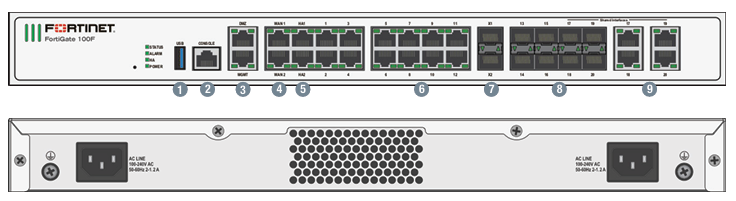
The Fortigate 100F Firewall stands as a robust solution in the realm of network and security, designed to protect organizations from an ever-evolving landscape of [...]
Cisco AnyConnect VPN Server Vulnerability Let Attackers Trigger DoS Attack A critical security vulnerability affecting Cisco Meraki MX and Z Series devices could allow unauthenticated [...]
Hackers Actively Exploiting Zyxel RCE Vulnerability Via UDP Port A significant spike was observed in exploitation attempts targeting CVE-2023-28771, a critical remote code execution vulnerability affecting [...]
Palo Alto Networks PAN-OS Vulnerability Enables Admin to Execute Root User Actions A critical command injection vulnerability in Palo Alto Networks PAN-OS operating system enables [...]
Cisco ISE Vulnerability Allows Remote to Access Sensitive Data – PoC Exploit Available A critical vulnerability affecting its Identity Services Engine (ISE) when deployed on major cloud [...]
VMware NSX XSS Vulnerability Allows Attackers to Inject Malicious Code Multiple Cross-Site Scripting (XSS) vulnerabilities in the VMware NSX network virtualization platform could allow malicious [...]
New HTTPBot Botnet Expanding Aggressively to Attack Windows Machines A new botnet family named HTTPBot has emerged as a critical threat to the Windows ecosystem, [...]
Ivanti Connect Secure RCE Vulnerability Actively Exploited in the Wild – Apply Patch Now! Ivanti has disclosed a critical vulnerability, CVE-2025-22457, affecting its Connect Secure, [...]
Hackers Actively Targeting SonicWall, Zoho, F5 & Ivanti Systems to Exploit Vulnerabilities A significant surge in cyberattacks targeting enterprise network appliances and remote access [...]
New Sophisticated Linux-Backdoor Attacking OT Systems Exploiting 0-Day RCE A sophisticated Linux-based backdoor dubbed “OrpaCrab” has emerged as a significant threat to operational technology (OT) [...]