The digital landscape is a constant battleground, and national security extends far beyond physical borders. In a significant move to safeguard American networks, the Federal [...]
The Invisible Hand: How APT Hackers Exploit RDP for Critical Infrastructure Infiltration The digital landscape is under constant siege, a truth starkly reinforced by [...]
The Unseen Threat: Google Forms Weaponized in Multi-Stage PureHVNC Campaign In an alarming development, threat actors have leveraged one of the most ubiquitous and [...]
Unveiling Kali Linux 2026.1: Eight New Tools for the Modern Pen Tester The cybersecurity landscape demands constant evolution, and for penetration testers, the tools [...]
Tycoon2FA’s Resurgence: A Persistent Threat to Cloud Accounts The digital landscape often feels like a constant game of cat and mouse, and recent events involving [...]
Larva-26002 Targets MS-SQL Servers with New ICE Cloud Scanner: What You Need to Know Microsoft SQL (MS-SQL) servers are a cornerstone of countless organizational [...]
The landscape of cyber warfare just intensified dramatically. A new and particularly aggressive destructive payload, dubbed CanisterWorm, has been deployed by the threat actor TeamPCP, [...]
When the Protectors Need Protecting: HackerOne Employees Affected by Navia Data Breach The very organizations dedicated to hardening our digital defenses are not immune [...]
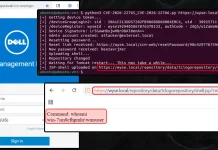
Navigating the Dell Wyse Management Vulnerabilities: A Path to Complete System Compromise The digital landscape is a constant battleground, and even seemingly minor chinks [...]
A disturbing development has sent ripples through the cybersecurity community: the widely trusted open-source vulnerability scanner, Aqua Security’s Trivy, has been compromised in a [...]