Unmasking ‘Sploitlight’: A Critical macOS Vulnerability Bypassing TCC Protections A disturbing revelation has emerged for macOS users: a critical vulnerability, aptly named “Sploitlight,” has [...]
The rapid adoption of generative AI tools like ChatGPT and Google Gemini has revolutionized various industries, offering unprecedented capabilities in content creation, data analysis, and [...]
Singapore’s critical infrastructure is under siege. A highly sophisticated and persistent cyber threat, known as UNC3886, has been systematically targeting the nation’s most vital [...]
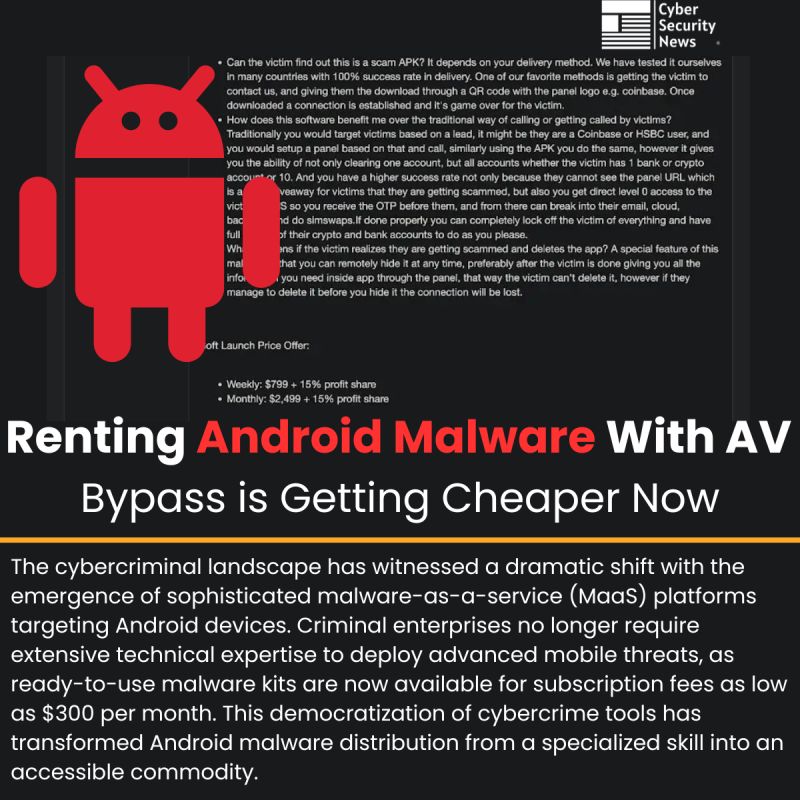
The Lucrative Business of Android Malware-as-a-Service: 2FA Interception and AV Bypass on Demand The barrier to entry for cybercrime has never been lower. A [...]
The digital arteries of modern society run on robust telecommunications infrastructure. When a giant like Orange, France’s leading telecom provider, announces a significant cyberattack, [...]
In the intricate tapestry of modern IT infrastructure, virtual machines (VMs) are foundational. They offer unparalleled flexibility, scalability, and resource optimization. However, this power [...]
The Unpatchable Past: SonicWall SMA100 N-Day Vulnerabilities Exposed In the evolving landscape of cyber threats, the exposure of N-day vulnerabilities, particularly those affecting critical [...]
In the intricate landscape of web application security, the discovery of a critical vulnerability can send ripples across the digital ecosystem, potentially impacting millions [...]
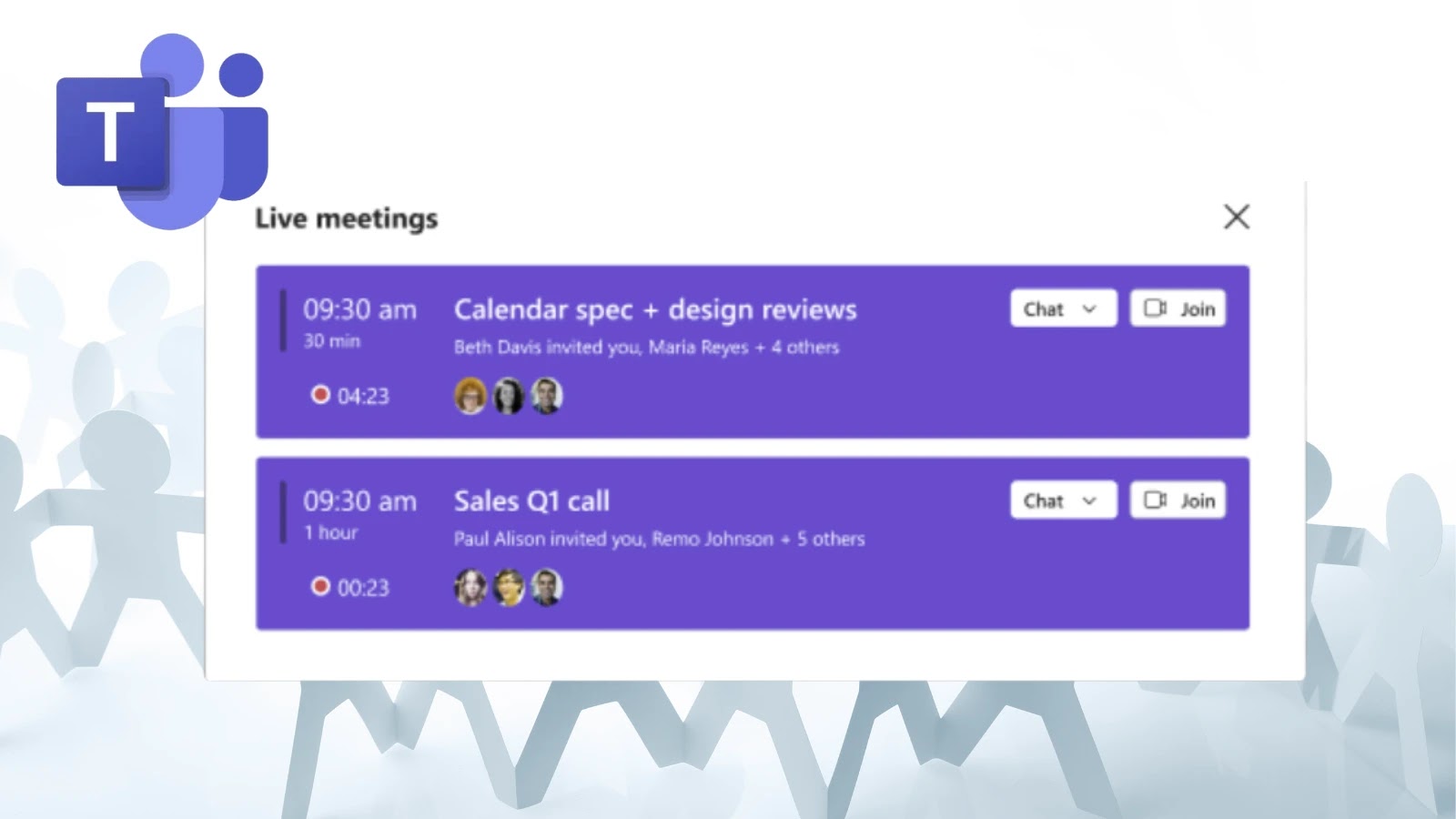
In the fast- paced rhythm of modern enterprise, every minute counts. Delays in meeting startups, often stemming from participants joining late or struggling to [...]
Google Fortifies Chrome with DBSC Open Beta: A New Era for Session Security The digital landscape is a constant battleground, with cybercriminals continually refining [...]