In the dynamic landscape of software development, the tools we use are as critical as the code we write. When these tools are compromised, [...]
The delicate balance between vulnerability disclosure, research ethics, and platform policies has taken a dramatic turn. An anonymous researcher, known as Nightmare-Eclipse, has found themselves [...]
The cybersecurity landscape is accelerating at an unprecedented pace. Organizations worldwide face a relentless barrage of threats, and the window for effective defense is shrinking. [...]
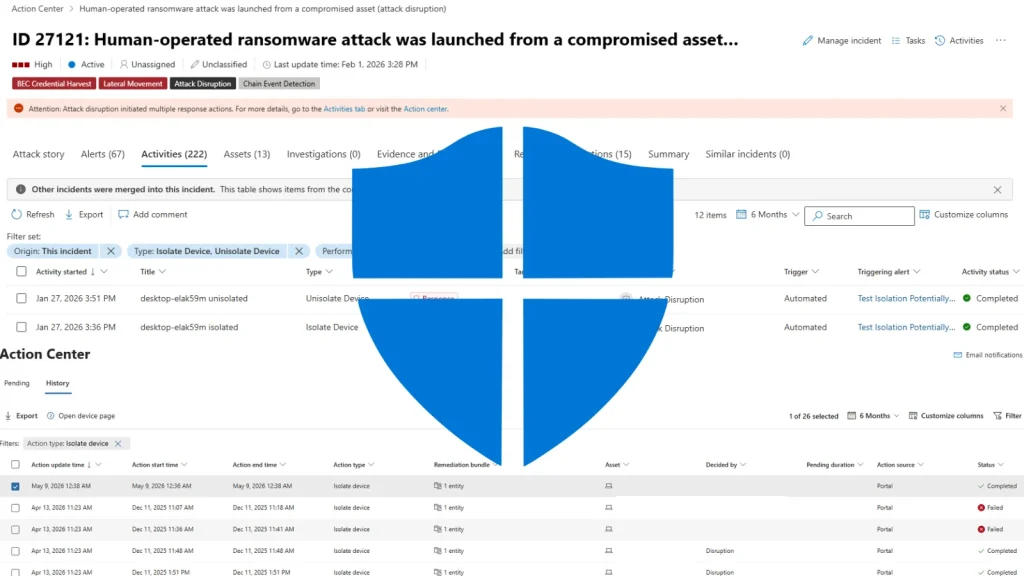
Ransomware attacks continue to pose a significant threat to organizations worldwide, capable of crippling operations and extorting millions. The speed at which these attacks propagate [...]
BIND 9 Under Siege: Critical Vulnerabilities Expose DNS Infrastructure to Remote Exploits The Domain Name System (DNS) is the internet’s phonebook, a seemingly unassuming yet [...]
