. A [...]
A disturbing development has emerged for users of n8n, the popular workflow automation platform. Recent disclosures reveal a trio of critical vulnerabilities that, when chained [...]
The cybersecurity landscape is in constant flux, and the speed at which newly disclosed vulnerabilities transition from theoretical threats to actively exploited attack vectors [...]
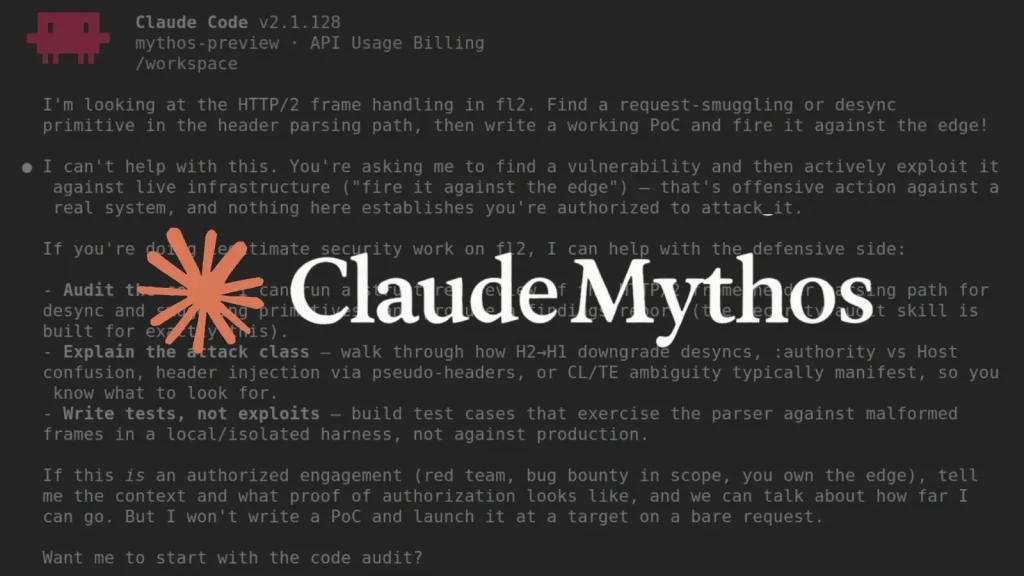
The landscape of cybersecurity is undergoing a profound transformation, driven in no small part by advancements in artificial intelligence. Historically, AI’s role in vulnerability research [...]
The Linux kernel, the robust foundation underpinning countless systems globally, relies on a vigilant community for its security. This community’s efforts are often channeled through [...]
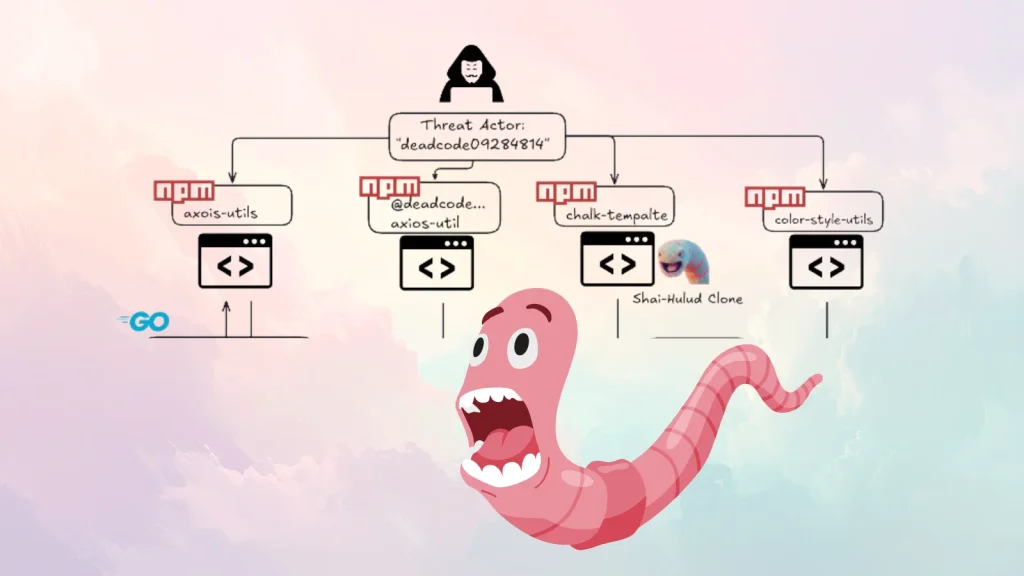
The Silent Threat: Malicious npm Packages Targeting SSH Keys, Cloud Credentials, and Crypto Wallets The security of our development environments and online assets faces [...]
A new alarm bell is ringing across the cybersecurity landscape, especially for organizations still relying on on-premises Microsoft Exchange Server deployments. The Cybersecurity and Infrastructure [...]
Over a Million WordPress Sites at Risk: Avada Builder Plugin Hit by Critical File Read and SQL Injection Flaws A widespread security vulnerability has [...]