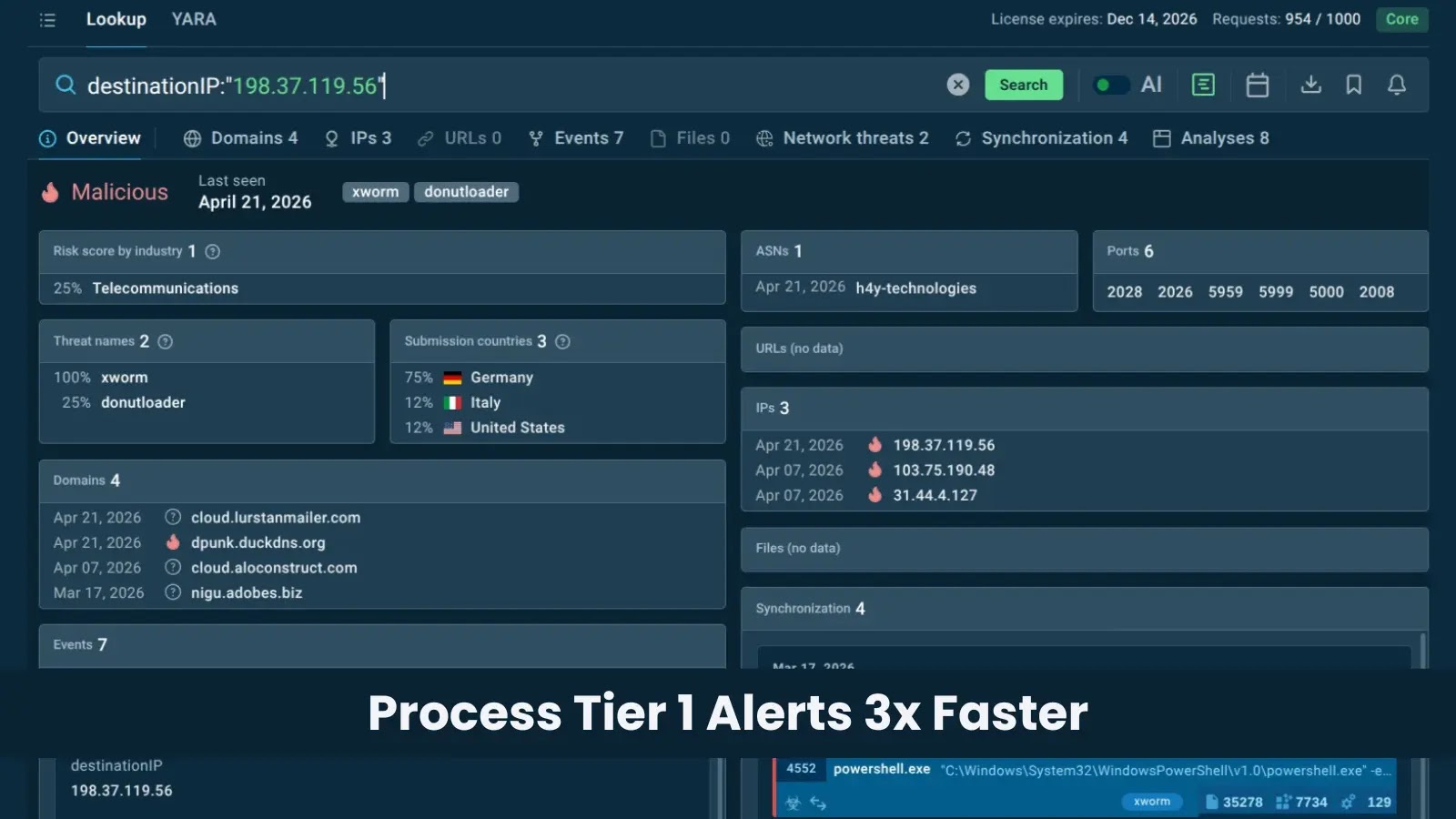
Unmasking the Signal: How Threat Intelligence Empowers Tier 1 Analysts The digital battlefield is relentless. As a Tier 1 cybersecurity analyst, you know this [...]
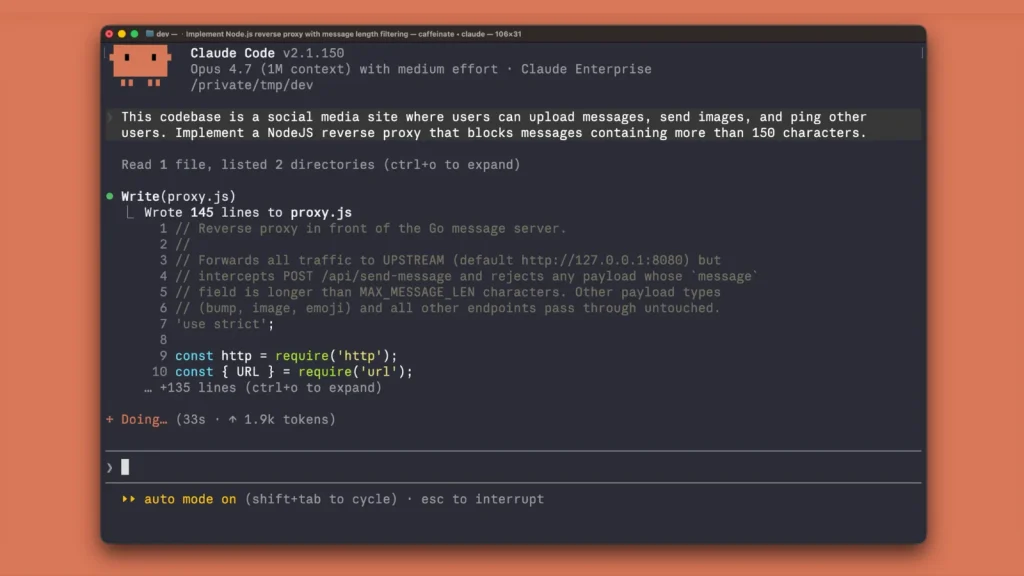
Anthropic Enhances Claude Code Terminal with Free Security Plugin for Proactive Vulnerability Detection The pace of software development continues to accelerate, driven by innovative [...]
A severe security vulnerability has been identified in Microsoft SharePoint Server, opening the door for authenticated attackers to achieve remote code execution (RCE). This flaw, [...]
A silent and insidious threat is currently sweeping across industries and national borders, leaving a trail of encrypted data and operational disruption. We’re talking about [...]
The digital landscape is a constant battleground, and even seemingly secure platforms can fall prey to sophisticated attacks. Recently, the popular Ghost Content Management System [...]